Even though ransomware is still one of the top cyber security issues for businesses today, ransomware defense is ineffective.
Organizations have historically relied on a mix of people, process, and technology to thwart security threats, from routine software patches and backups to threat modeling and password awareness. However, these strategies by themselves are insufficient to successfully reduce extremely complex ransomware attacks.
As a result of the misconception that ransomware is a technological or organizational issue rather than an economic one, ransomware defense is failing. The transportation and dissemination of data are crucial to the functioning of most global economies, therefore it is urgent that we examine our digital infrastructure with the same seriousness as our vital physical infrastructure. However free ransomware decryptors can help the business and people a lot.
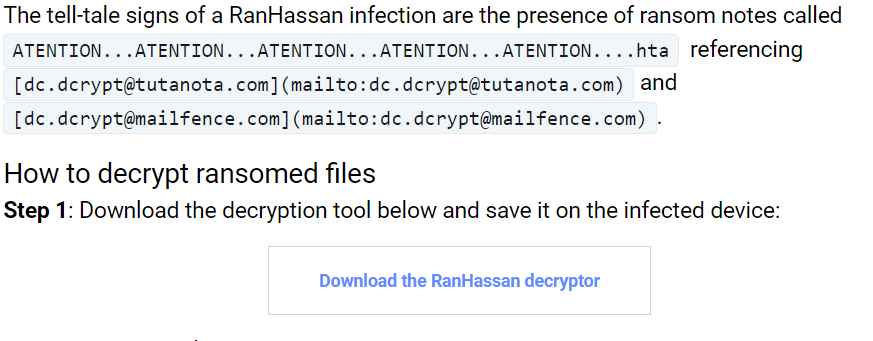
Now you may obtain a fresh decryptor for the RanHassan ransomware from Bit Defender. This family of ransomware, which was first discovered in May 2022, appears to predominantly target victims in India and Arab-speaking nations. A RanHassan infection can be identified by the existence of ransom note known as
ATENTION...ATENTION...ATENTION...ATENTION...ATENTION....hta referencing [dc.dcrypt tutanota com](mailto:dc.dcrypt tutanota com) and [dc.dcrypt mailfence com](mailto:dc.dcrypt mailfence com)
Visit the bit defender site to get the decryption tool, then save it on the infected device. Start the tool and agree to the end user license terms. To search for encrypted files, choose a folder, or let the program search through all of the system’s data. You require at least one encrypted file and its unencrypted counterpart for the program to identify the proper keys.
Once the decryption process has begun, let the program continue to work until all files have been unlocked.

A command line can also be used to run the utility silently. If you need to install the program on a wide network automatically.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
