The Apache Software Foundation is a nonprofit organization based in the United States that provides financial assistance to a variety of open-source software projects. The Apache Software Foundation (ASF) originated from a collective of individuals that worked on the Apache HTTP Server. The most recent market share statistics indicates that the Apache HTTP Server maintains its position as the most used web server on the internet. The Apache Software Foundation has announced the release of a new version of its HTTP Server web server in order to remedy a pair of security flaws. These vulnerabilities enable an attacker to smuggle requests, cause the process to crash, and trigger HTTP response splitting.
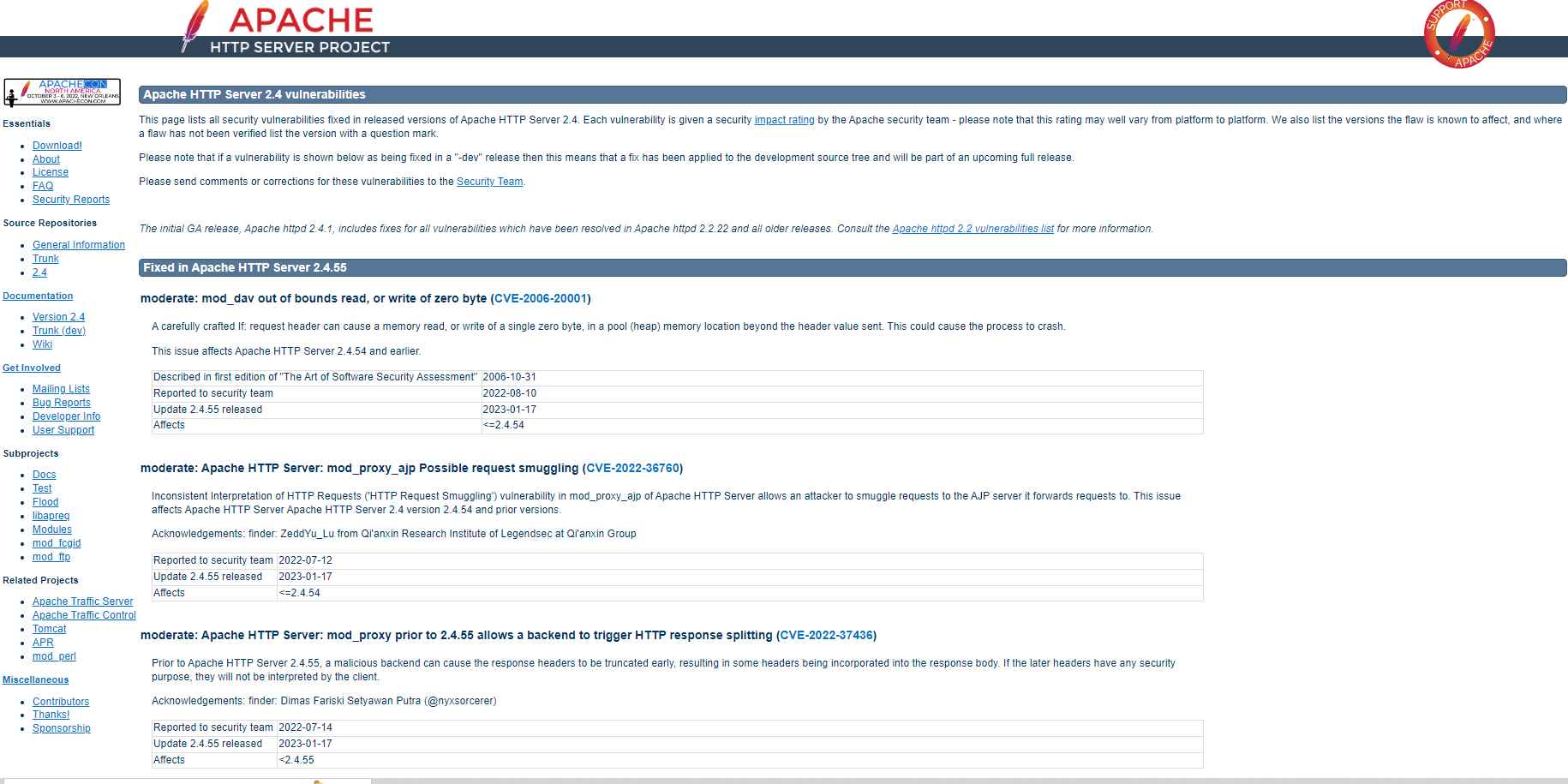
The patch addresses three security flaws that have been formally documented: CVE-2006-20001, CVE-2022-36760, and CVE-2022-37436.
In their statement, the Apache Software Foundation wrote the following:
CVE-2006-20001 — This vulnerability is rated as moderate. A well constructed If: request header may trigger a memory read or write of a single zero byte in a pool (heap) memory address that is beyond the header value that was delivered. This can happen even if the header value was not transmitted. This may result in the process being corrupted.
CVE-2022-36760 – This vulnerability known as “Inconsistent Interpretation of HTTP Requests” or “HTTP Request Smuggling” exists in the mod proxy ajp component of the Apache HTTP Server. This vulnerability enables an attacker to smuggle requests to the AJP server to which it passes requests.
CVE-2022-37436 – This vulnerability is considered moderate. Before the release of Apache HTTP Server version 2.4.55, a malicious backend may cause the response headers to be truncated early, which would then result in certain headers being included into the response body. This issue was fixed in the latest version of Apache HTTP Server. The latter headers will not be evaluated by the client since security is the reason for why they were included.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
