According to cybersecurity specialists, a hacker group has created a fake icon website with the goal of hiding malicious code and stealing payment card data on compromised websites, in what experts consider one of the most sophisticated hacking campaigns.
The cybersecurity community knows this attack variant as a skimming campaign or Magecart attack. Hackers compromise websites and then hide the malicious code on their pages, code that records and steals payment card details as they are entered into the payment forms.
The popularity of skimming attacks has increased considerably over the past four years, and as security companies improve their methods of anticipating hackers to detect them, they are also becoming more skilful and sophisticated.
In a recently released report, cybersecurity firm Malwarebytes mentions that a group of threat actors was detected taking their operations to a whole new level of sophistication. Researchers from the security company say that this hacking group was detected during an analysis of recent attacks related to favicon, the logo image displayed by tabs in a web browser.
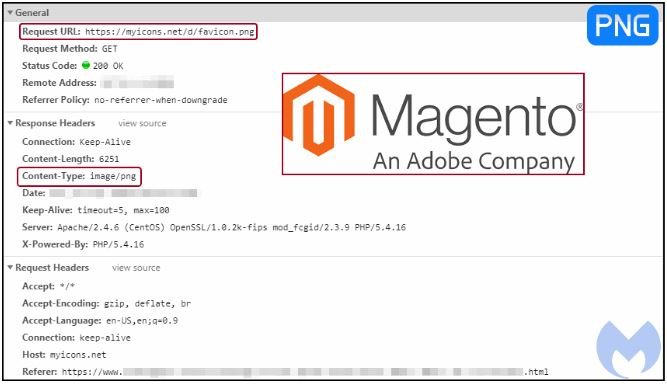
The new favicon was a legitimate image file hosted on MyIcons.net, with no hidden malicious code inside. However, although the change seemed innocent, Malwarebytes said that the web browsing code was still loaded on some compromised sites, so it became obvious that something was wrong.
According to Malwarebytes’ report, Mylcons.net (a compromised website) served a legitimate favicon file for all pages of a website, except pages containing payment forms. On these pages, the website loaded the favicon with a malicious JavaScript file, generating a fake payment form to extract the data from the victims’ cards.
As per Malwarebytes, site owners have already been notified and asked to investigate the incident and access the website MyIcons.net to check for this malicious JavaScript. However, soon after Malwarebytes discovered that this site was a clone of a legitimate portal (IconArchive.com). The site was also hosted on servers used by hackers in other skimming operations.
The hackers behind this operation made great efforts to hide their malicious code; however, such an aggressive skimming campaign is unlikely to go unnoticed, cybersecurity experts mention. However, researchers fear that other similar malicious campaigns will be detected in the future.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
