The Seiko Group, known for its timekeeping business, suffered a ransomware attack in July 2023 that led to the theft of around 60,000 items of personal data. The attackers, known as the BlackCat ransomware gang, targeted various entities within the Seiko Group, with Seiko Watch Corporation (SWC) being the most adversely affected. The data compromised included names, addresses, phone numbers, and/or email addresses of SWC customers. Additionally, information pertaining to job applicants, current and former employees of SWC, and some business transaction counterparties was also stolen during the breach.
The breach was first disclosed by Seiko on August 10, 2023, following which BlackCat claimed responsibility for the attack later that month. Initially, the extent of the data breach was unclear until BlackCat leaked what they claimed were internal documents, some of which seemed to be blueprints for watch designs. BlackCat began posting blueprints of past and future models to help Seiko evaluate the missing data.
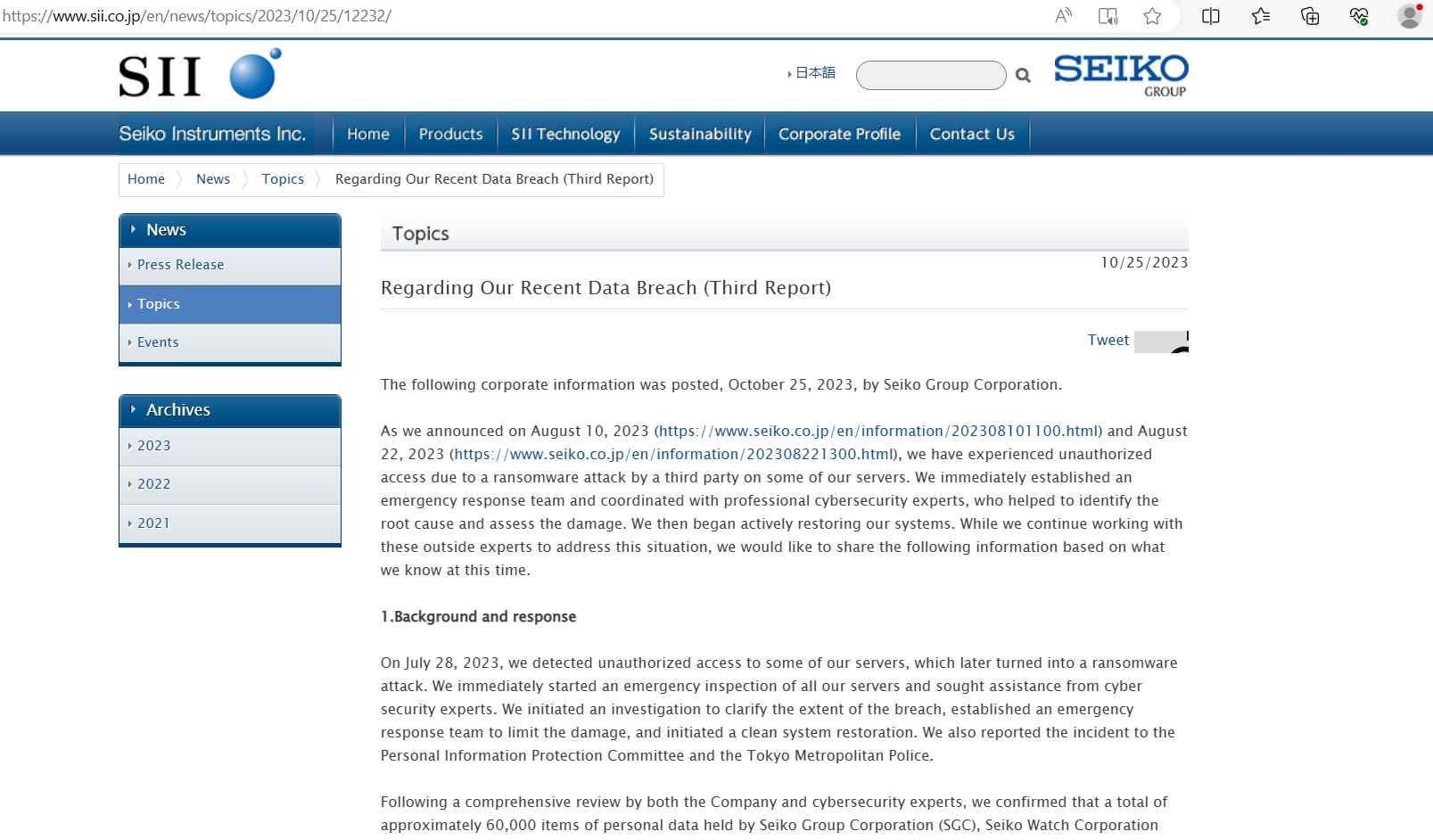
The incident was reported to the Personal Information Protection Committee and the Tokyo Metropolitan Police, hinting at the serious implications of the breach. Seiko conducted a thorough investigation alongside cybersecurity experts, which confirmed the compromise of personal data across Seiko Group Corporation (SGC), Seiko Watch Corporation (SWC), and Seiko Instruments Inc. (SII).
Despite the breach, no credit card details were accessed. The latest communication from Seiko highlighted that they are still identifying the scope of the breach and have initiated contact with the affected parties to manage the situation. They are also reviewing their IT vulnerabilities and business continuity plans to prevent similar incidents in the future.
The breach has raised concerns about the potential for further criminal activities. With the sensitive data now in the hands of criminals, there’s a risk of realistic phishing scams targeting the victims of the breach, which could also impact other organizations in the aftermath of this incident.
In a similar vein to the cyber attack experienced by Seiko, the Swatch Group and Casio a global brand specializing in the manufacture and sale of finished watches, jewelry, and related components, also fell victim to a cyber attack. Over a weekend, the Swatch Group noticed signs of a developing cyber attack on its systems, prompting a preventive shutdown of certain IT systems to mitigate the attack’s impact. Despite the shutdown, some of the company’s operations were affected, prompting Swatch to analyze the attack and implement corrective measures promptly. The company planned to file a complaint against the unknown cyber culprits and aimed to restore normalcy to its operations as soon as possible.
These incidents highlight the vulnerabilities faced by watch manufacturing companies in the digital age, where cyber attackers exploit any loopholes to gain unauthorized access to sensitive data and disrupt operations. Both Seiko and Swatch Group’s experiences underline the importance of robust cybersecurity measures and swift incident response strategies to mitigate the damage and ensure business continuity in the face of cyber threats.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
