Since Drupal 8’s first release in November 2015, the PHP-based open source online content management system has used Twig as its default template engine.
Drupal employs the third-party Twig library for sanitizing and templating content. A security patch for Twig has been made available; it impacts Drupal. The bug CVE IDs CVE-2022-39261 has a high severity according to Twig.
The code implementing Twig in Drupal core has also been changed to address a similar issue.
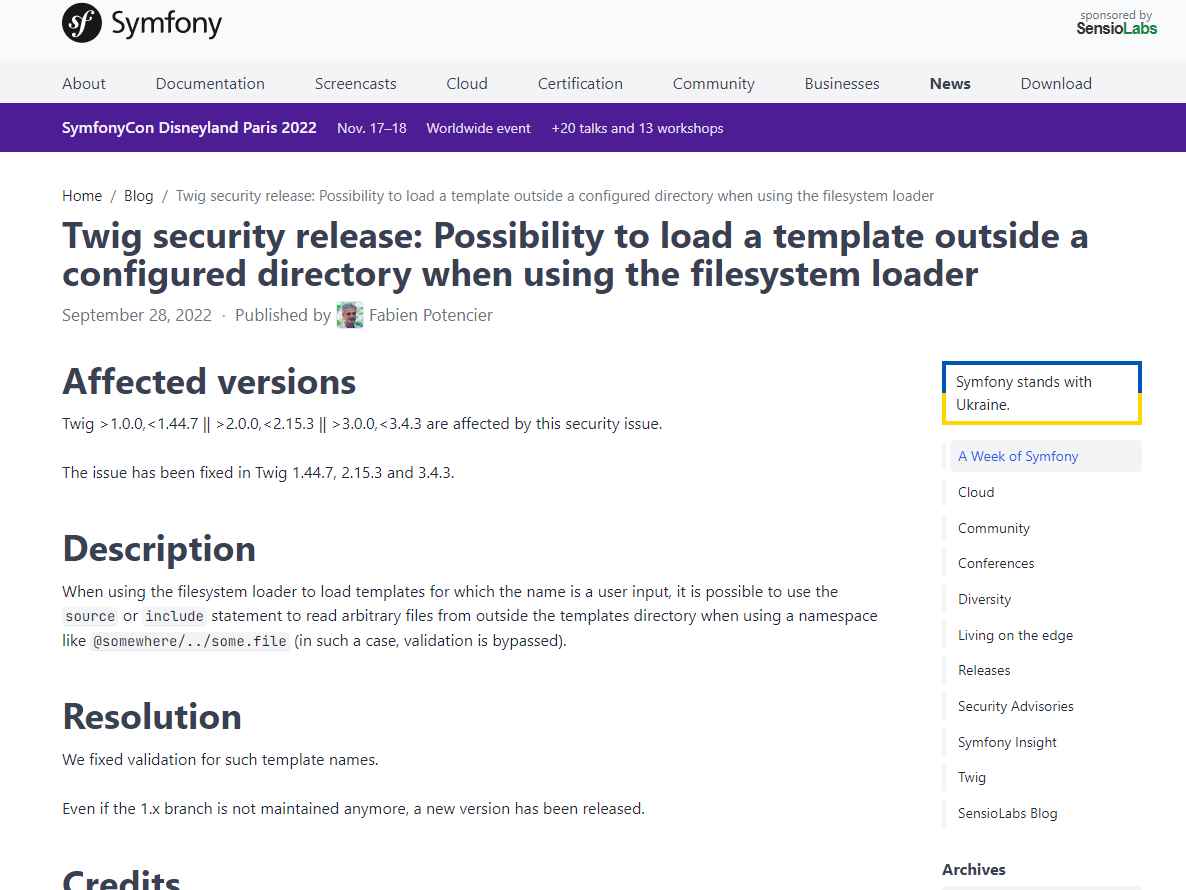
If an unauthorized user has access to write Twig code, a number of vulnerabilities are possible, including the potential for unauthorized read access to private files, the data of other files on the server, or database passwords.
Because an attack may only be performed on Drupal core with a restricted access administrative authority, the risk is reduced. It’s possible that donated or customized code that enables users to create Twig templates can lead to other exploit routes for the same vulnerability.
Mitigation
Upgrade to the most recent version:
Update to Drupal 9.4.7 if you are currently running Drupal 9.4.
Update to Drupal 9.3.22 if you are currently running Drupal 9.3.
Prior to 9.3.x, all Drupal 9 versions are considered to be “end-of-life” and are not supported in terms of security. Keep in mind that Drupal 8 is no longer supported.
Twig is not a part of Drupal 7’s core, hence it is unaffected.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
