Information security specialists report the detection of a critical vulnerability in Composer, a package management system for programming in PHP that provides the standard formats necessary to handle PHP dependencies and libraries. Successful exploitation of this fault could result in a high-risk scenario for those affected.
Tracked as CVE-2022-24828, the vulnerability exists due to incorrect input validation within the VcsDriver::getFileContent() method when parsing arguments $file or $identifier. This could be leveraged by remote threat actors to pass specially crafted data to the application and execute arbitrary operating system commands on the affected system.
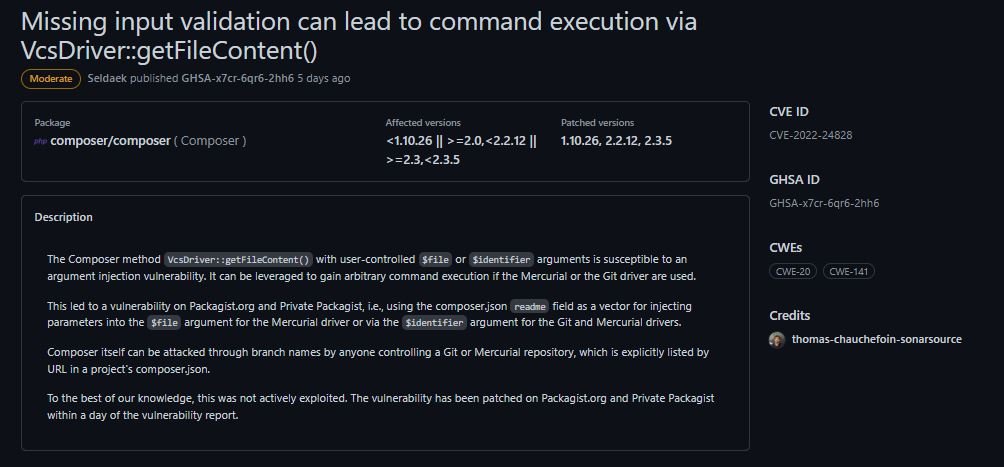
The flaw received a score of 8.5/10 according to the Common Vulnerability Scoring System (CVSS) and can only be exploited if the Mercurial or Git driver is used. Successful exploitation of the flaw could lead to the total compromise of the vulnerable system.
According to the report, the flaw resides in all versions of Composer between 1.0.0 and 2.3.4.
While the flaw could be exploited by remote threat actors not authenticated over the Internet, so far no active exploitation attempts or the existence of a malware variant linked to the attack have been detected. Still, users of affected deployments are encouraged to upgrade as soon as possible; the corresponding patches are now available.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
