The fast-paced modern world has made online shopping and selling an essential component of our everyday life. PrestaShop has distinguished itself as the foremost Open Source eCommerce web application thanks to its quick development and rising popularity. It offers an amazing shopping cart experience for both merchants and consumers. As of right now, about 300,000 online businesses all over the globe rely on PrestaShop for their commercial requirements.
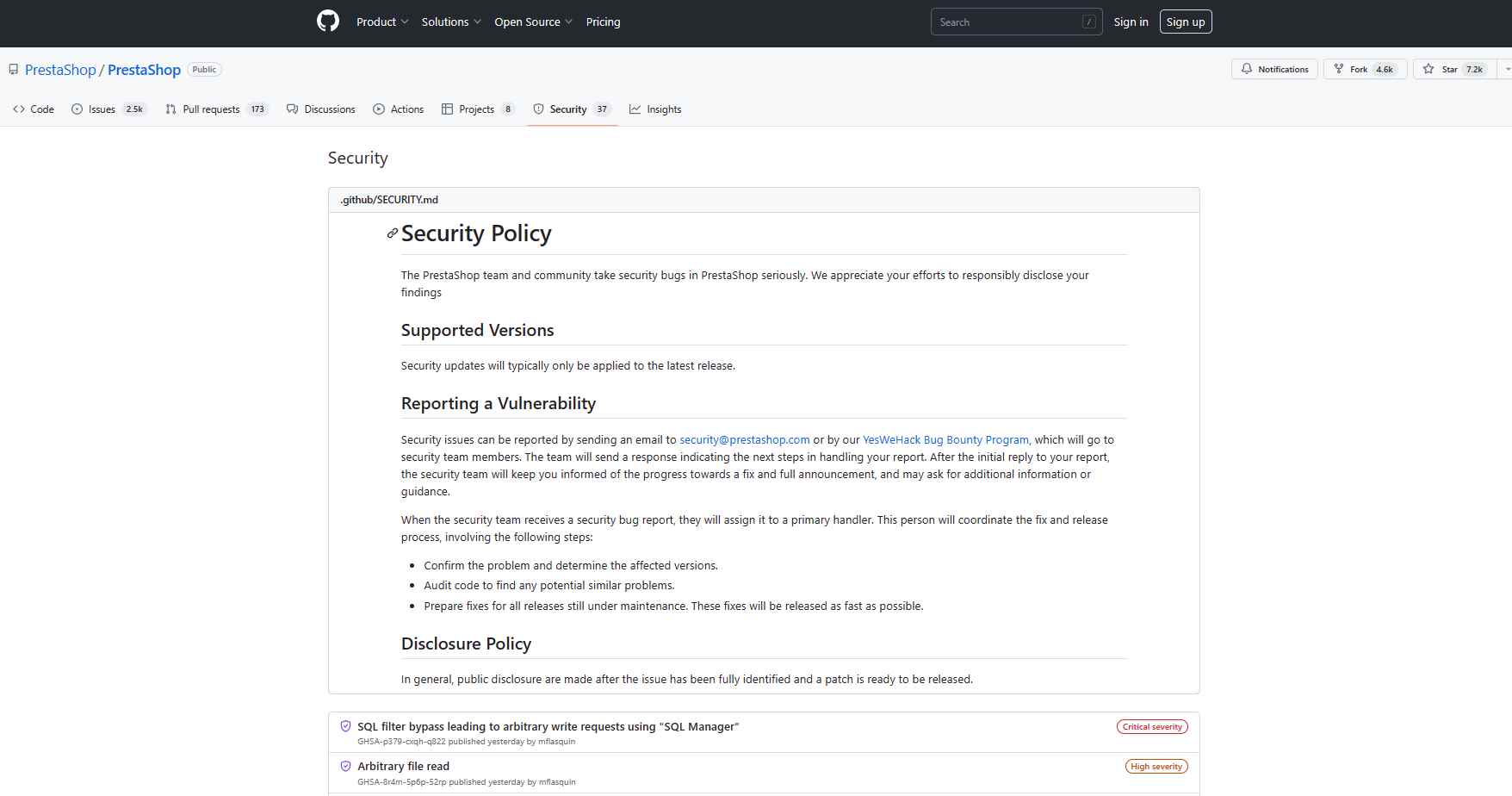
On the other hand, security flaws are always a possibility with software of any kind. There were recently found security flaws in PrestaShop, and all three of them have the potential to affect your online business.
CVE-2023-30839
SQL Filter Bypass That Can Lead to Arbitrary Write Requests, Also Known as CVE-2023-30839
This vulnerability has been given a score of 9.9 on the CVSS scale, which indicates that it is critical. A user in the back office may write, edit, and remove data in the database even if they do not have the proper rights thanks to this feature. This might result in unauthorized changes being made to the data stored in your online shop, which could do a great amount of harm to your company. The fix for this security flaw will be included into PrestaShop versions 8.0.4 and 1.7.8.9 when they are released.
Sadly, there is no way around the CVE-2023-30839 problem that can be used as a workaround. It is very necessary to upgrade your PrestaShop installation as soon as a patch is made available to do so.
Arbitrary File Read, also known as CVE-2023-30545
This vulnerability has been given a score of 7.7 on the CVSS, which indicates that it poses a high risk. This vulnerability may be exploited by a person who has access to the SQL Manager in order to read any file on the operating system by utilizing the SQL function LOAD_FILE in conjunction with a SELECT request. This may result in unauthorized access being gained to sensitive information, such as database passwords, encryption keys, or other essential files. The fix for this security flaw will be included in PrestaShop version 8.0.4 and version 1.7.8.9 when it becomes available.
XSS Injection Through the Validate::isCleanHTML Method, a CVE-2023-30838 Vulnerability
The CVSS score for this vulnerability is 8.0, which indicates that it poses a high risk. It arises because the ValidateCore::isCleanHTML() function fails to catch hijackable events, which makes it possible for XSS injection to occur. The vulnerability is especially hazardous due to the fact that it may hijack any HTML element without requiring any input from the user, which increases the likelihood of an attack being successful. The fix for this security flaw will be included into PrestaShop versions 8.0.4 and 1.7.8.9 when they are released.
It is of the utmost significance that the security of your online shop be maintained. It is very essential, in order to provide your consumers with a safe and secure online shopping experience, that you remain aware about any vulnerabilities and take the necessary actions to patch them. By bringing your installation of PrestaShop up to date with the most recent versions (8.0.4 or 1.7.8.9), you can safeguard your company from these vulnerabilities and ensure that you continue to provide consumers with a service that is consistent, frictionless, and dependable.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
