An open-source version of the Java Servlet, JavaServer Pages, Java Expression Language, and Java WebSocket technologies is known as Apache Tomcat. This implementation was built by the Apache Software Foundation. Any vulnerability that is discovered in the software’s core presents a substantial danger to the software’s massive user base since it is so extensively used. CVE-2023-34981 is the identification number for a newly discovered information leak vulnerability in Apache Tomcat. This vulnerability, which was discovered by Hidenobu Hayashi and Yuichiro Fukubayashi of M3, Inc., represents a substantial risk and has been given the severity classification of “Important” as a result.
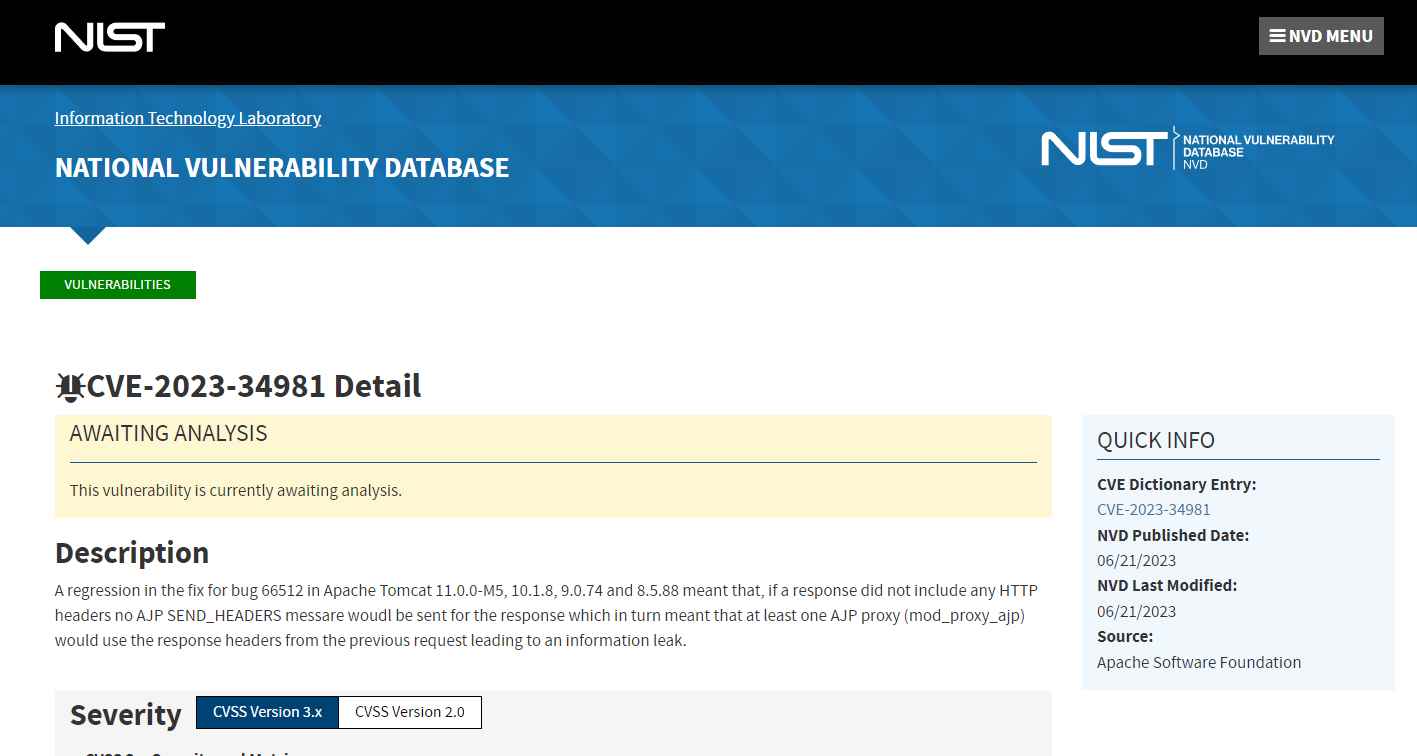
The following versions of Apache Tomcat are vulnerable to the CVE-2023-34981 vulnerability:
- Apache Tomcat version 11.0.0.M5
- Apache Tomcat version 10.1.8
- Apache Tomcat version 9.0.74
- Apache Tomcat version 8.5.88
So, how does the CVE-2023-34981 exploit work exactly? No AJP SEND_HEADERS message will be sent out if the response in question does not have any HTTP headers defined. The use of the response headers from the prior request by AJP-based proxies, such as mod_proxy_ajp, in the processing of the present request is the outcome of this behavior. What is the result? A leak of information that was not meant to be publicized might leave a business vulnerable to unlawful use.
It has been categorized as a difficult situation. A feature or two of the component Response Header Handler’s functionality may be impaired as a result. The manipulation with an unknown input results in a vulnerability that exposes confidential information. The problem is being referred to as CWE-200 by CWE. The product provides access to sensitive information to a third party that has not been expressly authorized to have access to that information. This will have an effect on the confidentiality of the information. CVE summarizes.
The bad news is that the vulnerability is substantial; however, the good news is that the Apache Software Foundation has moved quickly to remedy this problem by releasing updated versions of Tomcat that are strengthened and more secure. Upgrade is the simple advise that should be followed by users of impacted versions of the software.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
