It is well known that KeePassXC, an open-source password manager that is used by a lot of people, is known for having solid security features and the capacity to secure sensitive user information. On the other hand, new investigations conducted by CyberCitizen.tech have revealed concerns over modifications made to the security settings of the KeePassXC-Database. When making changes to security settings, it has come to the attention of CyberCitizen and other users that a confirmation through the master password or the configured second factor is not necessary.
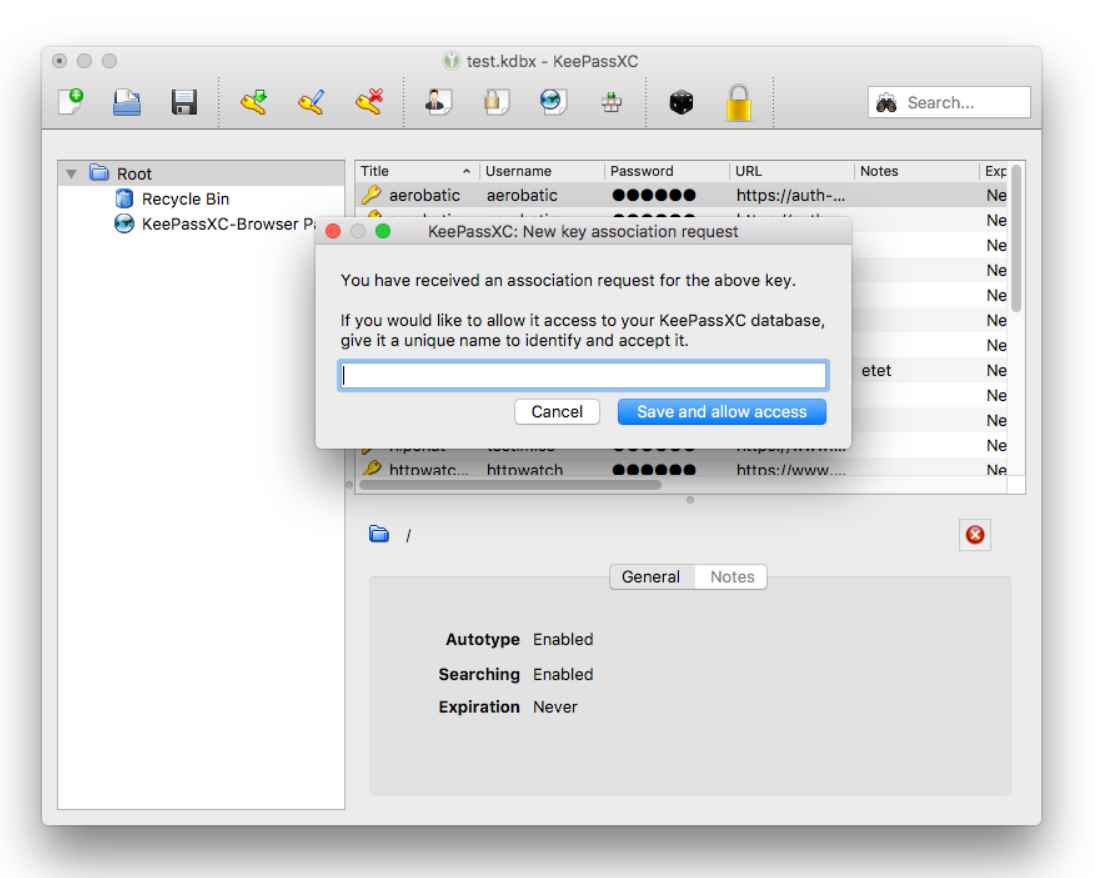
This is a very noteworthy discovery. CVE-2023-35866 is the name of the flaw that was found in KeePassXC not too long ago. An open-source password manager that works with Windows, macOS, and Linux platforms, KeePassXC is available for download. It serves as a repository for a wide variety of sensitive information, such as usernames, passwords, URLs, files, and even personal notes, among other things. Your data, which are encrypted and stored in an offline file, may be kept anywhere, from a local folder on your desktop to solutions that are hosted on the cloud. The platform allows for effective administration via the provision of user-defined titles, icons that may be customized, and a system of groups. A built-in search tool that supports complex pattern searches ensures that any record in the database may be accessed quickly at any time. In addition, KeePassXC is equipped with a versatile password generator that is capable of conjuring up a secure combination of characters or passphrases that are simple to remember.
The worrying ease of access is at the heart of the CVE-2023-35866 vulnerability. Within the context of an authenticated KeePassXC Database session, a local attacker has the ability to change the database security settings. This includes modifying the settings for the master password as well as the settings for the second factor of authentication without it being necessary to authenticate these changes.
Surprisingly, it is not necessary to get confirmation in order to export the database or make changes to the master password. After gaining access to the system either locally or remotely, a potential threat actor would be able to fast export the whole database or change the password without coming across any obstacles along the way that would prevent them.
The following are some of the possible steps that may be taken in order to improve KeePassXC’s existing safety features and close the existing security hole:
Confirmation of the Master Password Whenever any changes are made to the security settings, it is essential to implement a required confirmation of the master password. Only authorized users who are in possession of the master password and know how to enter it will be able to make changes to essential security settings if the master password has to be entered.
Confirmation of Second-Factor Authentication It is recommended, if possible, to include a need for second-factor authentication confirmation when making changes to the security settings of an organization. This might involve the usage of a physical key or one of the other 2FA techniques. Only those who have the appropriate credentials will be able to change the security settings after completing this step since it adds another degree of authentication to the process.
In light of this, the hardworking team behind KeePassXC has given their word that the problem would be fixed in the next version of KeePassXC, which is now under development.

Working as a cyber security solutions architect, Alisa focuses on bug bounty and network security. Before joining us she held a cyber security researcher positions within a variety of cyber security start-ups. She also experience in different industry domains like finance, healthcare and consumer products.
