To encourage manufacturers to provide better security upgrades, the Zero Day Initiative (ZDI), a vulnerability reseller, has shortened its disclosure deadlines for incomplete fixes.
Security company Trend Micro’s ZDI is moving as a result of what it calls a “disturbing” decline in patch quality and an increase in ambiguous messaging regarding fixes.
The effect on businesses is that they are unable to assess the danger to their systems and waste money deploying partial fixes that are later published and require reapplication.
Software suppliers have 120 days under ZDI’s regular disclosure timeframe to deploy a fix, but it is also establishing shorter deadlines for “failed patches” that it will be tracking.

If a patch fails and the defect is severe, it will allow suppliers 30 days to fix it if exploitation is anticipated and the patch is simple to get around. If the patch offers some defense and exploitation is conceivable, vendors will have 60 days to remedy critical and high severity problems. For any other vulnerabilities with a severity level below these and no immediate threat of exploitation, they will be given 90 days.
Software manufacturers have also come under fire from Google Project Zero researcher Maddie Stone for issuing unfinished updates. She calculated that more thorough patching and regression tests might have prevented half of the 18 zero-day or previously unreported problems in the first half of 2022. Some of the flaws are initially addressed, but they eventually return.
Attackers were able to return and re-expose the initial vulnerability through a new route since the root cause problem was not fixed, she said.
Not simply patch quality is a problem; companies also fail to disclose vulnerabilities. Dustin Childs of ZDI criticizes Microsoft’s intention to stop including executive summaries in its Security Update Guide (SUG) on each Patch Tuesday starting in 2020.
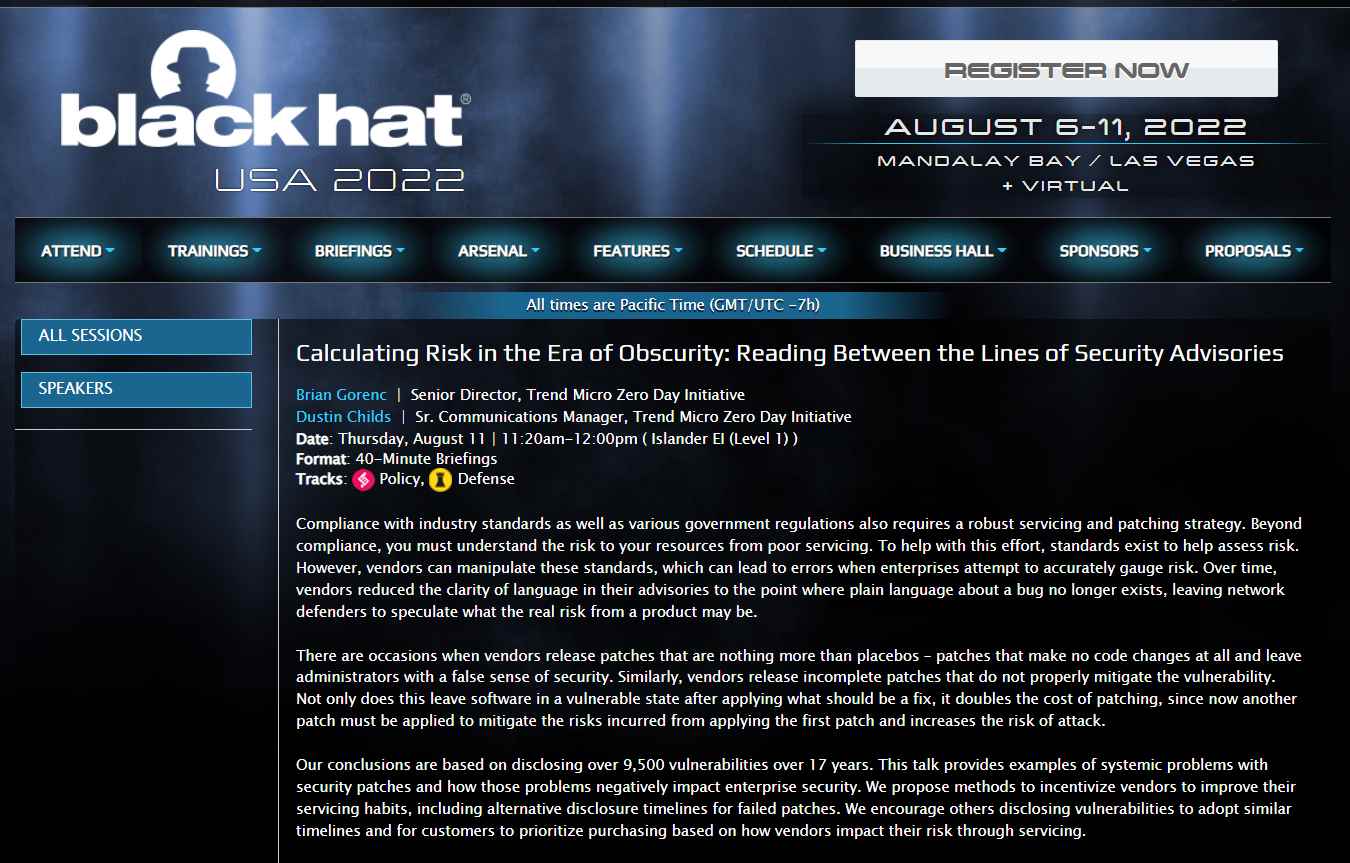
According to Childs, who spoke at Black Hat 2022, defenders no longer get the context they formerly did, along with information about, for instance, what security feature was evaded.
He also calculated that 10% to 20% of the flaws researchers analyze in ZDI’s tool, which has revealed 10,000 bugs since 2005, are the result of a flawed or insufficient repair.
Cyber Security Researcher. Information security specialist, currently working as risk infrastructure specialist & investigator.
He is a cyber-security researcher with over 18 years of experience. He has served with the Intelligence Agency as a Senior Intelligence Officer. He has also worked on the projects of Citrix and Google in deploying cyber security solutions. He has aided the government and many federal agencies in thwarting many cyber crimes. He has been writing for us in his free time since last 5 years.
