Cybersecurity specialists discovered a Windows point-of-sale (POS) malware that uses the DNS protocol to smuggle stolen credit cards, sending them to remote servers under the control of cybercriminals. This malware is installed on POS systems to monitor registered payments and, when processing a payment on a remote terminal, the malware will intercept the information from the compromised card.
Attackers collect data and use it to make fraudulent purchases, clone credit cards, or sell data on forums hosted on dark web.
When securing POS systems, it is common to block them so that they can only be connected to the protocols required for their operation. In many cases, these restrictions include blocking the HTTP protocol so that POS systems cannot connect to web servers. This restriction would prevent malware from connecting back to the command and control servers for POS malware that uses the HTTP protocol to send stolen credit cards.
However, the DNS protocol is not usually blocked, as it is required for multiple Windows services and the overall operation of a machine. That’s why the malware, identified as Alina, added the ability to use encoded DNS requests to communicate with the malicious server.
According to CenturyLink firm researchers, using a machine learning model it is possible to detect unusual DNS queries to specific domains. This is the method by which the behavior of the Alina malware was detected. When communicating with the command and control servers, the Alina malware will encode DNS queries and add them to a domain as if they were a subdomain.
When the threat actors’ C&C server receives this query, it will decode the coded subdomain to extract a PING command and inform the hackers that the malware is still running, or the information from the compromised payment card.
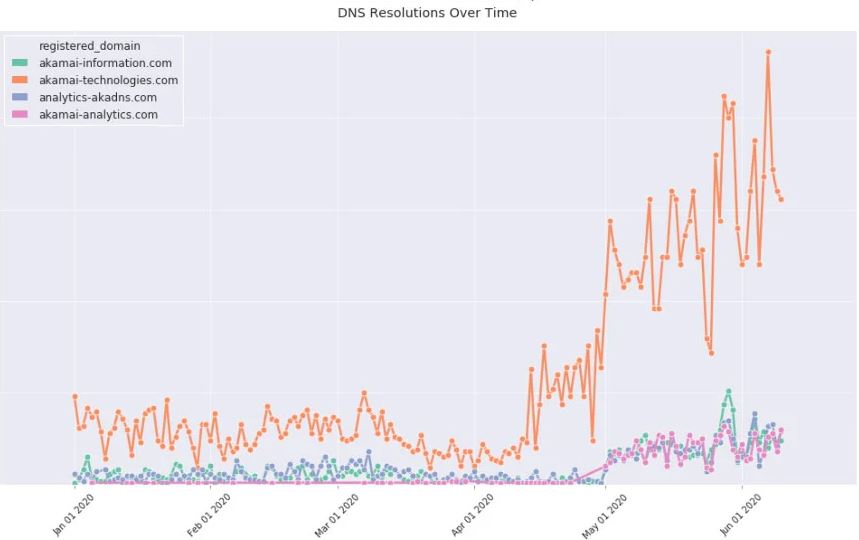
CenturyLink recommends that organizations monitor DNS traffic for repeated suspicious queries to the same domain. “We recommend that all organizations, including retailers using point-of-sale systems, monitor DNS traffic for suspicious queries,” CenturyLink suggests. It should be noted that Alina is not the only malware that uses DNS to send data to remote servers, so users of technology deployments should be wary of all potentia
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
