How Criminals Created SMS Blasters to Fake Cellphone Towers and Hack Thousands of Phones in Canada
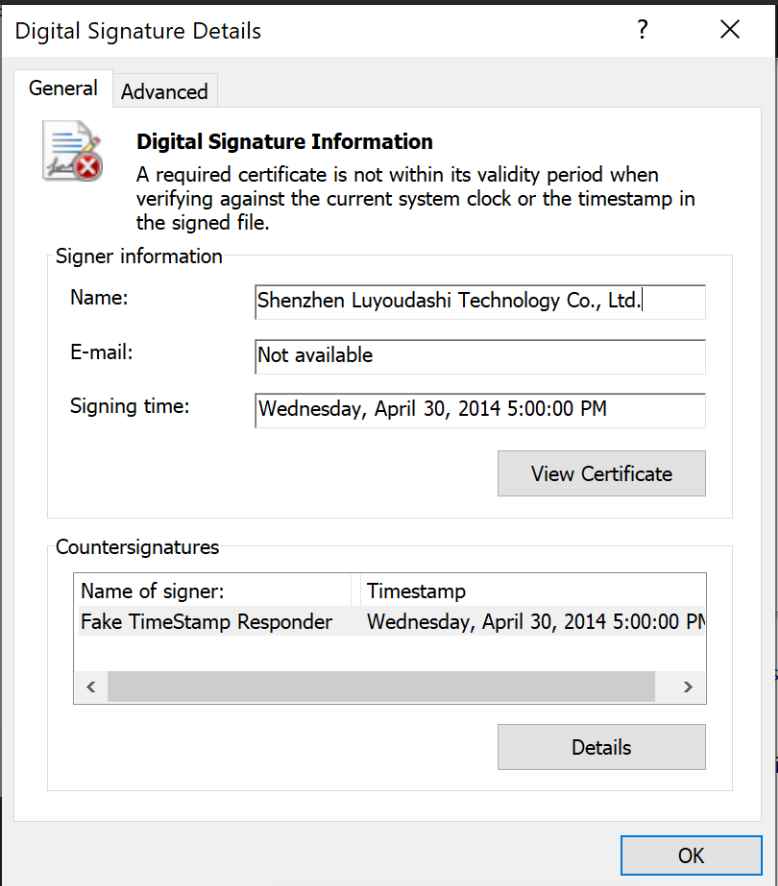
Canadian authorities have dismantled what appears to be one of the most technically sophisticated financially motivated telecom attacks publicly documented in North America after arresting three suspects accused of operatingRead More →