KillNet, a Russian hacker organization, has made the assertion that it breached the FBI’s database and stole the personal information of more than 10,000 US federal officers. This purported assault, like the most of the group’s other attacks, seems to have been motivated by political overtones, much like the majority of the group’s other attacks.
It is important to point out that a data breach occurred inside the FBI’s security platform InfraGard only the week before last. This breach resulted in the personal information of 87,000 of the platform’s users being stolen and published on the internet.
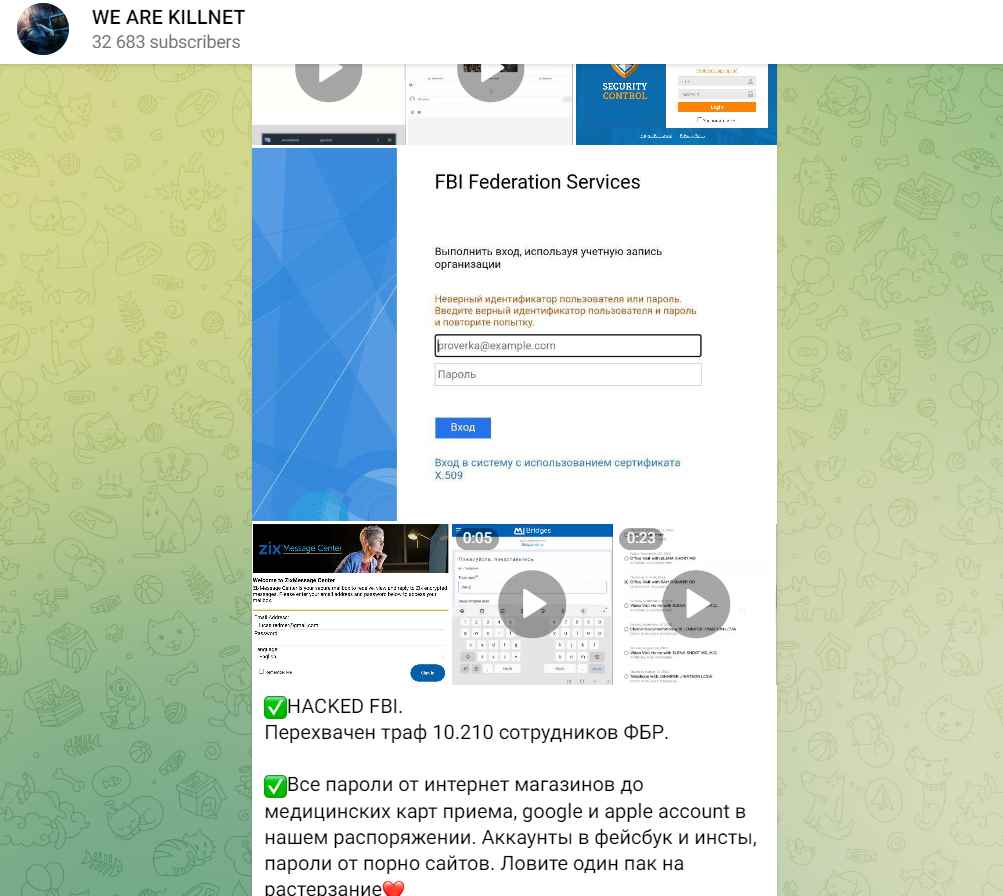
Killnet hackers claim that the data acquired includes social media passwords as well as financial information; nevertheless, the assault that was carried out by Killnet has not been validated. The gang shared photos on Telegram that revealed the passwords to various online retailers, medical ID cards, as well as accounts for Google, Apple, and Instagram.
A message that was ascribed to the hackers and published on Russian Telegram channels read as follows: “All passwords from online retailers to the mass acceptance card, Google, and Apple accounts are at our disposal.”
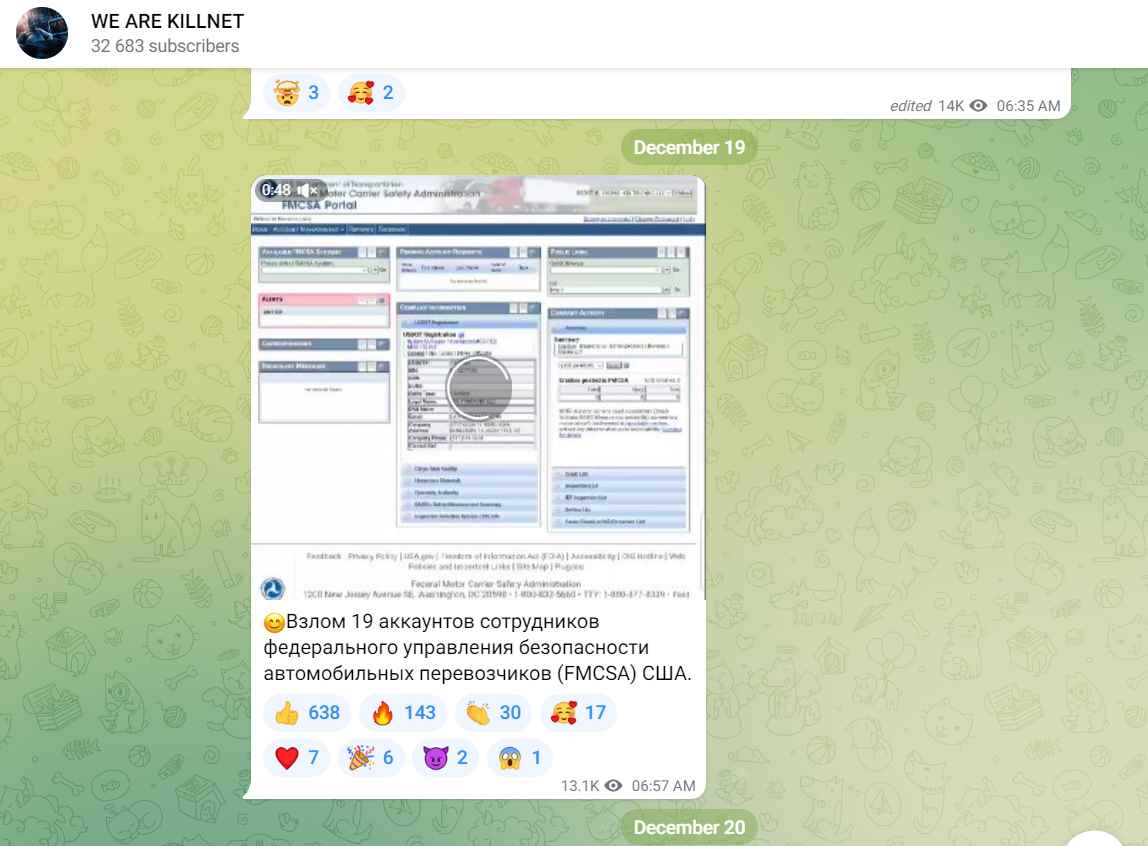
According to another screen video, the cybercriminals can be seen accessing a Facebook account that is said to belong to an employee of the Federal Motor Carrier Safety Administration (FMCSA). They demonstrate that they are in charge of the account by publishing the phrase “We are KillNet” on the profile page of the targeted individual.
Since the Russian invasion of Ukraine in February, hackers connected to the KillNet group have been behind a number of operations that have targeted Western government agencies and commercial organizations that support Ukraine.
DDoS attacks were first launched against the website belonging to Prince William in the previous month, and only a few days after, the website belonging to the European Parliament was attacked.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
