In the ever-evolving landscape of cybersecurity, a new vulnerability identified as CVE-2023-40547 has emerged, casting a shadow over the security of most Linux systems. This vulnerability, discovered within the shim bootloader—a cornerstone component for supporting Secure Boot—poses a critical risk, potentially allowing attackers to gain unauthorized control over the boot process of affected systems.
Understanding Shim and Its Role in Secure Boot
Shim plays a pivotal role in the Linux boot process, especially in systems utilizing Secure Boot, a security standard developed to ensure that a device boots using only software that is trusted by the Original Equipment Manufacturer (OEM). Due to licensing incompatibilities that prevent direct signing of the bootloader (GRUB2) by Microsoft, the shim bootloader was developed. Shim includes a vendor’s certificate and code that verifies and runs the bootloader, effectively bridging the gap between open-source software and Secure Boot requirements. The shim is first verified using Microsoft’s 3rd Party UEFI CA, which then loads and verifies the GRUB2 bootloader using the embedded vendor certificate.
The CVE-2023-40547 Vulnerability
Reported by Bill Demirkapi at Microsoft’s Security Response Center, CVE-2023-40547 is attributed to an out-of-bounds write vulnerability within shim’s HTTP protocol handling. This flaw can be exploited to achieve complete system compromise before the kernel loads, circumventing any security measures implemented at the operating system level. The vulnerability, maintained by Red Hat for most Linux distributions, received a CVSS score of 9.8 (Critical) by NVD and 8.3 (High) by Red Hat, underscoring its severity.
Broader Implications and Additional Vulnerabilities
While CVE-2023-40547 directly impacts shim, it’s crucial to note that this is not an isolated issue. Alongside this critical vulnerability, five additional vulnerabilities with medium severity have been disclosed, affecting various aspects of shim’s functionality, from handling PE binaries to validating SBAT information. These vulnerabilities collectively highlight the complex security landscape that developers and users must navigate.
The discovery of CVE-2023-40547 in the shim bootloader has brought to light additional vulnerabilities within the same component. Here’s a list of all five additional flaws identified alongside CVE-2023-40547, each presenting unique challenges to the security of systems utilizing shim for Secure Boot:
- CVE-2023-40546: This vulnerability addresses a flaw in the
LogError()function, specifically a NULL pointer dereference issue. This type of vulnerability can lead to denial of service (DoS) attacks or other undefined behaviors in software, potentially allowing attackers to exploit the system further. - CVE-2023-40548: Identified as an integer overflow vulnerability, this flaw occurs in the handling of the SBAT section size on 32-bit systems, leading to a heap overflow. Integer overflow vulnerabilities can result in the execution of malicious code, corruption of data, or a crash of the affected system.
- CVE-2023-40549: This vulnerability is an out-of-bounds read issue that occurs when loading a Portable Executable (PE) binary. Out-of-bounds read issues can lead to information disclosure, allowing an attacker to gain insights into system memory which might contain sensitive information or pointers that could be used in further exploits.
- CVE-2023-40550: Similar to CVE-2023-40549, this flaw also involves an out-of-bounds read, but it specifically occurs when trying to validate the SBAT (UEFI Secure Boot Advanced Targeting) information. This vulnerability could potentially be exploited to bypass Secure Boot restrictions or to disclose information that could facilitate further attacks.
- CVE-2023-40551: This vulnerability addresses a bounds check issue for MZ (Mark Zbikowski) binaries, a format used in DOS-compatible operating systems. Proper bounds checking is crucial to prevent buffer overflow attacks, and a flaw here could allow attackers to execute arbitrary code or cause a denial of service.
Each of these vulnerabilities, while scored as medium severity, underscores the complexity and importance of securing the boot process in modern computing environments. The identification and prompt remediation of these flaws are critical steps in maintaining the integrity and security of systems relying on Secure Boot technology.
Attack Vectors and Remediation Strategies
The exploitation of CVE-2023-40547 can occur through several attack vectors, including Man-in-the-Middle (MiTM) attacks intercepting HTTP boot traffic, local attacks manipulating EFI Variables or the EFI partition, and network-based attacks utilizing PXE to chain-load a vulnerable shim bootloader. The comprehensive nature of these attack paths underscores the necessity for robust security measures.
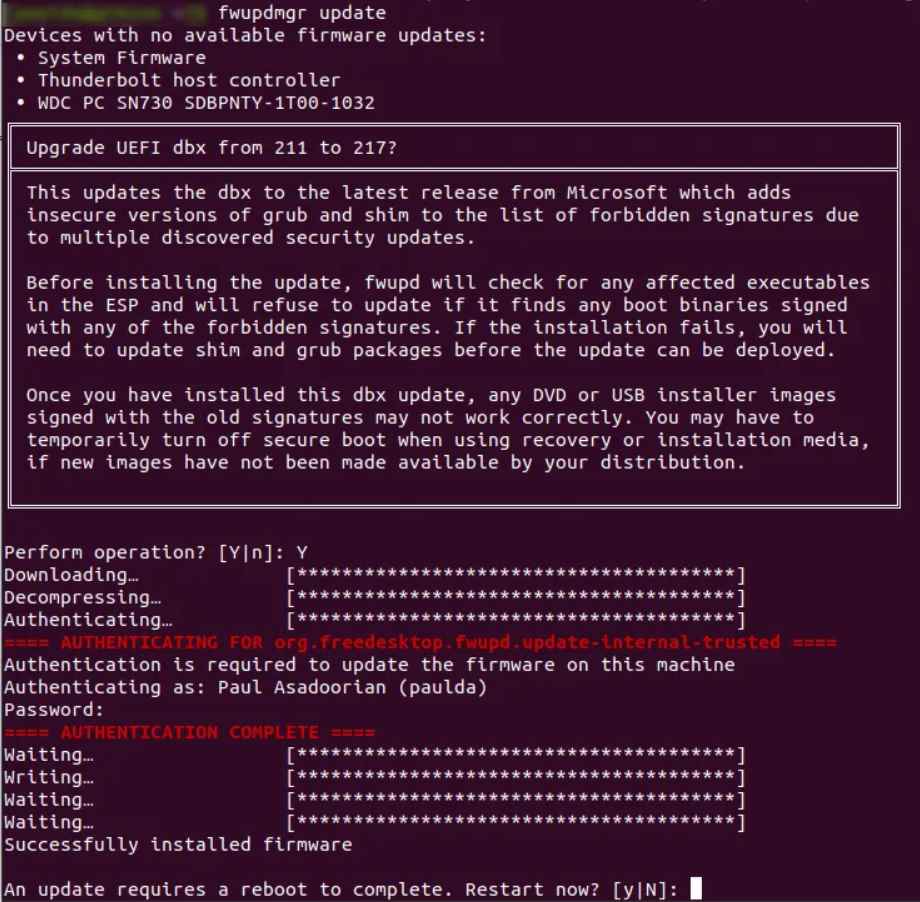
To mitigate the risks posed by CVE-2023-40547 and associated vulnerabilities, a multi-faceted approach to updating the Secure Boot chain of trust is required. This includes updating the UEFI Secure Boot DBX (revocation list) to include hashes of the vulnerable shim software and signing new, patched versions of shim with the Microsoft 3rd Party CA. Linux users are advised to first update to the latest version of shim before applying the DBX update, a process that can be facilitated using tools like fwupd.
The discovery of CVE-2023-40547 and related vulnerabilities within the shim bootloader serves as a stark reminder of the ongoing challenges in securing the boot process against sophisticated threats. The collaborative efforts of the cybersecurity community, including researchers, developers, and security firms like Eclypsium, play a crucial role in identifying, reporting, and mitigating such vulnerabilities. As the digital landscape continues to evolve, the commitment to proactive security measures remains paramount in protecting against the ever-present threat of unauthorized system access and compromise.
The incident surrounding CVE-2023-40547 not only highlights the technical intricacies and challenges of securing modern computing environments but also emphasizes the importance of community engagement and response in the face of cybersecurity threats. Through collective vigilance and action, the potential impact of such vulnerabilities can be significantly reduced, safeguarding the integrity and trustworthiness of countless systems worldwide.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
