Timeless Targets: After Casio, Seiko Group hacked again by Ransomware gang
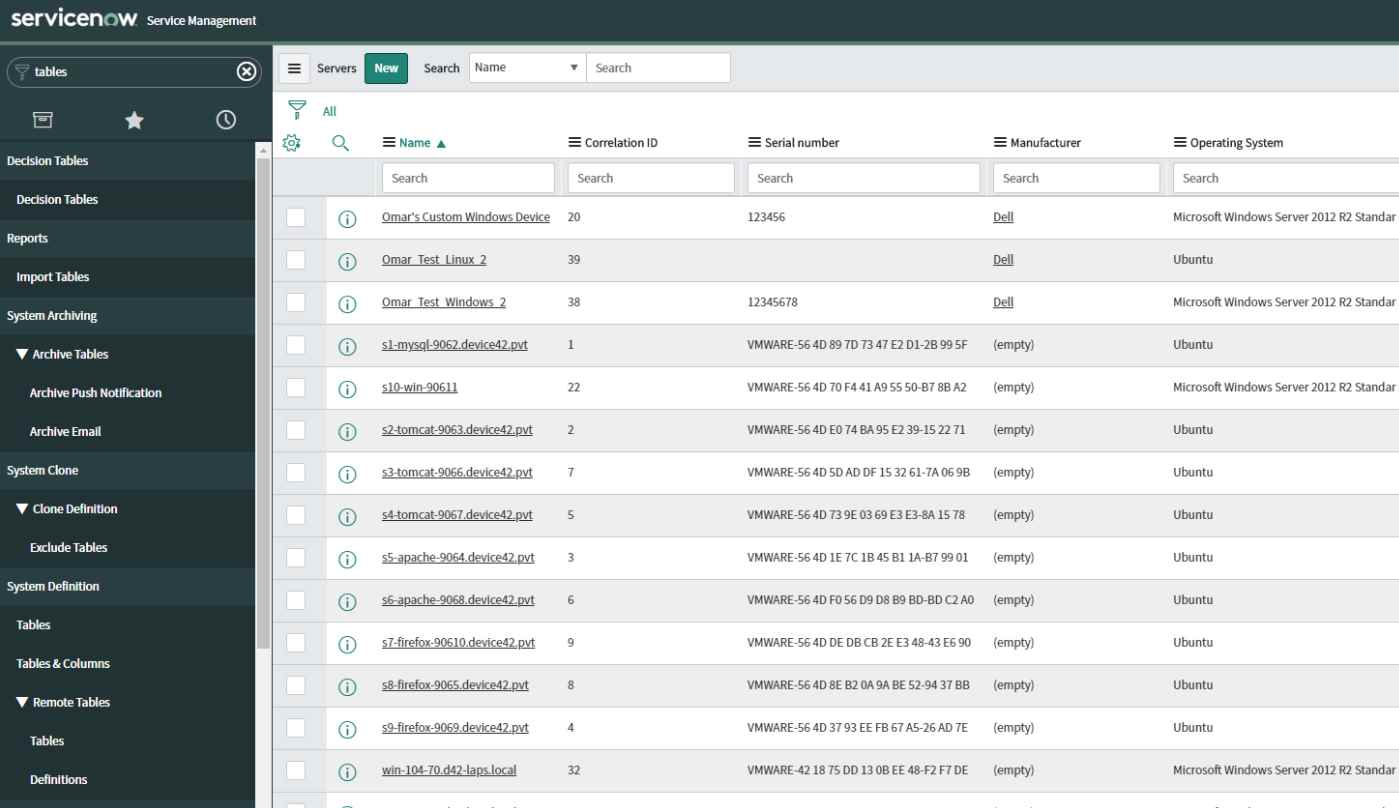
The Seiko Group, known for its timekeeping business, suffered a ransomware attack in July 2023 that led to the theft of around 60,000 items of personal data. The attackers, knownRead More →