Okta, a firm that ensures security, has been compromised, and the perpetrators of the hack seem to have stolen the company’s source code.
Theft of source code is a serious problem, particularly in the area of computer security solutions. Although user data in and of itself is undoubtedly more valuable, thieves might utilize Okta’s source code to discover hidden vulnerabilities and conduct further attacks against consumers. Okta is a famous supplier of authentication services.
Okta has had a difficult year in terms of security, beginning with a breach that was associated with the ransomware gang Lapsus$ in January. However, the business didn’t reveal the attack until March of this year. It subsequently agreed that postponing the statement had been a’mistake,’ but it added that the breach had been at a third-party provider known as Sitel rather than anywhere inside its own network.
In April, Okta disclosed that the security breach that occurred in January lasted for “25 straight minutes,” and the company also reduced the scope of the harm, stating that it was restricted to only two clients.
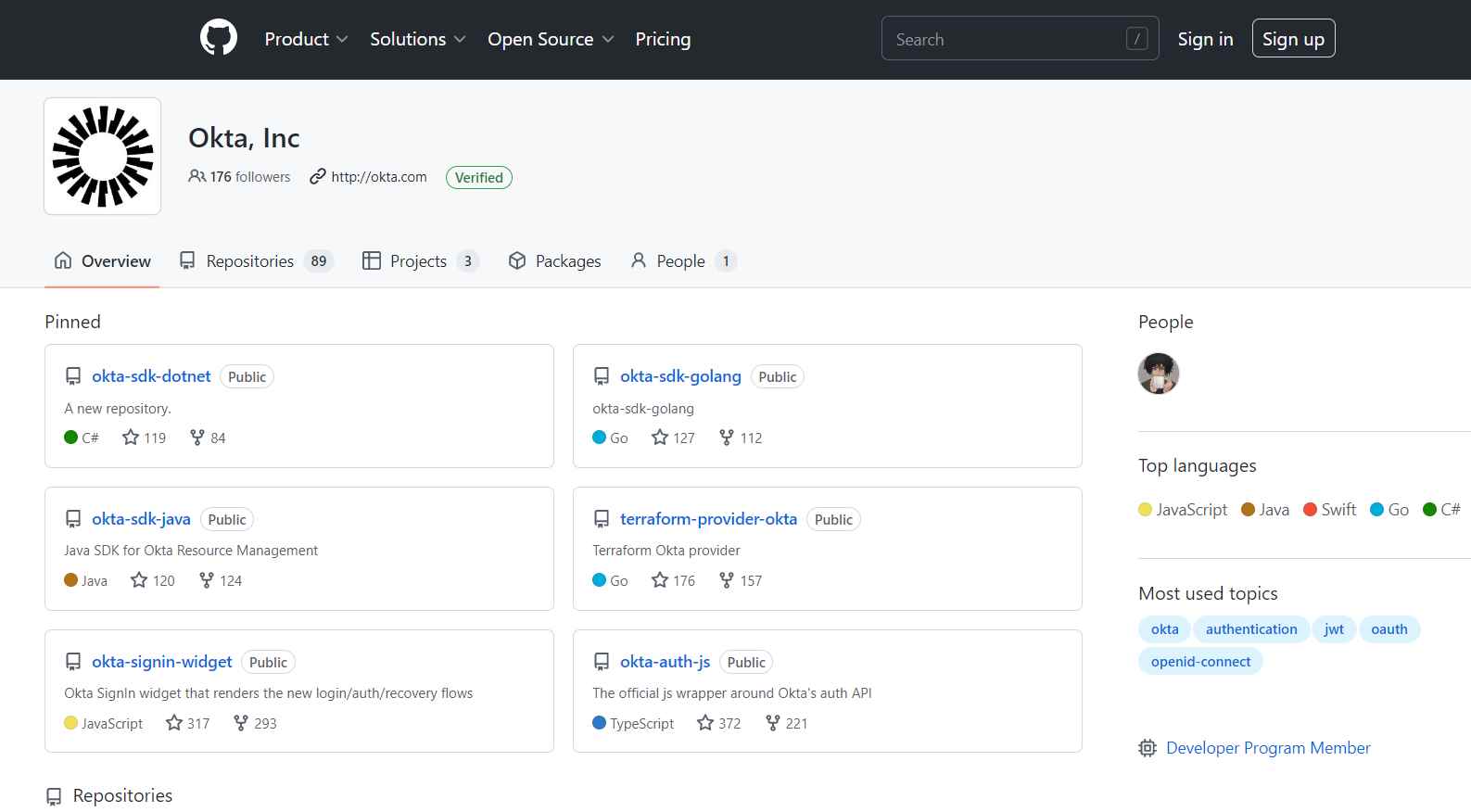
Nevertheless, the problems persisted beyond that point. In September, hackers broke into Okta subsidiary Auth0 and targeted the company’s source code. The hackers’ method of attack was similar to the one used in today’s incident.

According to a ‘secret’ letter that the corporation has issued to its ‘security contacts,’ the company claims that hackers broke into its GitHub repositories early this month. The authenticity of the notice was validated by BleepingComputing.
According to David Bradbury, Okta’s Chief Security Officer, who was quoted in the message, no customer data was compromised. This includes data belonging to “HIPAA, FedRAMP, or DoD customers,” which are organizations based in the United States that are involved in the healthcare, government, or defense sectors.
Early in the month of December, GitHub notified Okta that there had been “potential suspicious access” to their code repositories, as noted by Bradbury. Okta conducted an investigation, and the results led them to the conclusion that the access had been utilized to copy the aforementioned repositories. Nevertheless, neither the Okta service nor the data belonging to its users were accessed in an unauthorized manner.
As an additional line of defense, Bradbury added, “Okta does not depend on the secrecy of its source code for the security of its services,” obviously in an effort to allay the worries that were warranted.
At the time of this writing, it seems that the security compromise only affected Okta’s Workforce Identity Cloud product and not Auth0’s Customer Identity Cloud.
At the conclusion of his presentation, Bradbury emphasized Okta’s “commitment to openness.” Later on today, the corporation is going to issue a statement about the event that just occurred.
To: People in Charge of Security
I would want to provide some background information and specifics on a recent security incident. Please be aware that we have verified that there has been no illegal access to the Okta service as well as no unlawful access to the data of our customers. There will be no effect on any clients, including those regulated by HIPAA, FedRAMP, or the Department of Defense. The Okta service continues to function normally and securely even if customers are not obliged to take any action.
At the beginning of December 2022, GitHub informed Okta that there may have been unauthorized access to Okta’s development repositories. After conducting an investigation, we have come to the conclusion that someone with such access copied Okta code repositories.
After conducting this examination, we came to the conclusion that there was no illegal access to the Okta service or to the customer data of any users. Okta does not place any reliance on the secrecy of its source code in order to ensure the safety of its services.
As soon as Okta became aware of the potentially malicious access, we swiftly put temporary limitations on access to Okta’s GitHub repositories and halted any integrations of GitHub with third-party apps.
Since then, we have rotated GitHub credentials, reviewed all recent access to Okta software repositories hosted by GitHub in order to understand the scope of the exposure, reviewed all recent commits to Okta software repositories hosted with GitHub in order to validate the integrity of our code, and reviewed all recent access to Okta software repositories hosted with GitHub. We have also informed the appropriate authorities.
In addition, we have ensured that this code cannot be utilized to get access to any corporate or client environments by taking the necessary precautions. As a consequence of this occurrence, Okta does not foresee any interruption to either the operation of our company or our capacity to provide service to our clients.
Note that this particular vulnerability incident refers to the code repositories for Okta Workforce Identity Cloud (WIC). It has nothing to do with any of the solutions offered by Auth0 (Customer Identity Cloud). Because of our dedication to being transparent and working in cooperation with our clients, we have come to the conclusion that it is in everyone’s best interest to provide this information.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
