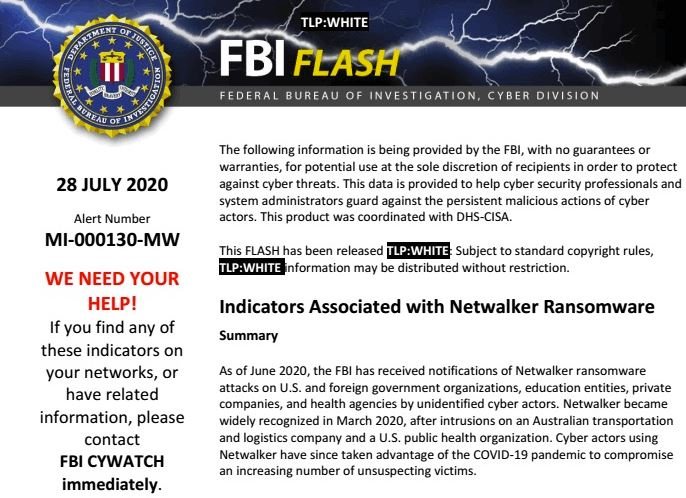
The Federal Bureau of Investigation (FBI) issued a security alert related to the Netwalker ransomware; Also identified as Mailto, this encryption malware has been detected in multiple attacks against private companies and government organizations in the U.S. and other countries.
The federal agency mentions that Netwalker operators have increased their activities since last June, when infections were reported at UCSF School of Medicine, Australian logistics firm Toll Gruop, among other companies. Federal agents also mention that threat actors also try to take advantage of the pandemic, designing phishing content to deceive unsuspecting users.
Some reports point to an increase in Netwalker attacks since April 2020, when threat actors began exploiting VPN deployments, web management interfaces, and vulnerable remote desktop protocols. The FBI adds that the vulnerabilities most exploited by this group of ransomware are CVE-2019-11510 (in Pulse Secure VPN) and CVS-2019-18935, in Telerik UI.
When vulnerabilities are exploited and the network is compromised, threat actors can employ multiple tools to collect login credentials, allowing for subsequent attacks, not to mention encryption of the affected information, the main feature of the ransomware attack.
Netwalker operators also often expose victim information: “Hacking groups that use this malware variant also often post the compromised information on cloud platforms like MEGA, or on hacking forums on dark web, trying to pressure victims to make the payment,” the agency’s report says.
Although Netwalker is one of the leading hacking groups currently, the FBI claims that by enabling a number of security measures, it is possible to significantly reduce the risk of attack. Among the main recommendations are:
- Keep antivirus solutions up to date to their latest version
- Employ VPN connections
- Supporting critical information for the organization
Finally, the agency recommends that victims refrain from paying the ransom demanded by the hackers, in addition to reporting any attack, whether successful or not, to the competent authorities.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
