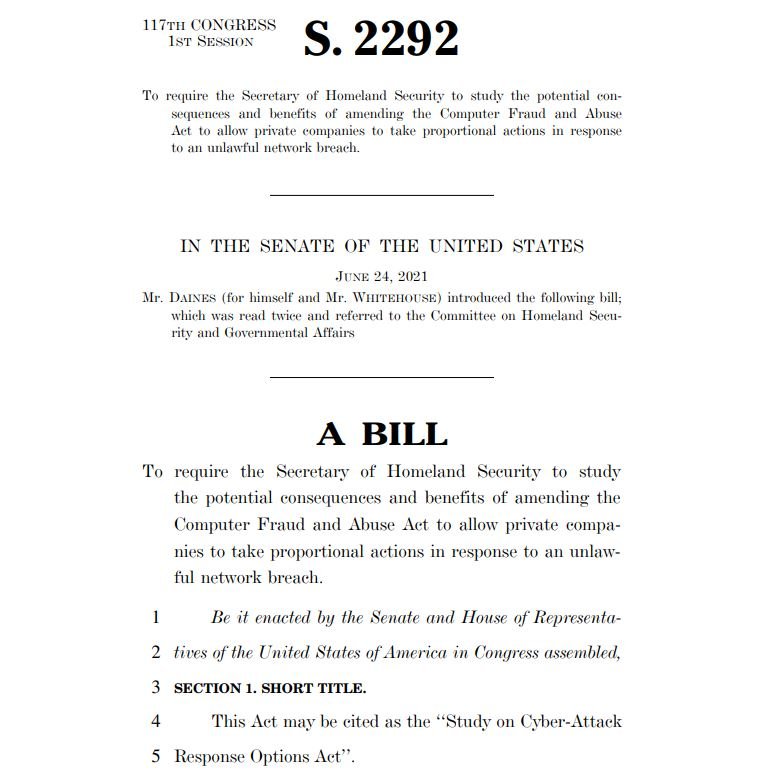
In mid-2021, U.S. Senators Sheldon Whitehouse and Steve Daines presented a document titled “Study on Cyber-Attack Response Options Act”, as a way to request (or require) the Department of Homeland Security (DHS) to assess the potential risks and benefits involved in allowing private companies to launch cyberattacks against cybercriminal groups, as a form of response to cybersecurity incidents.
In other words, the congressmen were proposing to empower institutions in the U.S. to retaliate against threat actors, bringing the right to self-defense to the world of technology. DHS must submit a detailed report on why a private organization may, or may not, legally launch hacking attacks, considering the impact of this decision on national security and proposing possible limits to this practice.
This is a position shared by some government representatives. John Demers of the U.S. Department of Justice (DOJ) testified shortly after this bill was introduced, mentioning that the DOJ planned to take a proactive stance in the fight against cybercrime, rather than simply waiting for attacks on U.S. public and private institutions to arrive.
While many experts see the right to self-defense against hacking as a great option for combating cybercrime, there are many very good arguments against this idea. A few months ago, cybersecurity specialist Jen Ellis mentioned that, among the multiple drawbacks, the main one is the lack of certainty about the real authorship of an attack: “It is virtually impossible to know with certainty if an attack has been attributed to the right threat actor,” she says.
Another potential consequence of legalizing this practice, dubbed “hack back”, is the increase in the sophistication of hacking groups, believes Dirk Schrader of New Net Technologies: “More advanced hacking groups will increase their efforts to hide their traces, and hacking attempts could serve as a hook to attract larger targets.”
It remains to be seen whether this proposal will become law, but the discussion on it remains active. For Ellis, it is preferable for organizations to focus on raising employee awareness, which allows them to minimize exposure to cyberattacks, in addition to adhering to other security measures, including regularly updating their software products, applying user identity management and using strong passwords.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
