Although Cisco recognized the detection of 68 vulnerabilities in various router models, the company announced that these flaws will not be corrected since vulnerable devices have reached the end of their lifetime, with the December 1, 2020 update being the last that these devices received.
The affected routers are the V110W, RV130, RV130W, and RV215W models, designed for small and medium businesses: “Small Business routers have begun the process of ending their lifespan. We recommend that users consult notices related to these products,” the Cisco alert mentions.
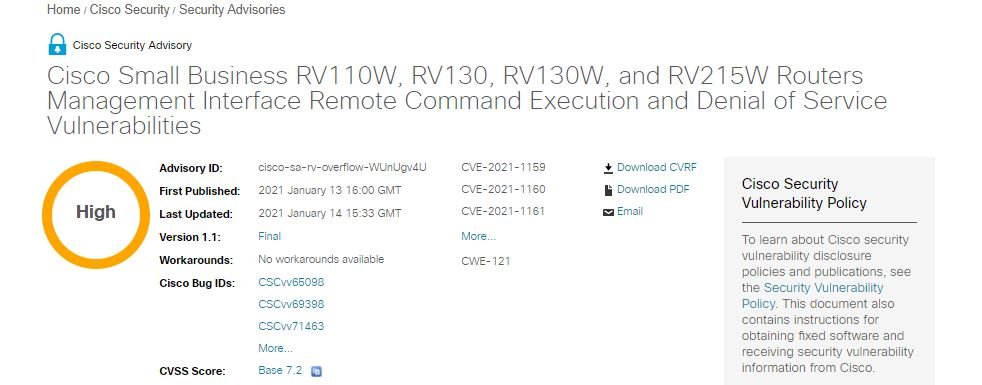
Reported security flaws exist because user-provided entries in the web management interface of these routers are not validated correctly, allowing HTTP requests specially designed to exploit vulnerabilities to be sent.
Threat actors launching successful attacks could execute arbitrary code with root user privileges on the target system, although attacks require valid administrator credentials.
In its security alert, Cisco also mentions that a threat actor could exploit flaws to force a reboot of affected devices, leading to a denial of service (DoS) condition. The Cisco security team reports that the web management interface can be accessed from LAN or over a WAN connection as long as remote management is enabled; it should be noted that this function is disabled by default.
Cisco also issued 18 other warnings detailing medium severity errors on Webex, ASR 5000 routers, Proximity Desktop for Windows, NFV Enterprise Infrastructure Software (NFVIS), Finesse, 8000 Video Surveillance IP Cameras, Firepower Management Center (FMC), DNA Center, Unified Communications Products, CMX API Authorizations, and AnyConnect Secure Mobility Client.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
