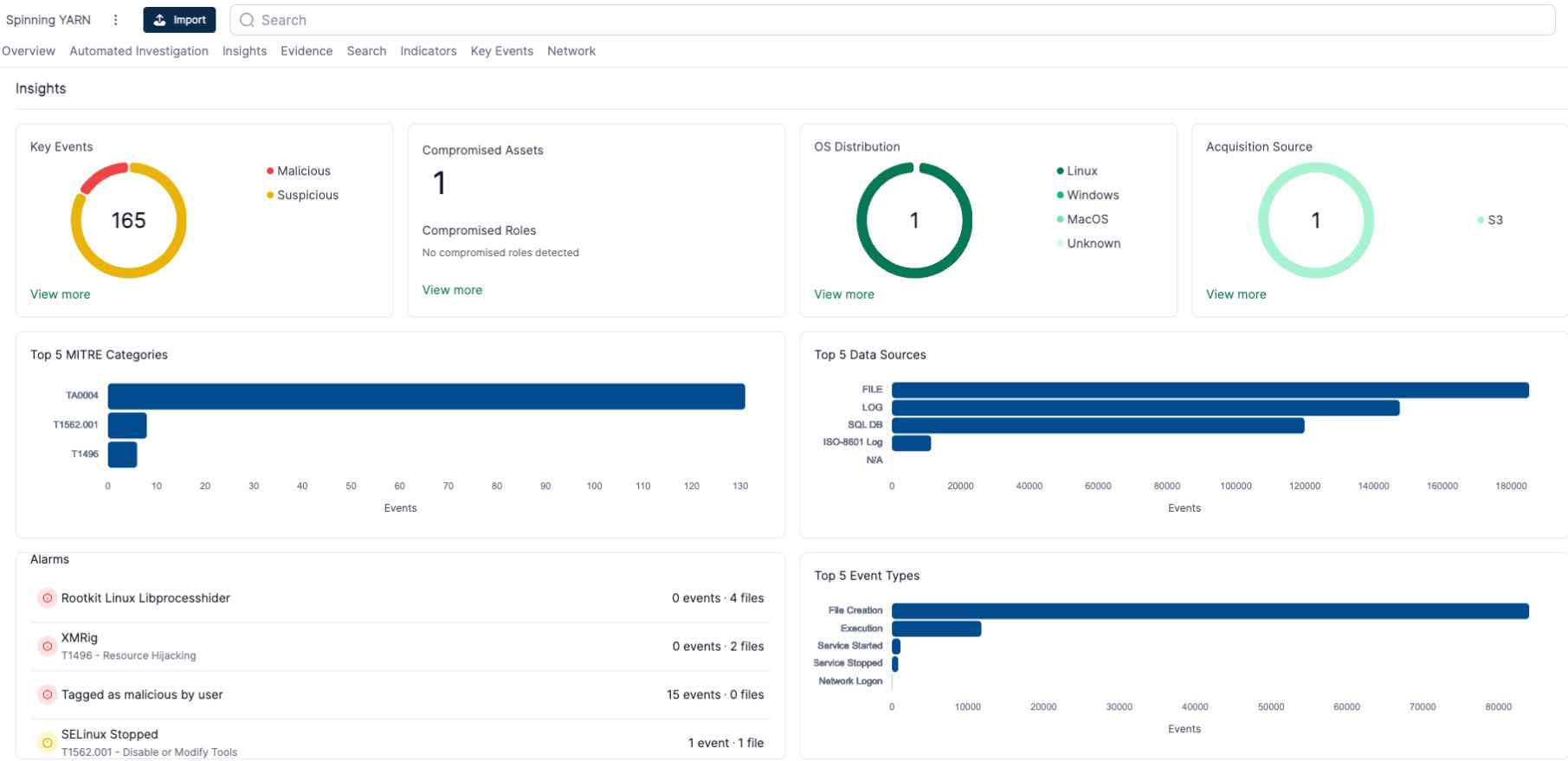
How HTTP/2 CONTINUATION Flood Vulnerability Lead to CPU Exhaustion, Memory Overflow & Evasion of Logging
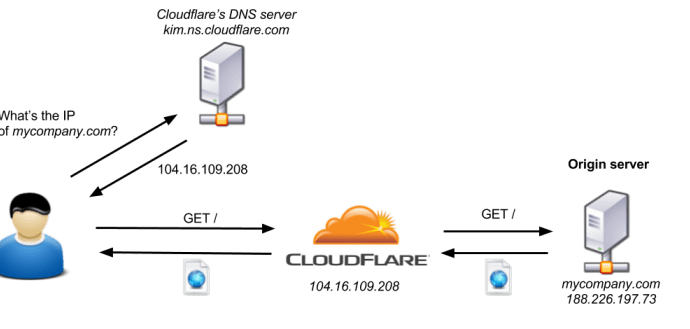
In a groundbreaking analysis, security researcher Bartek Nowotarski has detailed a new class of vulnerabilities within the HTTP/2 protocol, known as the CONTINUATION Flood. This technical deep dive into HTTP/2‘sRead More →