A recent Google report mentions that various groups of threat actors are exploiting a vulnerability that affects Android devices with Qualcomm chips. Although the vulnerability was recently corrected, researchers mention that it is still being exploited in real-world scenarios.
The flaw was tracked as CVE-2020-11261 and received an 8.4/10 score on the Common Vulnerability Scoring System (CVSS) scale. The error lies in the graphics component in Qualcomm, which could be exploited to trigger severe memory corruption of the target system, as long as a specially designed application requests access to extensive memory resources.
This flaw was discovered by security teams for Android, which are part of Google, and reported to Qualcomm in late July 2020. Updates that fix CVE-2020-11261 were finally released in January 2021.
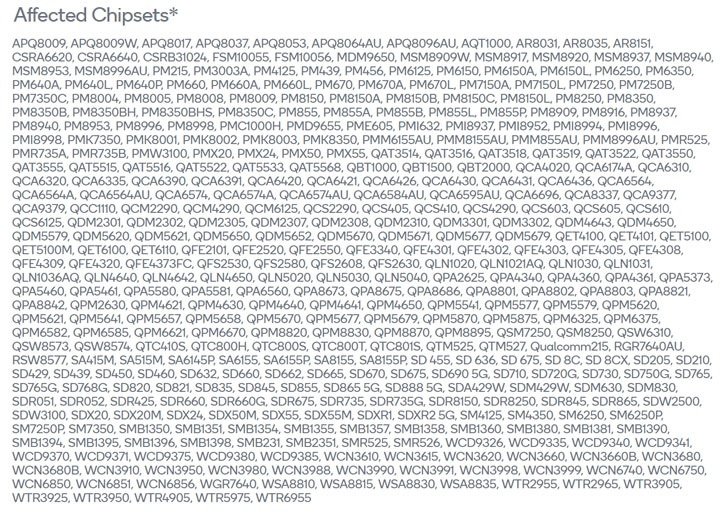
Below is a complete list of Qualcomm chip versions affected by this vulnerability:
The report is very focused on the fact that the access vector for exploiting this vulnerability is local, which means that a successful attack requires physical access to the device: “Launching a successful attack requires physical access to the device or other means, including watering hole attacks, malware infections, and other attack variants.
Because this vulnerability was recently fixed, no technical details on the exploitation of the flaw were revealed. The identity of attackers and the approximate number of vulnerable users is also unknown, although this information could be disclosed once the risk of exploitation is mitigated to a minimum.
In any case, the developers point out the need to install the monthly security updates issued by Google in due course, which is the main security method for Android. To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
