A recently published investigation revealed the presence of a dangerous vulnerability that would allow a hacker to completely control a Windows system. Previously, Microsoft had revealed some details related to the vulnerability, which was tracked as CVE-2020-0791, present in the system graphics component and that allows escalation of privileges on the target system because memory objects are not processed properly.
If exploited, this vulnerability would allow a threat actor to execute any high-privileged process, cyber security specialists say.
A hacker with local access to the target system could exploit this vulnerability by running an application specially designed to take full control of the system. In its report, Microsoft claims that a threat actor is unlikely to exploit this vulnerability by assigning it a severity level of 3.9/10.
In addition, as mentioned by the report, the vulnerability had not been publicly disclosed at the time. However, Microsoft released some security patches to address this vulnerability in March 2020. Microsoft updates and classification can be found on the Microsoft website (CVE-2020-0791).
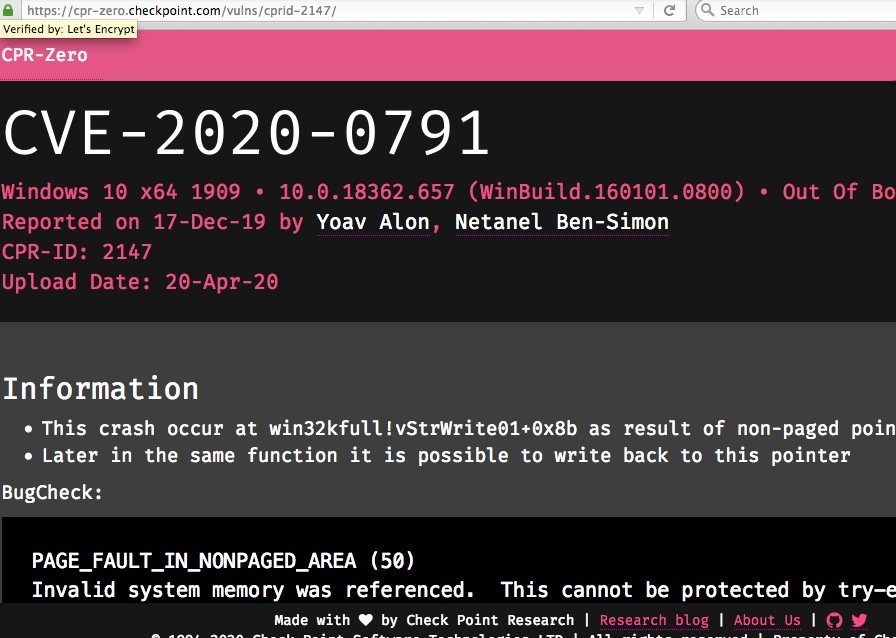
In addition to Research conducted by Microsoft, the Team of Specialists at CheckPoint Research also published some details about the Windows graphics component vulnerability (CVE-2020-0791).
According to the Check Point report, the vulnerability resides in the win32kfull.sys module and occurs in the StrechBlt function. This allows for an out-of-bounds read/write operation. Security researchers have released a proof of concept (PoC) to run on Windows 10 version 1909. If the process is executed according to the guidelines established by the experts, the attack generates a Windows system lock condition (showing only a blue screen).
Recently a group of experts also discovered a vulnerability that would allow you to dodge antivirus software on any Windows operating system device; this attack could be used to take control of some system functions and even to disable the antivirus, allowing the passage of malicious content.
Additional technical details about this vulnerability are available on the official Microsoft platform. Information on the proof of concept to exploit this flaw is also available on the official website of the researchers.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
