Adobe developers announced the open source release of One-Stop Anomaly Shop (OSAS), a tool designed for analysis and detection of anomalies in large data sets that can be quite useful for any security team.
OSAS relies on the collection of information on research, technical reports and projects previously carried out to enable researchers to experiment with all kinds of datasets, controlling the processing and combination of functions to finally identify a solution to potential threats detected in the process.
Developers expect this project to address the problem of data scarcity, which occurs when using algorithms and machine learning models with security logs that have a large feature space, which could sometimes lead to misconceptions of unreleased situations.
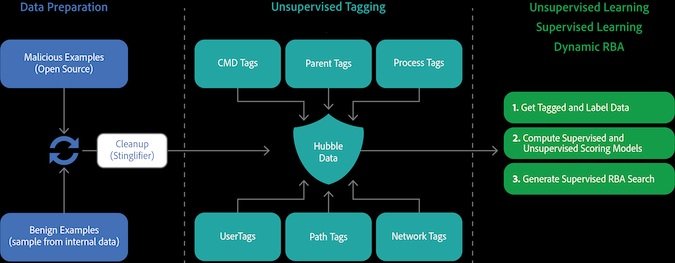
To lessen this effect, this project will implement a completely new approach to data processing, which involves consuming and tagging raw data based on standard recipes, and then using those tags as input features for monitored and unsupervised machine learning algorithms.
OSAS can also be used to generate a custom pipeline configuration file, creating a pre-trained model for the custom pipeline and applying the model created on unprocessed data.
This advanced machine learning and tagging feature enables OSAS to process a wide variety of data and projects while the “expert knowledge”-based tagging component enables security threat detection in a similar way to risk-based alert models.
As mentioned at the beginning, Adobe turned this project into an open source tool available on GitHub, as well as leaving available a docked variant that features WebUI and ElasticSearch OpenDistro integrations.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
