Cisco announced the fixing of a zero-day vulnerability in the software of its XR IOS routers whose exploitation would have allowed unauthenticated threat actors to remotely access Redis instances running in NOSi Docker containers. The affected software resides on multiple Cisco router platforms, including the NCS 540 and 560, NCS 5500, 8000, and AST 9000 series.
Tracked as CVE-2022-20821, the vulnerability was discovered while Cisco Technical Assistance Center (ATC) was solving a case. The researchers detail that the flaw exists because the status check RPM opens TCP port 6379 by default at the time of activation.
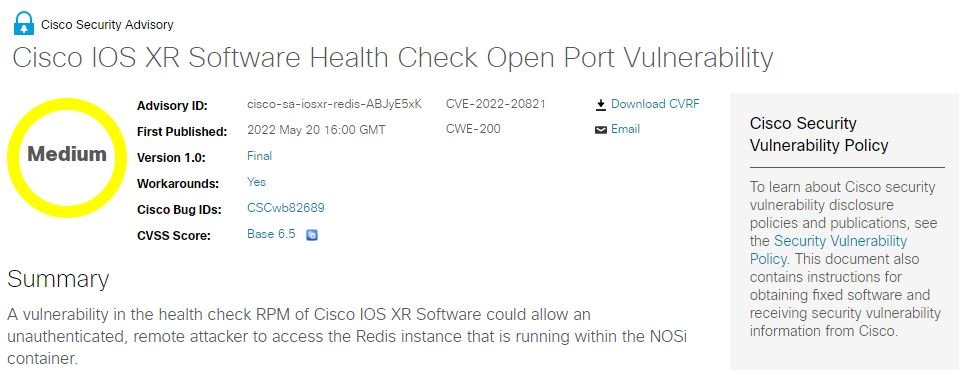
Malicious hackers can connect to the Redis instance on the open port by exploiting this error, allowing writing to the Redis in-memory database, writing arbitrary files to the container file system and retrieving information over the Redis database.
Although the bug might seem critical, the good news is that even if a malicious hacker managed to exploit the vulnerability, it would be impossible to execute remote code or compromise the integrity of the host system because Redis instances run in sandboxed containers.
The vulnerability only affects 8000 Series routers, as the verification RPM is installed and active in these products. However, the company has asked customers of all the aforementioned products to apply the recently released patches, or implement alternative solutions according to their considerations.
Cisco also confirmed that some active exploitation attempts have been detected, so it invites users to apply the necessary measures to mitigate the risk of attack as soon as possible.
For administrators who are unable to update their devices at this time, a workaround requires disabling health checking and removing the verification RPM on vulnerable devices. To find out if your devices are affected, run the docker ps command and look for a container called NOSi.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
