Cybersecurity specialists reported the detection of multiple vulnerabilities in routers produced by tech firm Aruba Networks, whose exploitation would allow threat actors to deploy various malicious tasks, including remote code execution (RCE).
The flaws were reported by researchers at Aleph Security, who reported 8 vulnerabilities in Aruba Instant, the software that allows users to make adjustments to the configuration of Aruba routers.
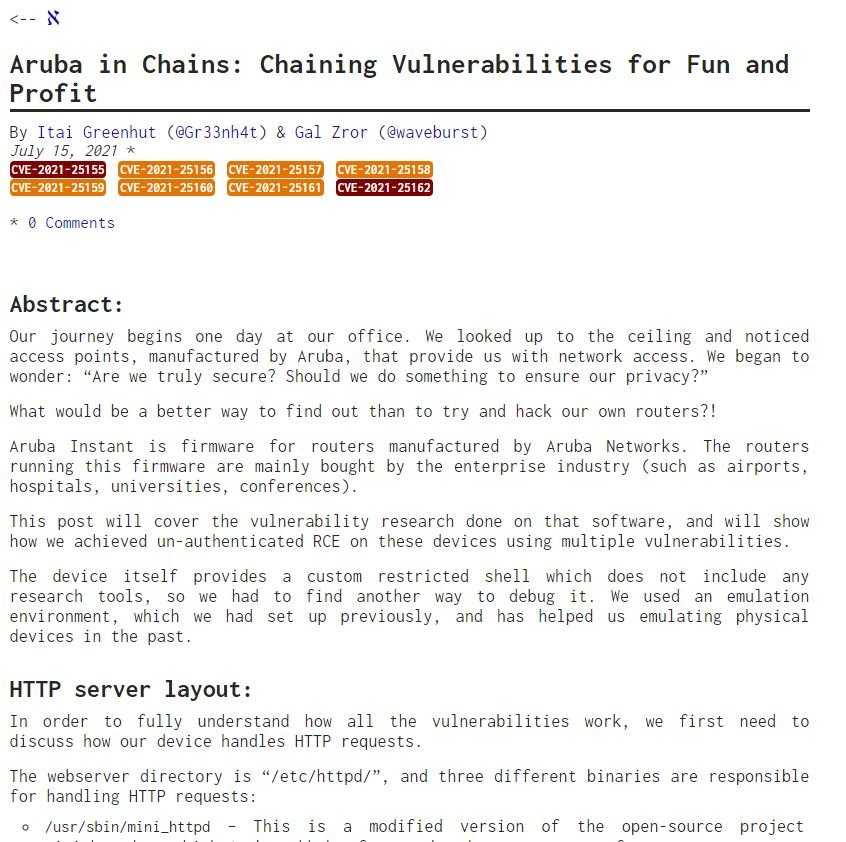
Itai Greenhut, the researcher in charge of the report, says: “Our research started because we were working from home and wanted to investigate our own WiFi equipment to test their security mechanisms.”
These devices are configured through a restricted command-line interface, plus they have a CGI portal that allows administrators to send commands to the CLI through a web interface. The vulnerability detected by the experts allows you to create directories and download files from the server, in addition to taking advantage of the same flaw through the query string of the web interface that communicates with the CLI module.
The experts later discovered a way to upload an arbitrary file to the directory where CGI is hosted, employing the server’s logging mechanism for the creation of a malicious file in the root directory of the web server. Finally, the experts used a flaw in the server’s PAPI interface to force exposure of router content; in some earlier versions of the firmware, the configuration file contains the password in plain text.
By abusing this information, threat actors could chain vulnerabilities together to gain root shell access to the affected routers. In their research, the experts found other vulnerabilities, including an argument injection flaw in the CLI library and a cross-site scripting (XSS) bug.
Aruba is a major supplier of equipment to enterprise customers, such as airports, hospitals, and universities, so the implications of having vulnerable routers in public locations and accessible over the Internet can be critical. Aruba prompts users to deploy the appropriate updates as soon as possible.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
