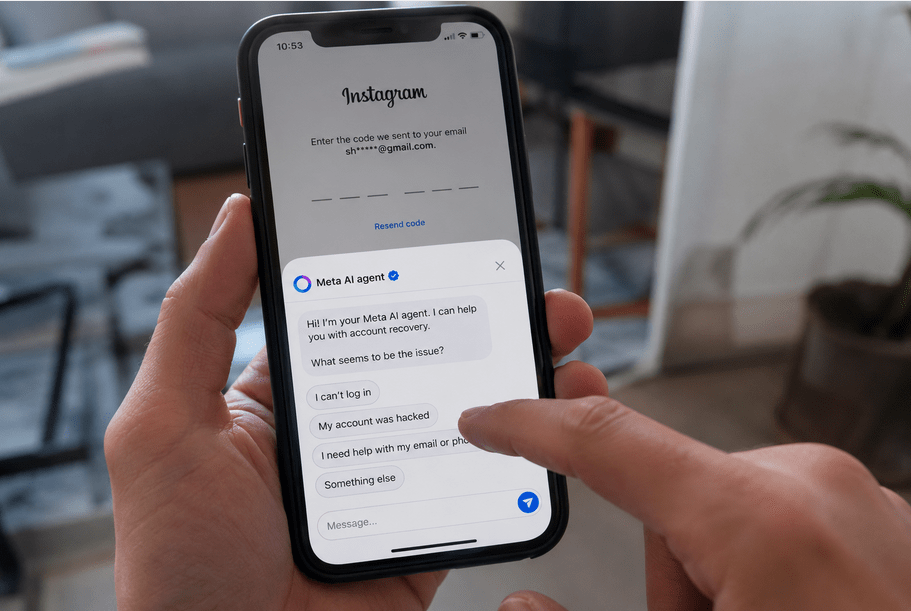
Hackers Didn’t Hack Instagram: They Convinced Meta’s AI to Hand Over More Than 20,000 Accounts
Meta’s disclosure that attackers abused an AI-assisted account recovery system to hijack more than 20,000 Instagram accounts is rapidly becoming one of the most consequential security incidents in the emergingRead More →