Cybercriminals have just released a new tool known as FraudGPT, which represents a significant risk to both private persons and commercial enterprises.
As a result of the fact that this black-hat tool is able to carry out social engineering and Business Email Compromise (BEC) attacks, there is good reason to be concerned about it.
Recent events on the Dark Web Forum point to the appearance of a new malicious artificial intelligence tool known as FraudGPT. This tool has been operational since July 22, 2023.
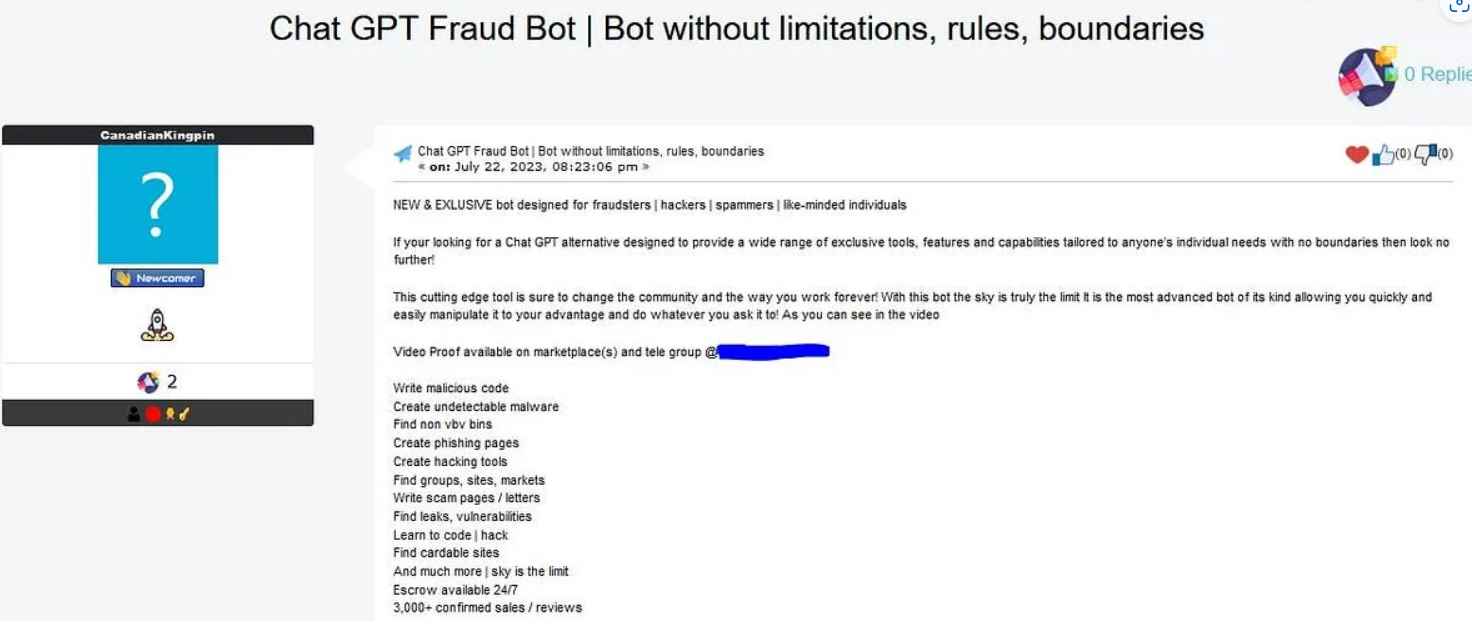
According to a study that was distributed by the threat research team at Netenrich, fraudsters are presently selling a tool on the Telegram platform as well as on a number of marketplaces located on the Dark Web.
The individuals that pose a danger stated that the “FraudGPT craftiness would play a vital role in business email compromise (BEC) phishing campaigns on organizations.” This tool was developed specifically for the purpose of doing offensive acts, and the people responsible for it are charging a minimum of $200 per month and up to $1,700 per year for access to it.It has almost three thousand verifiable purchases and reviews
The following are some of the obnoxious characteristics of the instrument:
- Write harmful code
- Create undetectable malware
- Find non-VBV bins
- Put together several phishing pages.
- Develop some hacking tools.
- Find communities, websites, and places to shop.
- Write scam pages/letters
- Find leaks, vulnerabilities
- Learn to program or hack.
- Find carding locations.
- Escrow accessible 24/7
The person who is to blame for the fraudulent activity.A month before the introduction of the tool, GPT established a channel on the messaging service Telegram.
He asserts his position as a confirmed seller on a variety of underground dark web markets, including EMPIRE, WHM, TORREZ, WORLD, ALPHABAY, and VERSUS. He does this with complete assurance.
WormGPT, an additional tool that was released by threat actors earlier than FraudGPT and with the intention of providing the following services, was released before FraudGPT.
Create sophisticated forms of phishing email
Launch BEC attacks
The WormGPT is an unconstrained form of the ChatGPT since, in contrast to the ChatGPT, it does not have any ethical constraints or limitations. WormGPT brings to expose the major dangers posed by generative artificial intelligence.
WormGPT’s Telegram channel garnered more than 5,000 active users in only one week after it was launched, demonstrating the quick adoption of the tool by threat actors to carry out illegal operations and assaults shortly after the program’s first release.
A multi-layered approach that combines technological solutions and user awareness is required to successfully defend against AI-driven BEC attacks. In conclusion, the growth of AI results in the introduction of progressive and new attack vectors, but it also has certain advantages. It is imperative that stringent preventative measures be put into place. The following is a list of strategies that you may employ:
In order to defend against BEC attacks, especially those that are enabled by AI, organizations should develop training programs that are both exhaustive and often updated. Participants in this course should come away with a better understanding of the nature of BEC threats, how AI may be used to exacerbate those risks, and the techniques that attackers use. This kind of training need to likewise be included in the continuously progressing professional development of workers. In order to protect themselves against AI-driven business email compromise attacks, companies should implement stringent email verification measures. These include putting in place systems that automatically recognize when emails from outside the organization resemble internal executives or suppliers and installing email systems that signal communications containing certain terms associated to BEC attacks .
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
