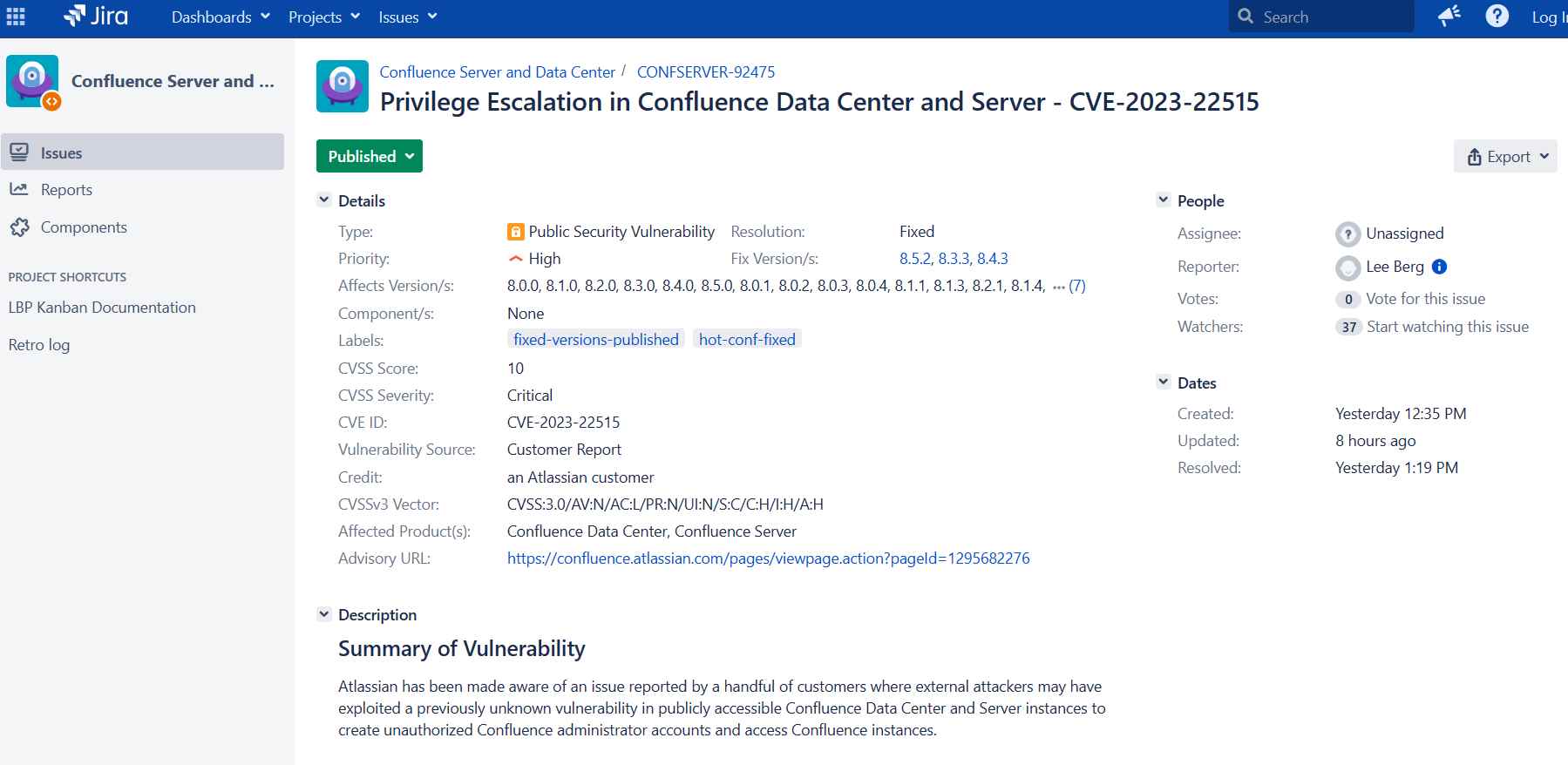
Hacking into an enterprise Atlassian Confluence and creating a permanent admin account
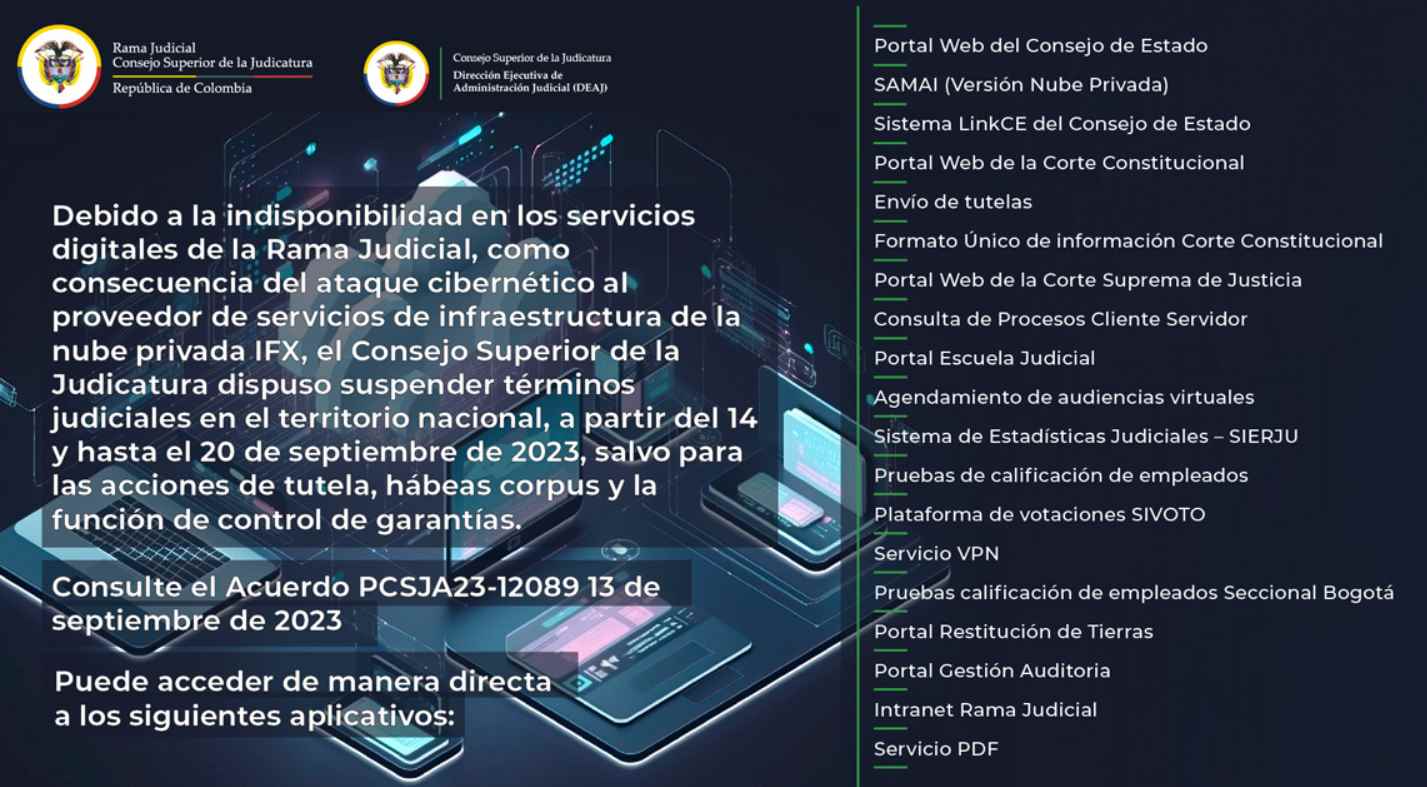
In the tech realm, the unsettling words ‘zero-day vulnerability’ can send shivers down the spine of even the most hardened IT veterans. The recent discovery and the swift action againstRead More →