A former employee of technology firm Cisco has been accused of remotely accessing the company’s cloud infrastructure in order to install a code that closed more than 16,000 WebEx Teams accounts and deleted 456 virtual machines, all made five months after submitting their resignation. The defendant has already pleaded guilty.
In his statement, Sudhish Kasaba Ramesh, 30, acknowledges having accessed the company’s cloud infrastructure, hosted on Amazon Web Services (AWS) unauthorizedly in September 2018. During this unauthorized access the individual injected a code from their Google Cloud Project account to perform some malicious tasks, such as deleting the virtual machines for the WebEx Teams video conferencing and messaging application, mention the court documents.

As a result, more than 16,000 application accounts were also temporarily closed, forcing Cisco to invest about $2.4 million USD to restore the compromised resources.
After an investigation, prosecutors determined that user data was not compromised. Regarding the defendant, Ramesh admits that his actions were reckless, as he ignored the risk he could cause by injecting code into the Cisco cloud. The company began correcting the problem as soon as it was detected, preventing the attack from causing further damage, as well as notifying the relevant authorities of the incident.
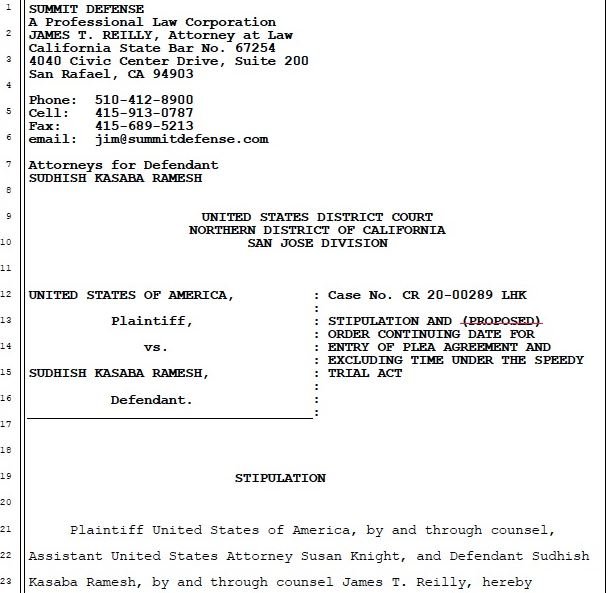
The defendant was released after posting a $50,000 USD bail and handing over his passport to the authorities. Ramesh is awaiting his sentencing hearing, scheduled for December 9. If found guilty, the individual faces a sentence of up to 5 years in prison and a $250,000 USD fine for the crime of intentional access to a protected computer without authorization, in addition to reckless damage.
It should be noted that the accused has a pending citizenship application, so he could be deported to India, his native country, if found guilty. º
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
