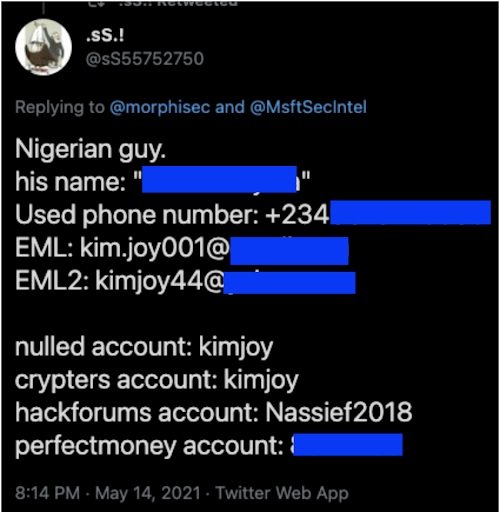
Cisco Talos cybersecurity researchers report the detection of an espionage campaign against the airline industry, using hacking tools such as AsyncRAT and other remote access Trojans (RATs). This campaign, identified as Operation Layover, has been attributed to a Nigeria-based threat actor, active in the cybercriminal community since 2015 and characterized by unsophisticated attacks.
Apparently, the campaign aims to deploy attacks of data theft, electronic fraud and financial fraud, among other variants of attack. According to the report, the operator of the attack uses conventional malware available on the dark web, so no new malware variants are actually being used. The attacker also involves the use of “crypters”, supplementary tools that allow RATs to be used to evade detection.
The attacker’s primary goal is the theft of cookies and login credentials, which can be sold to other hacking groups for the deployment of subsequent attacks, including credential stuffing, enterprise email compromise (BEC) and ransomware infections.

This campaign takes place in a context in which this variant of fraud and its operators, known as initial access brokers (IAB), are growing excessively. Throughout the dark web, platforms have appeared to sell this information to hacking groups around the world.
About this attack, experts mention that it begins with a phishing and spam campaign, with the hacker posing as a representative of aerospace companies to send dozens of emails to various targets. The message refers to topics related to air travel and includes a link to a supposed PDF file; if the target user clicks, they will be redirected to a script. VBS hosted on Google Drive, where the RAT payload is encrypted and delivered to the victim’s system, which will trigger the final attack.
The Cisco Talos report also points to the detection of some domains used as C&C, such as akconsult.linkpc.net, used to host the AsyncRAT payload. This server used TLS for the encryption of its communications, which allowed performing a search with this same digital record and detect eight other domains linked to this campaign.
The researchers point out that these domains were identified between last May and June, in addition to the therefore that at the time of their detection some of these domains had only a couple of days of registration. The report also notes the detection of 14 malicious .VBS files.
A few months ago Microsoft also published a report in reference to this campaign, noting that threat actors used other tools such as Agent Tesla for the exfiltration of confidential data, in addition to being able to take screenshots of the affected systems and perform network mappings.
Although the little sophistication of the attacker has made it possible to detect this campaign, Cisco Talos researchers believe that the risk should not be underestimated: “Many threat actors can act impulsively and continue to pose a severe risk; while this is a simple attack, operators have been able to continue the active campaign for at least three years, so a way must be found to contain the threat,” the report concludes.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
