Through a Telegram channel, a group of hacktivism claims to have infected the private network of the Belarusian railway with a powerful ransomware variant, in an attempt to stop the export of military personnel and equipment from Russia to Ukraine. This seems to be a very rare attack in such a conflict, which would have already caused the fall of multiple critical services.
This group, identified as ‘Cyber Partisans’, claims that servers, databases and workstations on the affected network have been blocked, trying to slow down and even interrupt the circulation of the railway system in Belarus.
Cyber Partisans says they will only allow the restoration of services if the Belarusian government meets some conditions, including the release of 50 political prisoners who require medical attention, in addition to the expulsion of Russian troops from their territory: “The government continues to repress the free will of Belarusians, imprisoning innocent people and illegally holding thousands of political prisoners.”
Specialists mention that Belarus is a key country in this international conflict, since it is one of Russia’s main allies, with whom it shares a border in addition to Ukraine. Thanks to this, the Russian government has accelerated the mobilization of its troops to Ukrainian territory through the Belarusian railway system.
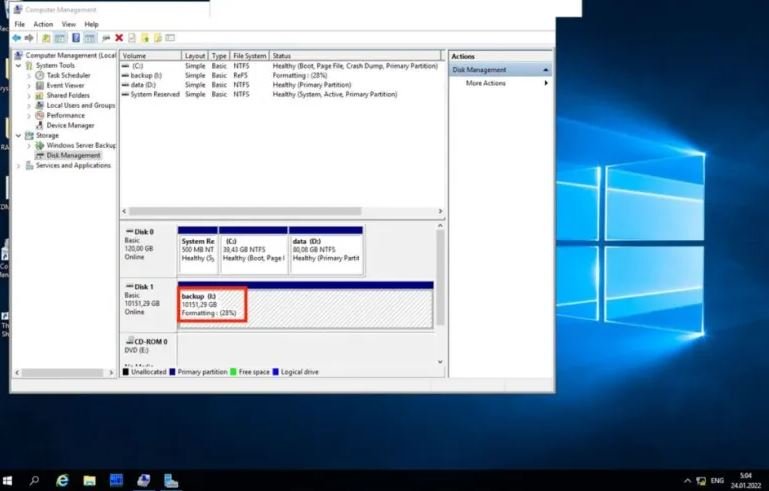
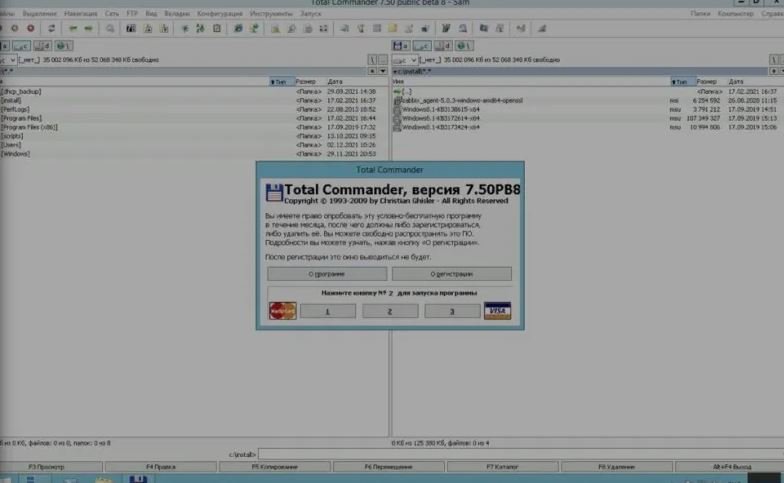
The cyberattack appears to have severely affected the rail system, impeding the full functioning of ticketing systems and blocking access to multiple services. The hacktivists shared some screenshots showing that they managed to take control of some services.
The use of a ransomware attack in an international conflict of this magnitude is something that, until now, we have never seen even though the multiple cyberwarfare examples seen nowadays. This type of attack, in fact, is usually common in companies or companies, and extortion method is used to demand payment in exchange for returning all services to normal.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
