Canadian authorities have dismantled what appears to be one of the most technically sophisticated financially motivated telecom attacks publicly documented in North America after arresting three suspects accused of operating vehicle-mounted “SMS blaster” systems that impersonated legitimate cellular towers, induced nearby mobile devices into attaching to rogue infrastructure, delivered phishing messages to those devices—likely through direct rogue-network messaging rather than traditional carrier SMS infrastructure, according to available public details and technical analysis—and triggered roughly 13 million network disruptions across the Greater Toronto Area.
According to Toronto Police Service, the investigation—codenamed Project Lighthouse—began in November 2025 after law enforcement received intelligence from a cybersecurity partner regarding suspicious telecommunications activity occurring in downtown Toronto. Investigators ultimately determined that attackers were moving throughout Toronto in vehicles equipped with rogue wireless infrastructure capable of directly interacting with nearby mobile devices.
Police said the infrastructure connected with tens of thousands of devices, disrupted legitimate cellular connectivity, and may have temporarily interfered with emergency communications, including 911 access. Search warrants executed on March 31 in Markham and Hamilton led to the seizure of multiple SMS blaster systems and electronic equipment. Two suspects were arrested during the raids, while a third surrendered on April 21. Authorities declined to release photographs of the seized devices, describing them only as “uniquely built” due to public safety concerns.
That phrase is particularly notable because it strongly suggests investigators recovered custom-built rogue telecom infrastructure rather than conventional phishing hardware.
The Attack Bypassed Traditional Smishing Infrastructure Entirely
Traditional SMS phishing campaigns rely on:
- bulk messaging providers
- compromised SMS gateways
- SIM farms
- cloud communication APIs
- third-party telecommunications aggregators
Those operations leave artifacts across legitimate telecom infrastructure, where carriers can detect abnormal sender behavior, identify malicious links, and suspend abusive campaigns.
The Toronto operation appears to have bypassed that model entirely.
Instead of sending phishing messages through legitimate Short Message Service Centers (SMSCs), attackers allegedly operated rogue radio infrastructure capable of communicating directly with nearby phones over cellular frequencies.
In legitimate SMS routing:
Phone → Cell Tower → Carrier Core Network → SMSC → Recipient
In the Toronto operation:
Phone → Rogue Tower → Attacker-Controlled SMS Infrastructure → Victim Device
This bypassed carrier anti-spam filtering entirely because the carrier never handled the message. The attackers temporarily became the telecommunications provider.
Why Traditional Detection Mechanisms Failed
Carrier-side SMS filtering systems rely on several control points that were entirely circumvented:
SMSC-level filtering — Short Message Service Centers inspect message content, sender reputation, and delivery rate thresholds. Since messages originated from the rogue infrastructure rather than a carrier SMSC, no SMSC ever processed the traffic.
SS7 signaling monitoring — Carriers monitor Signaling System 7 (SS7) traffic for anomalous routing or location update storms. In a standalone rogue base station model, however, traditional SS7 monitoring may provide limited visibility because malicious activity occurs primarily at the radio access layer rather than the carrier core—though 2G and 3G architectures can still involve SS7/MAP signaling depending on how the rogue core is structured.
IMSI-based blacklisting — Carriers can block specific SIM identifiers from sending bulk messages. The rogue infrastructure never authenticated through the carrier’s Home Location Register (HLR) or Home Subscriber Server (HSS), rendering blacklisting irrelevant.
A2P (Application-to-Person) message rate limits — Carrier enforcement of per-sender message volume caps has no purchase against an out-of-band injection model.
GSMA SMS Firewall rules — Carriers deploy SMS firewalls at interconnect points to filter grey-route and spoofed traffic. No interconnect point was involved in this attack chain.
Software Defined Radio Hardware Likely Powered the Rogue Infrastructure
At the center of this type of operation is Software Defined Radio (SDR) hardware.
Traditional telecom towers rely on highly specialized ASIC-driven radio hardware designed for fixed functions. SDRs separate radio hardware from protocol logic by moving signal processing into software, allowing a single hardware platform to emulate virtually any radio protocol by replacing or modifying the software stack.
The physical hardware typically performs:
- RF transmission and reception
- Analog-to-digital and digital-to-analog conversion
- Frequency tuning and channel selection
- RF amplification and filtering
- Timing synchronization critical for cellular protocol compliance
Higher-layer telecom logic—including cellular protocol state machines, authentication procedures, and message routing—is handled by software running on attached computing systems.
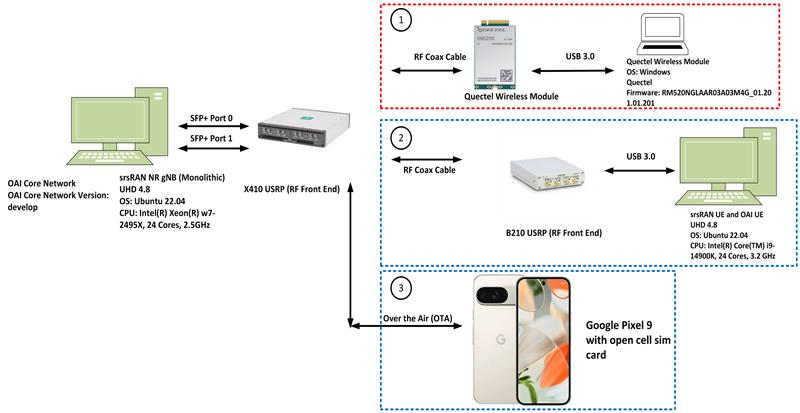
Ettus Research USRP Platforms
Ettus Research manufactures some of the most widely used SDR platforms for telecom experimentation.
USRP B210 remains one of the most common platforms for cellular experimentation because it supports:
- Full duplex communications over a single RF chain
- Simultaneous transmission and reception (critical for base station impersonation)
- 70 MHz–6 GHz frequency coverage encompassing all major cellular bands
- 2×2 MIMO antenna support
- LTE testing environments via srsRAN and OpenAirInterface
- FPGA-assisted signal processing via onboard Xilinx Spartan-6 FPGA
- USB 3.0 host interface with approximately 61.44 MHz instantaneous bandwidth
Full duplex capability is critical in rogue tower operations because the infrastructure must continuously broadcast tower beacon signals (System Information Blocks in LTE, BCCH/SCH in GSM) while simultaneously receiving and processing device attachment requests from victim phones.

USRP X310 provides significantly greater bandwidth and processing performance, making it better suited for:
- Multi-carrier deployments covering multiple bands simultaneously
- Higher-throughput data plane operations
- FPGA acceleration via onboard Kintex-7 FPGA
- Dual 10 GigE or PCIe host interfaces
Researchers have historically used USRP platforms for:
- Rogue eNodeB (LTE base station) research
- LTE protocol fuzzing and vulnerability discovery
- IMSI catcher construction and simulation
- Protocol security testing and standards auditing
- Lawful intercept system development
Nuand bladeRF
Nuand bladeRF platforms offer a lower-cost alternative while still supporting serious telecom experimentation.
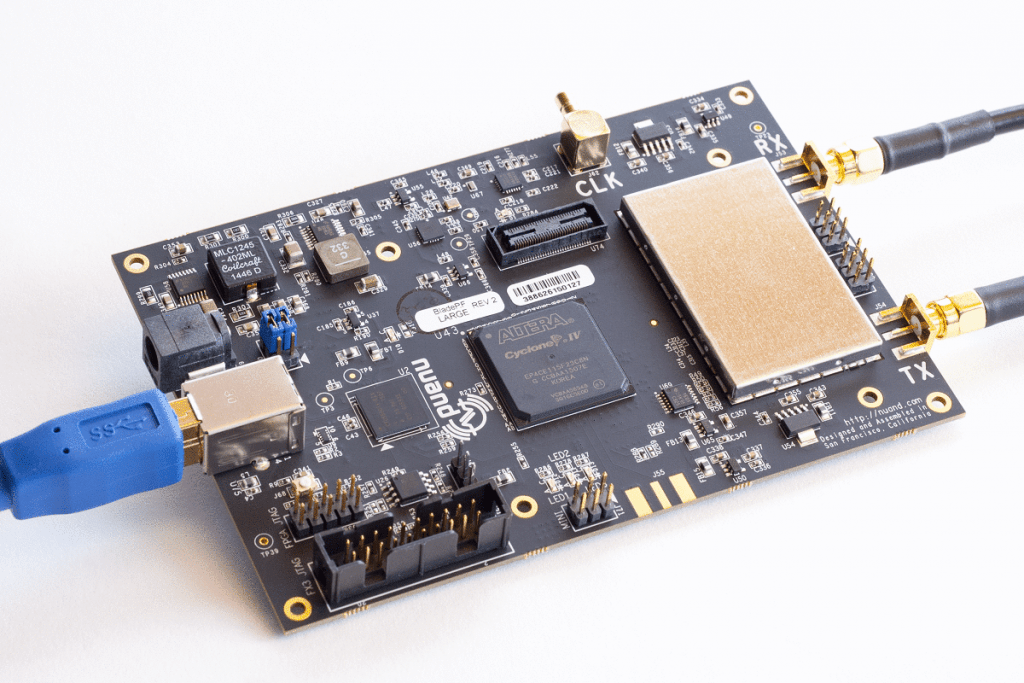
Capabilities include:
- Onboard FPGA acceleration (Cyclone IV or Cyclone V depending on model)
- Full transceiver functionality via Lime Microsystems LMS6002D or LMS7002M RF transceiver
- Broad cellular band support (300 MHz–3.8 GHz on bladeRF x40/x115; 47 MHz–6 GHz on bladeRF 2.0 micro)
- USB 3.0 interface with up to 40 MHz instantaneous bandwidth
- Compact deployment design favorable for vehicle-concealed operations
BladeRF systems are frequently used in rogue GSM and LTE experimentation due to their portability, affordability, and compatibility with open-source cellular stacks including OsmocomBB and srsRAN.
HackRF One
HackRF One, developed by Michael Ossmann, is one of the most widely known SDR devices.
It supports:
- 1 MHz–6 GHz frequency range
- Portability suitable for reconnaissance and signal mapping
- Spectrum monitoring across broad frequency ranges
Its primary technical limitation is that it operates in half-duplex mode only, meaning the RF chain cannot simultaneously transmit and receive. This is an architectural constraint of the MAX2837 and MAX5864 ICs used in the design.
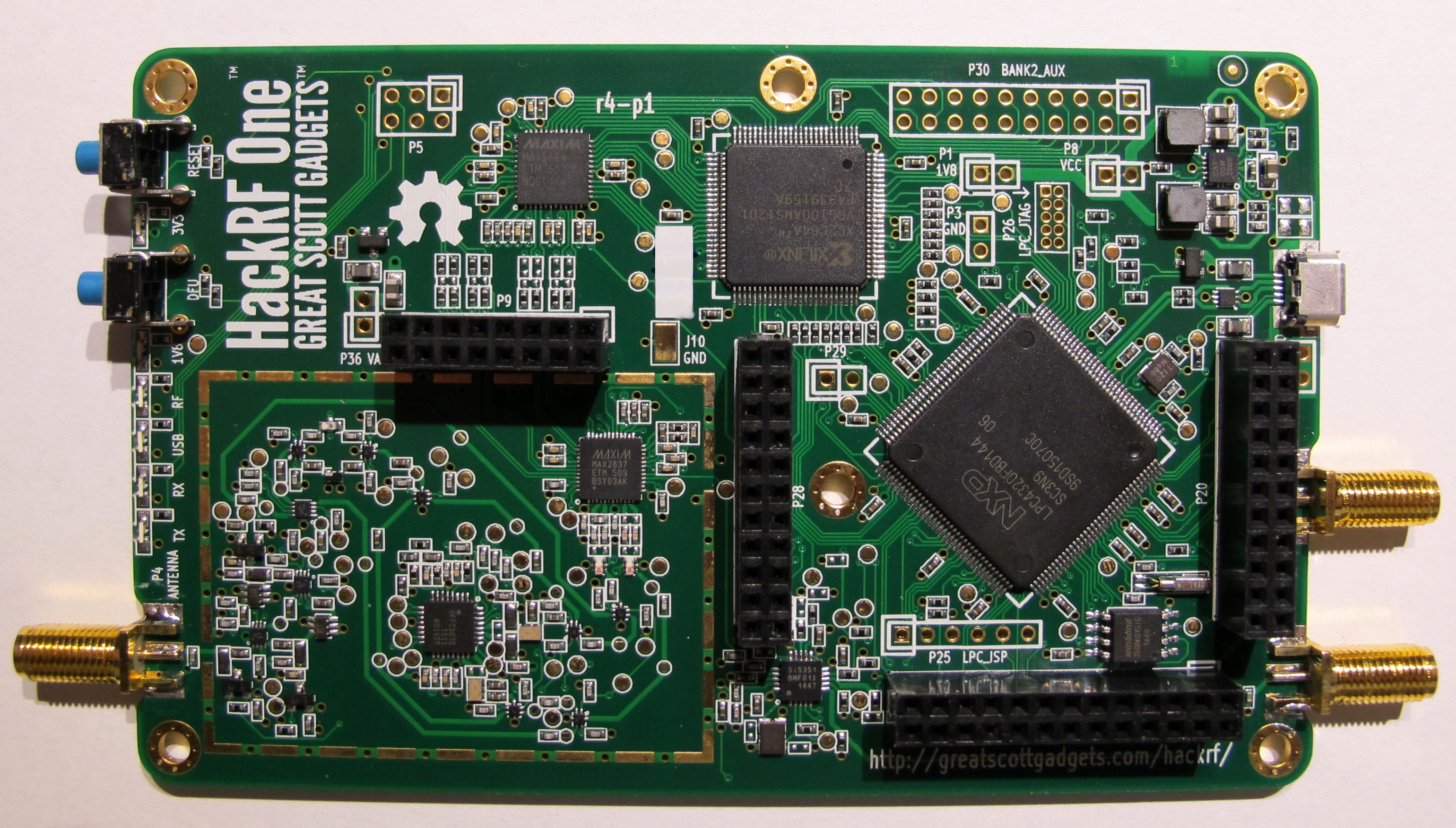
That limitation makes HackRF generally less practical for sustained rogue tower operations than full-duplex platforms, though researchers have used it in proof-of-concept wireless attacks. Sustained base station impersonation requires simultaneous:
- Broadcast synchronization signals (PSS/SSS in LTE)
- Transmit System Information Blocks (SIBs)
- Receive Random Access Channel (RACH) preambles from attaching devices
- Process uplink data channels
HackRF One is most useful in this threat context for:
- Target frequency discovery and carrier band mapping
- Signal strength surveying to identify optimal deployment positions
- Spectrum monitoring to identify competing towers and channel congestion
- Pre-attack reconnaissance to determine which protocol generation (2G/3G/4G) to emulate
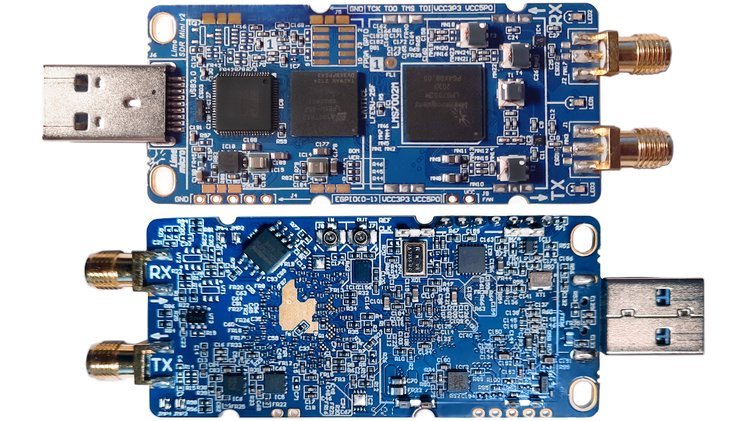
LimeSDR
LimeSDR platforms are frequently used in telecom labs because they support:
- Full duplex communication via the Lime Microsystems LMS7002M RF transceiver chip
- Frequency coverage from 100 kHz to 3.8 GHz
- 2×2 MIMO configuration with multiple antenna paths
- FPGA acceleration via onboard Intel Cyclone IV (LimeSDR-USB) or ECP5 (LimeSDR-Mini)
- USB 3.0 and PCIe host interfaces depending on model
The LMS7002M chip’s architecture is particularly notable because it integrates a fully programmable digital baseband, allowing more of the protocol stack to run closer to the hardware—reducing latency in time-critical cellular protocol operations such as RACH response timing.
Modified Telecom Boards
This category may be especially relevant given law enforcement’s description of “uniquely built” devices. Investigators did not disclose the hardware design, but that phrase may indicate customized RF assemblies or modified telecom-grade components rather than off-the-shelf SDR hardware.
Telecom-grade boards, if incorporated, would offer significant operational advantages over consumer SDR platforms:
- Higher RF output power — Commercial base station hardware is engineered for kilometer-scale cell coverage, whereas SDR platforms typically produce milliwatt-level outputs requiring external amplification
- Improved protocol compliance — Hardware designed and tested against 3GPP specifications tends to achieve higher compatibility with a broader range of device firmware implementations
- Larger geographic coverage radius — Even operated at reduced power, purpose-built radio hardware may reach hundreds of meters, versus tens of meters for low-power SDR platforms
- Improved thermal reliability — SDR platforms running intensive cellular workloads can overheat under sustained operation; purpose-built hardware is designed for continuous duty cycles
Regardless of the RF front end, operators in this class of deployment typically integrate supporting components such as:
- RF power amplifiers (e.g., Mini-Circuits ZHL series or cellular-band-specific PAs)
- Directional Yagi or panel antennas for focused coverage
- Omnidirectional antennas for broad area coverage
- GPS disciplined oscillators (GPSDO) for precise frequency and timing synchronization—critical for LTE timing advance calculations
- Power inverters converting vehicle 12V DC to AC for equipment powering
- Embedded Linux systems (Raspberry Pi, NVIDIA Jetson, or x86 mini-PCs) running the software stack
- Battery arrays enabling covert stationary deployment with engine off
This architecture enables continuous vehicle-based operations without requiring proximity to power infrastructure.
Rogue Base Station Software Enabled Network Impersonation
SDR hardware alone cannot impersonate a mobile provider. Attackers require software that emulates radio access network functions and, in more sophisticated deployments, carrier core infrastructure.
GSM Protocol Weakness: Unilateral Authentication
A fundamental design flaw in GSM (2G) makes it uniquely attractive for rogue tower attacks: the network authenticates the subscriber, but the subscriber does not authenticate the network.
In legitimate GSM authentication:
Network → Sends RAND (random challenge) → Phone
Phone → Computes SRES using Ki (SIM secret key) → Network
Network → Verifies SRES → Grants access
The phone has no mechanism to verify that the network it is attaching to is legitimate. Any base station broadcasting valid GSM signals with an appropriate Mobile Country Code (MCC) and Mobile Network Code (MNC) can attract device attachments.
LTE introduced Evolved Packet System Authentication and Key Agreement (EPS-AKA), which provides mutual authentication—but the downgrade attack described in the Phase 3 section circumvents this protection.
OpenBTS
OpenBTS was one of the earliest major projects demonstrating that GSM infrastructure could be virtualized using commodity SDR hardware, first publicly demonstrated circa 2008.
OpenBTS converts GSM radio communications into SIP (Session Initiation Protocol) traffic, allowing voice and SMS to be routed through VoIP infrastructure.

Architecture:
Phone → Fake GSM Tower (SDR) → OpenBTS → Asterisk PBX → SIP Backend
Key components:
- Transceiver layer — Handles physical-layer radio signal processing, including burst formatting, frequency correction, and timing alignment
- OpenBTS core — Implements Layer 2 (data link) and Layer 3 (network) GSM protocols
- Asterisk integration — Routes calls and SMS through the Asterisk PBX, enabling arbitrary message injection
Because GSM lacks mutual authentication, OpenBTS can attract device connections without possessing subscriber credentials. SMS messages can be injected directly to attached devices without any carrier involvement.
YateBTS
YateBTS provides a more integrated alternative to OpenBTS:
- GSM and GPRS emulation on a single platform
- Built-in SMS routing without requiring a separate PBX
- Voice routing via the YATE PBX engine
- Subscriber registration services via an embedded HLR
- Web-based management interface suitable for less technically sophisticated operators
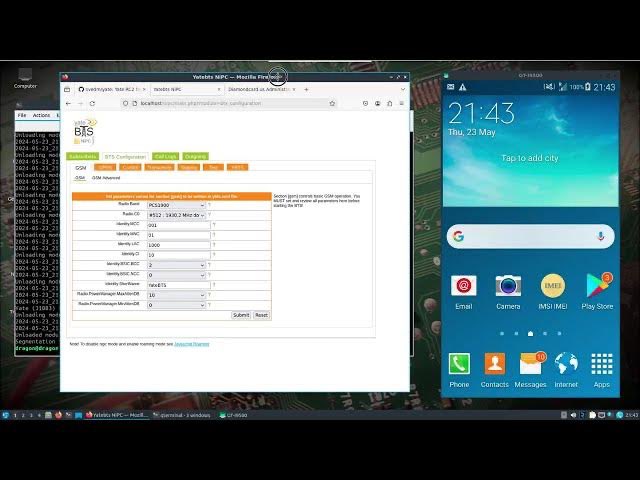
YateBTS’s lower deployment complexity makes it particularly attractive for criminal operators who lack deep telecom engineering backgrounds.
Osmocom
The Osmocom project provides a modular, production-grade open-source GSM stack that more completely emulates carrier infrastructure.
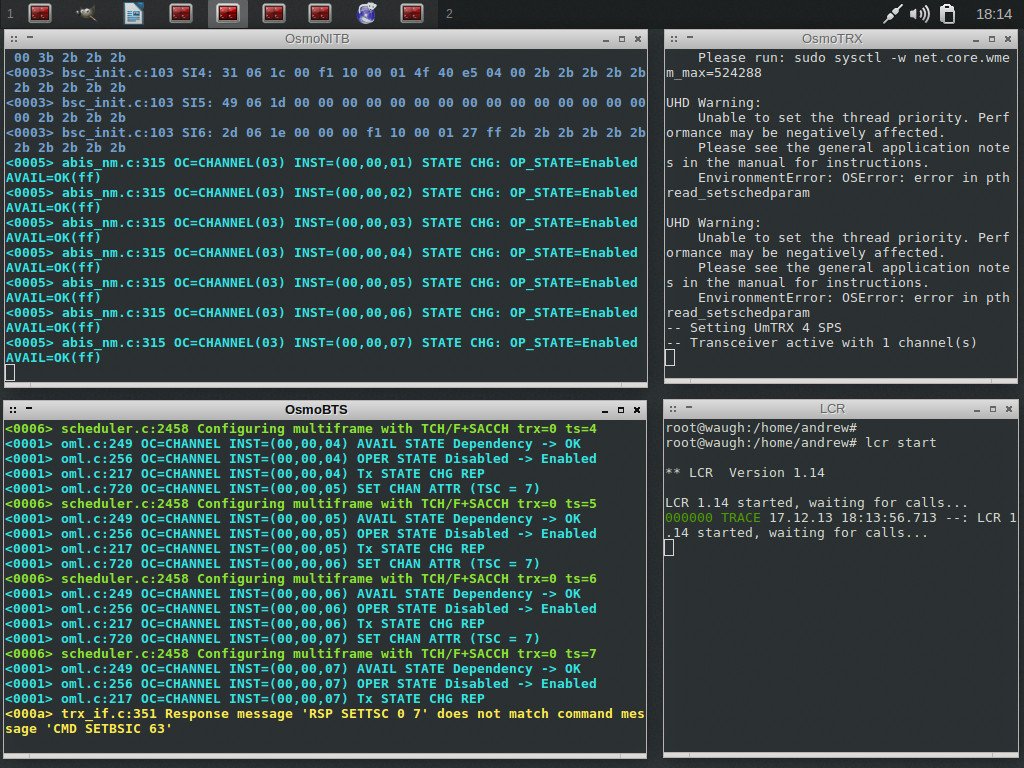
| Component | Function |
|---|---|
| OsmoBTS | Base Transceiver Station — handles radio protocol layers |
| OsmoBSC | Base Station Controller — manages multiple BTSs |
| OsmoMSC | Mobile Switching Center — handles voice call routing |
| OsmoHLR | Home Location Register — stores subscriber identities and authentication data |
| OsmoSGSN | Serving GPRS Support Node — manages packet data sessions |
| OsmoGGSN | Gateway GPRS Support Node — connects packet data to internet |
| OsmoSTP | Signaling Transfer Point — routes SS7 signaling |
Together, attackers can emulate large portions of real carrier infrastructure. The Osmocom stack is notable because it supports the Abis interface (between BTS and BSC) over IP, enabling geographically distributed deployments where radio hardware and core network processing run on separate systems.
srsRAN (formerly srsLTE)
srsRAN extends rogue base station capabilities into the LTE generation:
- Rogue LTE eNodeB (eNB) creation targeting modern 4G devices
- User Equipment (UE) emulation for protocol testing
- Complete LTE downlink and uplink implementation
- Partial 5G NR (New Radio) support in srsRAN 4G/Project branches
- Integration with GNU Radio for signal processing pipelines
LTE attacks are technically more difficult because LTE mandates EPS-AKA mutual authentication and uses stronger encryption (AES-based SNOW 3G and ZUC algorithms). However, several attack vectors remain viable:
- Null encryption attack — Some eNB implementations can negotiate no encryption if the UE accepts it; rogue eNBs can attempt to force null ciphering
- Attach rejection attacks — The rogue eNB issues an Attach Reject message with a cause code (e.g., cause #14 “EPS services not allowed”) that causes the device to detach and potentially fall back to 2G
- RRC (Radio Resource Control) message injection — Certain RRC messages do not require established security context and can be injected prior to authentication completion
- TAU (Tracking Area Update) storms — Repeated TAU requests can be exploited to track device locations and generate denial-of-service conditions against legitimate networks
Open5GS
Open5GS enables attackers to construct a complete fake mobile core network, supporting both 4G EPC (Evolved Packet Core) and 5G core architectures.
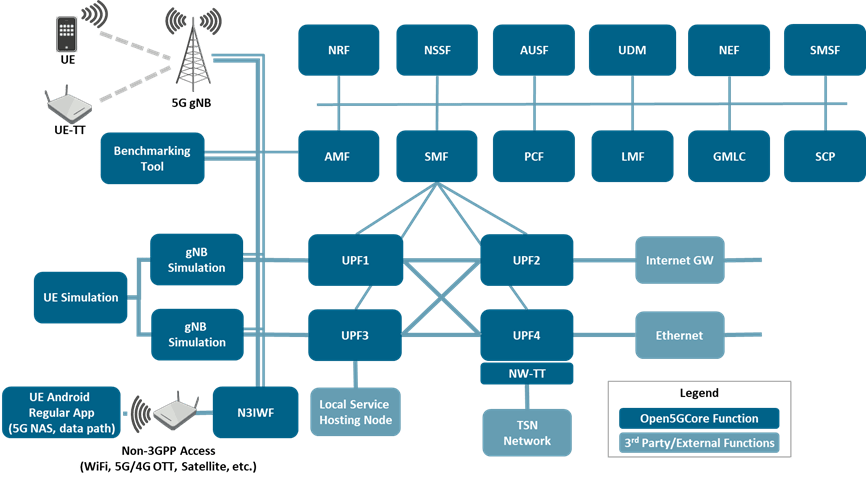
4G EPC components:
| Component | Function |
|---|---|
| MME | Mobility Management Entity — handles device registration, authentication coordination, and handover |
| HSS | Home Subscriber Server — stores authentication vectors and subscriber profiles |
| SGW | Serving Gateway — handles user-plane data routing |
| PGW | PDN Gateway — connects UE to external packet data networks |
| PCRF | Policy and Charging Rules Function — controls QoS policies |
5G Core components:
| Component | Function |
|---|---|
| AMF | Access and Mobility Management Function — handles registration and connection management |
| SMF | Session Management Function — manages PDU sessions |
| UPF | User Plane Function — routes user data traffic |
| AUSF | Authentication Server Function — manages 5G-AKA and EAP-AKA’ authentication |
| UDM | Unified Data Management — stores subscriber data |
With Open5GS, adversaries can build a complete fake backend mobile network that presents as a fully functional carrier infrastructure. This allows the rogue network to issue valid-appearing Temporary Mobile Subscriber Identity (TMSI) assignments, manage location area updates, and persist device connections beyond initial attachment—enabling sustained SMS injection sessions rather than single-message attacks.
End-to-End Attack Chain Reconstruction
Investigators have not released full forensic details, but the operational model can be reconstructed based on known rogue base station behavior, published academic research, and documented criminal deployments in other jurisdictions.
Phase 1: RF Reconnaissance
Attackers likely used SDR reconnaissance hardware to survey the target environment:
- Carrier frequency mapping — Identifying the specific ARFCN (Absolute Radio Frequency Channel Number) for GSM or EARFCN (E-UTRA Absolute Radio Frequency Channel Number) for LTE used by Bell, Rogers, and Telus in target areas
- Signal strength profiling — Mapping Received Signal Strength Indicator (RSSI) and Reference Signal Received Power (RSRP) across target zones to identify coverage gaps where rogue signals can dominate
- Cell ID inventory — Capturing CGI (Cell Global Identity) values broadcast in legitimate tower SIBs to allow accurate spoofing of carrier identity parameters
- Protocol generation mapping — Identifying which protocol layers (2G/3G/4G) are active in target zones and which devices are connecting on which generation
- Congestion analysis — Identifying peak traffic periods when legitimate tower load is highest, maximizing the proportion of devices that might prefer the rogue tower’s relatively unloaded signal
High-density target locations likely included downtown corridors, transit hubs, shopping districts, and major event venues.
Phase 2: Rogue Tower Deployment
Vehicle-mounted infrastructure broadcasts fake cellular beacon signals.
In LTE, the rogue eNodeB broadcasts:
- Physical Broadcast Channel (PBCH) — Contains the Master Information Block (MIB) with basic system parameters including downlink bandwidth and system frame number
- System Information Blocks (SIB1–SIB13) — Contain scheduling information, PLMN (Public Land Mobile Network) identities, tracking area codes, cell access restrictions, and neighbor cell lists
- Primary Synchronization Signal (PSS) and Secondary Synchronization Signal (SSS) — Enable devices to synchronize to the cell’s timing and identify the Physical Cell Identity (PCI)
The rogue tower advertises:
- Mobile Country Code (MCC) matching legitimate Canadian carriers (302 for Canada)
- Mobile Network Code (MNC) matching Bell (610), Rogers (720), or Telus (220)
- Tracking Area Code (TAC) — Can match or differ from legitimate towers; matching TACs reduce Tracking Area Update signaling that might expose the rogue tower’s presence
- Cell Identity — 28-bit identifier used in CGI construction; spoofing a legitimate Cell ID can suppress UE neighbor cell measurement reporting
Phase 3: Protocol Downgrade Attack
Modern devices prefer LTE (4G) and will attempt 5G NR where available. Attackers may force protocol downgrade through several mechanisms:
LTE barring: The rogue eNodeB broadcasts access class barring information in SIB2, causing devices to consider the LTE cell as barred for normal service. Devices then search for available 3G (UMTS/HSPA) or 2G (GSM/GPRS) cells.
Frequency jamming: Narrowband jamming on LTE frequencies used by legitimate towers forces devices to lose their legitimate LTE connection and search for alternative connectivity. Jamming hardware can be as simple as a signal generator tuned to the target frequency with sufficient output power.
RSRP manipulation: If the rogue tower transmits a stronger LTE signal than legitimate towers on the same frequency, devices may attach to the rogue tower directly—no jamming required—and can then be downgraded by the rogue eNodeB issuing an RRC Release with redirect to a 2G frequency.
Deliberate Reject with fallback instruction: The rogue LTE tower can issue an Attach Reject (EMM cause #14 or #15) containing a “Redirect to GERAN” or “Redirect to UTRAN” information element, explicitly instructing the device to move to 2G or 3G where authentication is weaker or absent.
This forces the protocol degradation sequence:
5G NR → LTE (4G) → UMTS/HSPA (3G) → GSM/GPRS (2G)
Older protocols are exploited because:
- GSM has no network-to-device authentication
- Legacy GSM networks rely on older encryption algorithms such as A5 variants for circuit-switched voice and data, while GPRS uses older GEA (GPRS Encryption Algorithm) variants that have historically faced security scrutiny—particularly GEA-1 and GEA-2, which researchers have demonstrated can be broken
- UMTS improved on GSM but remains vulnerable to certain bidding-down attacks
Phase 4: Device Attachment
Once operating on 2G, phones initiate Location Update or Attach procedures with the rogue network.
During GSM Location Update:
Phone → CHANNEL REQUEST → Rogue BTS
Rogue BTS → IMMEDIATE ASSIGNMENT → Phone
Phone → LOCATION UPDATING REQUEST (IMSI or TMSI) → Rogue BTS
Rogue BTS → AUTHENTICATION REQUEST (optional) → Phone
Phone → AUTHENTICATION RESPONSE → Rogue BTS
Rogue BTS → LOCATION UPDATING ACCEPT → Phone
During this process, victims may expose:
- IMSI (International Mobile Subscriber Identity) — Permanent 15-digit subscriber identifier tied to the SIM; exposed when the device has no TMSI or the rogue network requests it directly
- TMSI (Temporary Mobile Subscriber Identity) — Pseudonymous identifier issued by the network; still useful for tracking across sessions
- IMEI (International Mobile Equipment Identity) — Device hardware identifier; exposed via IDENTITY REQUEST messages
- Authentication response values — If the rogue network issues an authentication challenge, the device’s response can be captured for subsequent cryptanalysis
After successful attachment, the phone treats the rogue tower as its serving cell.
Phase 5: Network Entrapment
Phones may become trapped in repeated signaling loops due to:
- Authentication failures — Rogue network lacks subscriber authentication vectors from the real HLR; authentication challenges fail, causing retries
- T3210/T3230 timer expiry — Location Updating Request timeouts trigger re-attempts
- Repeated RACH storms — Devices continuously attempt random access on a channel that processes requests but never successfully establishes stable sessions
- Handoff failure loops — Devices attempt handoff to legitimate towers but are continuously attracted back to the stronger rogue signal
Each failed attachment attempt, timer expiry, and retry contributes to the reported 13 million network disruption events. A single device in an entrapment loop can generate hundreds of signaling events per hour, explaining how tens of thousands of affected devices could produce 13 million disruptions.
Emergency call impact: Because the phone believed it was registered to the rogue network, emergency call attempts (911) would route through the rogue infrastructure rather than legitimate carrier emergency call paths. Under 3GPP specifications, even unauthenticated devices can place emergency calls on legitimate networks—but if the device never reaches a legitimate network, this fallback fails.
Phase 6: Direct SMS Injection
Once devices are attached to the rogue GSM infrastructure, SMS delivery does not require carrier SMSC involvement.
In GSM, the Short Message Service is delivered over the signaling plane using the SMS-DELIVER message format carried in GSM Radio Resource (RR), Mobility Management (MM), and Connection Management (CM) layers.
The rogue MSC/SGSN simply delivers the message directly:
Rogue MSC → SMS-DELIVER → Rogue BTS → Um interface → Victim Phone
Key injection parameters attackers control:
- Originating Address (OA) — The apparent sender number or alphanumeric sender ID displayed to the victim; completely attacker-controlled and can impersonate any organization
- Message content — Arbitrary text including Unicode characters, URLs, and callback numbers
- Message Class — GSM supports Class 0 (flash/immediate display), Class 1 (ME storage), Class 2 (SIM storage), Class 3 (TE delivery); Class 0 messages force an immediate pop-up on the device screen without user interaction required for display
- Protocol Identifier (PID) — Can be set to indicate special handling, including replacement of previous messages or silent discard
- Data Coding Scheme (DCS) — Controls character encoding (GSM 7-bit, 8-bit, UCS-2) and message class
Class 0 (Flash SMS) abuse is particularly effective: the message is displayed immediately on the screen without being stored in the phone’s message inbox, reducing forensic evidence and increasing urgency perception in social engineering scenarios.
Messages may impersonate:
- Major Canadian financial institutions (RBC, TD, Scotiabank, BMO, CIBC)
- Telecommunications providers (Bell, Rogers, Telus)
- Canada Revenue Agency or Service Canada
- Package delivery services (Canada Post, UPS, FedEx, Purolator)
Victims receive trusted-looking messages because the apparent sender ID (e.g., “BMO-Alerts” or “Bell”) appears authentic and the message bypassed all carrier filtering systems that would normally strip spoofed alphanumeric sender IDs.
Phase 7: Credential Theft Infrastructure
Victims clicking embedded URLs are directed to attacker-controlled infrastructure.
The phishing backend typically includes:
- Credential harvesting pages — Pixel-perfect clones of bank or government login portals capturing usernames, passwords, and PINs
- Real-time MFA interception proxies — Reverse proxy tools (Evilginx2, Modlishka, Muraena) that relay credentials to the legitimate site in real time, capture session tokens, and defeat time-based OTP (TOTP) and SMS-OTP controls without the victim noticing
- Adversary-in-the-Middle (AiTM) infrastructure — Session token theft that bypasses MFA by capturing authenticated session cookies rather than just credentials
- Payment fraud portals — Fake pages capturing payment card numbers, CVVs, and billing addresses
- Malware delivery pages — Drive-by download pages or pages prompting malicious APK installation on Android devices
- Callback phishing — Pages displaying fake fraud alert phone numbers where live agents further social-engineer victims
The combination of direct SMS injection (bypassing carrier spam filters) with real-time AiTM infrastructure represents a significant capability upgrade over conventional smishing, as MFA controls that would stop credential-only attacks are ineffective against session token theft.
Phase 8: Mobility and Evasion
Vehicle-based deployment provided significant operational security advantages:
- RF triangulation evasion — Law enforcement and carrier security teams use Time Difference of Arrival (TDOA) or Angle of Arrival (AoA) techniques to locate rogue transmitters. Constant movement degrades triangulation accuracy and increases location uncertainty from tens of meters to potentially kilometers
- Pattern-of-life disruption — Varying routes, timing, and target neighborhoods prevents analysts from developing predictive models of attacker movement
- Victim density optimization — Operators could identify and target high-density zones during peak hours, maximizing devices reached per operational hour
- Rapid extraction — If carrier security or law enforcement began triangulating the signal, the vehicle could relocate within minutes—far faster than the response time required to deploy RF triangulation assets
The vehicle likely used cellular signal surveys (via SDR scanning or commercial tools like TEMS or NEMO Handy) to pre-plan optimal routes through high-density corridors.
Defensive Countermeasures and Detection
Carrier-Level Detection Mechanisms
Despite the attack’s sophistication, several detection opportunities exist at the carrier level:
Sudden Location Area Update storms: When a rogue tower attracts devices, the carrier’s legitimate infrastructure observes a surge in devices simultaneously deregistering from their last known cell. Anomaly detection on Location Cancellation requests at the HLR/HSS can flag this pattern.
IMSI catcher detection via inconsistent timing: Legitimate towers maintain precise timing synchronization via GPS. Rogue towers using consumer GPS modules or software-based synchronization may exhibit slight timing drift that carrier measurement systems can detect as anomalous.
Network-side measurement correlation: LTE devices report neighbor cell measurements (signal strength of adjacent towers) back to their serving cell. A device that suddenly stops reporting measurements from previously visible neighbors may have attached to a rogue tower.
Subscriber complaint pattern analysis: Unusual clusters of subscriber complaints about dropped calls, failed 911 connections, or unexpected SMS messages in a specific geographic area can trigger carrier investigations.
Device-Level Protection Mechanisms
LTE/5G-only mode: Forcing devices to operate on LTE or 5G only prevents GSM downgrade attacks. Both iOS and Android support LTE-only (4G) network mode settings that disable 2G/3G fallback. Some devices and carriers expose 5G-only modes. This is the single most effective user-configurable protection.
SIM-based fraud detection: GSMA’s SIM Application Toolkit (SAT) allows carriers to push monitoring applications onto SIM cards that can detect anomalous network parameters and alert subscribers or report to the carrier.
SUPI concealment in 5G: 5G introduces SUPI (Subscription Permanent Identifier) concealment using a public key encryption scheme (SUCI – Subscription Concealed Identifier), preventing IMSI harvesting at the radio interface. This protection is absent in 2G and 3G and only partially implemented in LTE.
Law Enforcement Detection
Project Lighthouse’s success appears to have relied on:
- Intelligence from a cybersecurity partner — Likely a carrier security team or a commercial telecom security vendor using network-side anomaly detection
- Subscriber complaint correlation — Mapping reported SMS phishing messages to geographic areas and timeframes
- RF direction finding — Once approximate area was known, mobile direction-finding equipment could narrow the rogue transmitter’s location to a specific vehicle or address
- Subscriber metadata analysis — Identifying clusters of devices that experienced simultaneous connectivity disruption, attachment failures, or unexpected operator changes
Why This Operation Represents a Major Shift
Rogue cellular infrastructure has historically been associated with:
- Intelligence agencies using IMSI catchers (Stingray/Hailstorm) for surveillance
- Academic security researchers demonstrating protocol vulnerabilities
- Lawful intercept vendors developing commercial interception products
The Toronto operation demonstrates criminal actors operationalizing telecom-layer attacks for large-scale financial fraud at industrial scale.
Several factors make this particularly significant:
Technical barrier erosion: SDR hardware costs have dropped from tens of thousands of dollars to hundreds of dollars over the past decade. Open-source cellular stacks are freely available, documented, and maintained. The knowledge required to build a functional rogue base station has moved from specialized telecommunications engineering expertise to skills accessible to technically competent criminal operators.
Fraud yield optimization: By controlling the delivery channel entirely, operators eliminate the per-message cost and carrier detection risk associated with conventional smishing. A vehicle covering a dense urban corridor can reach tens of thousands of devices in hours, with zero marginal cost per SMS injected.
MFA bypass potential: Combined with AiTM phishing infrastructure, rogue-tower-delivered phishing can defeat SMS-OTP MFA by controlling both the SMS delivery channel and the phishing proxy.
Jurisdictional complexity: Vehicle-based mobile operations cross multiple municipal and provincial jurisdictions in a single operation, complicating law enforcement coordination and RF triangulation logistics.
Precedent for escalation: Criminal adoption of IMSI catcher-class hardware for fraud—rather than surveillance—represents a doctrinal shift in how telecom-layer capabilities are exploited. Successful operations like the Toronto deployment create templates that other criminal organizations can adopt and refine.
Rather than simply abusing communication platforms, the attackers temporarily became the communications infrastructure itself—combining RF engineering, telecom protocol exploitation, phishing operations, and mobility-based evasion into a highly scalable, detection-resistant criminal model that will likely inspire imitation.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
