Recently a critical flaw was revealed on the PowerEdge server that, if exploited, would allow threat actors to take full control of the operations of the affected server. The vulnerability was detected in the Dell EMC iDRAC remote access controller, the technology built into the latest versions of this product. Although the flaw was fixed e early this month, a team of researchers has just released a detailed analysis of this vulnerability.
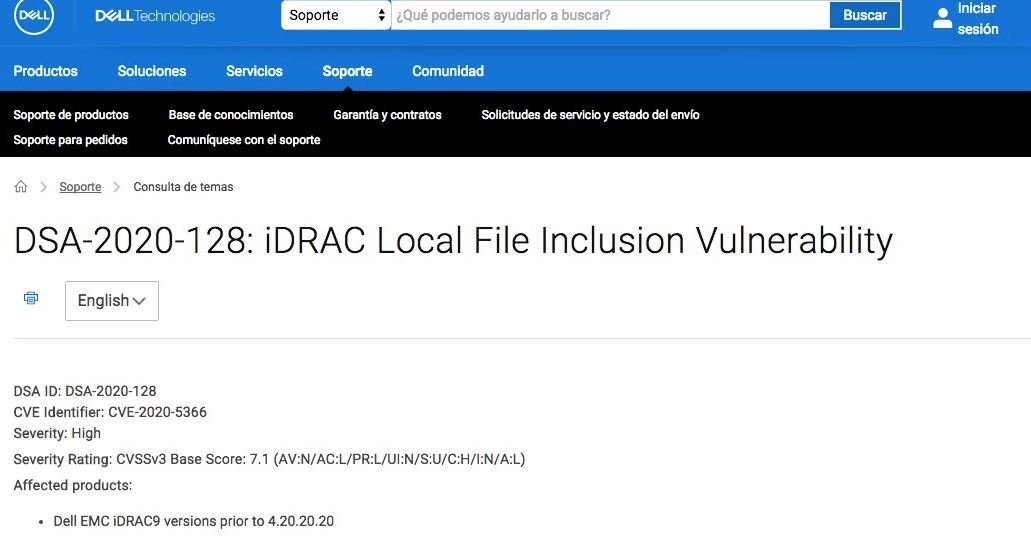
Tracked as CVE-2020-2366, this is a cross-path flaw present in all EMC iDRAC9 releases prior to 4.20.20.20 that received a score of 7.1/10 on the CVSS scale.
According to the report, this is one of the three most common vulnerabilities detected by security researchers. If exploited, this flaw would allow hackers to access the contents of the server folders, information that should not be accessible to users who are logged in as normal. Regarding the vulnerable product, threat actors might try to access the /etc/passwd file, which stores Linux user information.
According to the report, hackers can use this attack by exploiting two vulnerabilities in Zoom that could allow any participant’s system to be compromised in a video conferencing session. Moreover, if a threat actor exploits the flaw, it would gain unrestricted access to arbitrary files on the system.
Dell released an iDRAC firmware update that fixes the bug, so users are encouraged to upgrade as soon as possible. In the report, the researchers mention that the vulnerability could only be exploited in case iDRAC is connected to the Internet, setting little recommended. In addition, this is a relatively new technology on Dell EMC servers, so an attack would not be large. However, experts mention that it is possible to detect some affected implementations using conventional search engines.
For complete Dell server protection with iDRAC, experts recommend that customers place iDRAC on an isolated management network and refrain from connecting the controller to the Internet. Enterprise clients must also isolate the management network and restrict access to VLAN subnets only for authorized users.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
