A significant vulnerability has been discovered in Foxit PDF Reader, a well-liked alternative to the PDF software developed by Adobe. The JavaScript interface that is made available inside the software’s exportXFAData function is where the issue may be found. This approach has accidentally revealed a potentially harmful vulnerability in the security system, which may enable a remote attacker to run arbitrary code on the computer of the victim.
Because the victim’s participation is required for the exploitation process, a prospective aggressor would have to persuade the target to visit a malicious website or open an infected file in order to succeed in their mission. Because of this, the risk factor associated with this vulnerability is considerably increased when the victim is susceptible to social engineering.
A critical security hole, identified as CVE-2023-27363 in Foxit PDF Reader as a result of a discovery made by a well-known security researcher by the name of Andrea Micalizzi, also known as rgod in the cybersecurity community. This vulnerability, which has an impressive CVSS score of 7.8, illustrates the possibility for remote code execution, putting millions of people at risk of a cyberattack that could be very damaging.
Because Foxit PDF Reader is so widely used across a variety of industries, including businesses and educational institutions, the revelation of this vulnerability has caused the community of cybersecurity professionals to express some degree of alarm. It highlights how important secure coding methods and thorough vulnerability testing are in the creation of software.
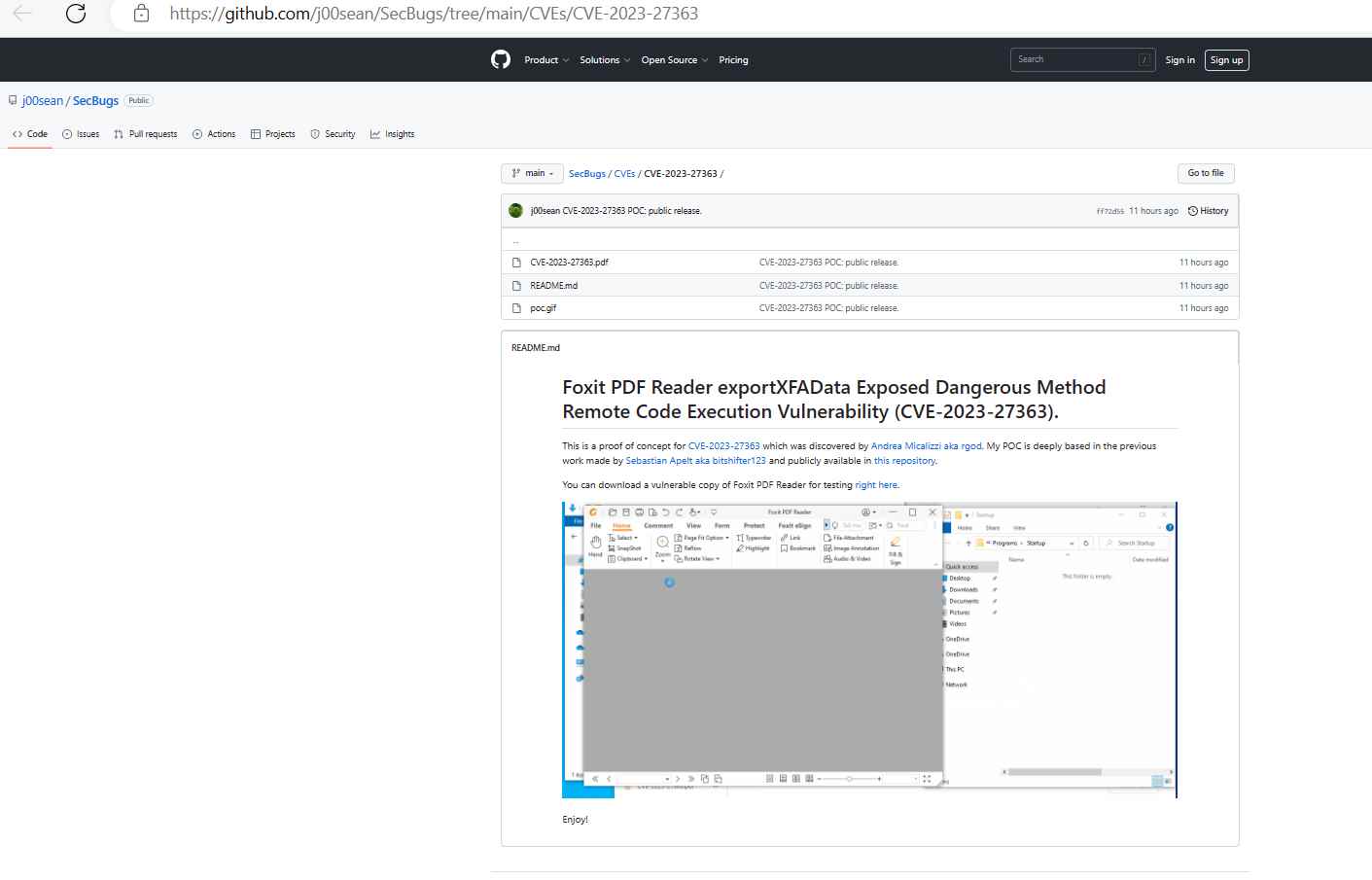
The security researcher known as j00sean has only recently made public a proof-of-concept (PoC) for the vulnerability known as CVE-2023-27363. The proof-of-concept publication is a crucial step in understanding this vulnerability and mitigating its effects. Now that the proof of concept has been developed, security teams are able to reproduce the exploit, which enables them to get a deeper understanding of the attack’s underlying mechanisms and devise more efficient mitigation strategies. A proof-of-concept for CVE-2023-27363 may be found on Github.
The specific issue may be found in the exportXFAData function. As a result of an oversight, Foxit PDF Reader exposes a JavaScript interface that is able to write to arbitrary file types. This oversight is what leaves the program open to malicious assault in the first place. This vulnerability may be exploited by an attacker to run code in the context of the currently logged-in user, giving them unauthorized access over the system.
Nevertheless, the fact that the proof-of-concept was made public indicates that threat actors now have access to the exploit specifics. As a consequence of this, it is of the highest significance for individuals and companies who use Foxit PDF Reader to install patches and upgrades that address this vulnerability.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
