A report by the security firm Lookout mentions that a group of scammers managed to trick more than 90,000 users of Android devices into buying fake apps for cryptocurrency mining tasks. These criminals used at least 172 apps divided into two families named As BitTransit and CloudTransit and offered alleged virtual asset mining services in the cloud.
While it’s easy to spot the malicious intentions behind some of these apps, the report mentions that at least 25 of these tools were available on the official Google Play Store platform, while most could be downloaded from third-party sites.

Needless to say, none of these fraudulent apps had functions for the mining of cryptocurrency, but it was digital scrap that was sold to unsuspecting users without providing a single one of the advertised services.
In total, the threat actors obtained $300,000 USD for the sale of these fraudulent apps, in addition to another $50,000 USD for the sale of alleged updates. The Lookout report mentions that affected users never suspected that it was all a scam because these apps didn’t even contain malware: “These are simple empty shells created to attract users interested in investing in cryptocurrency.”
In addition to the sale of the APK and the supposed updates, cybercriminals offered users all kinds of additional services, which could be paid for by bank transfers or even with cryptocurrency transactions. These apps support transfers in Bitcoin and Ethereum, so many users relied without hesitation on their investment.
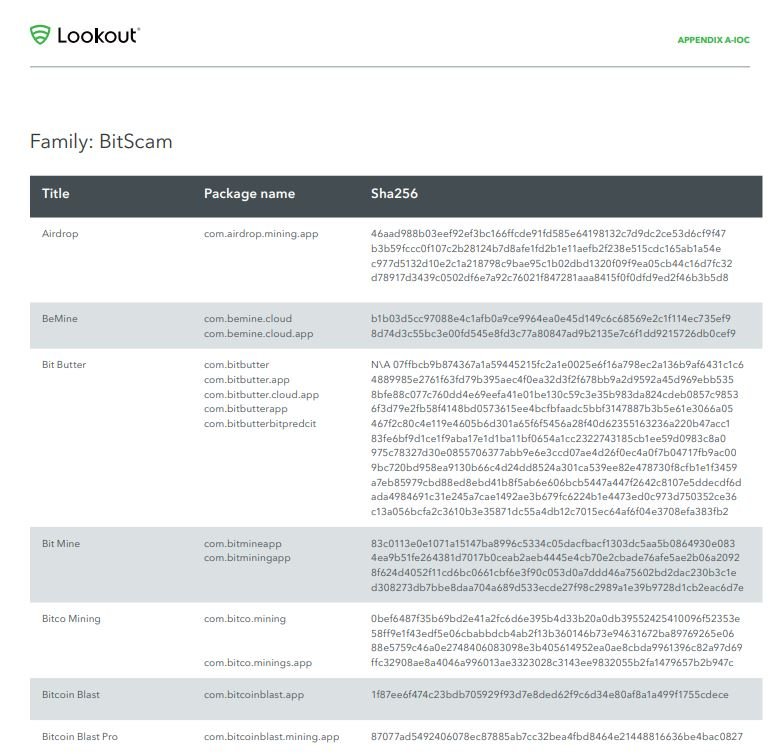
Google has already removed from the Play Store all apps linked to this campaign, however, researchers mention that most of these fraudulent tools are still available on unofficial websites and app stores. If you have downloaded any of these apps you are advised to remove it from your device and cut off any communication with the fraud operators. If it is your interest to invest in cryptocurrency, you are advised to approach a reliable specialist to avoid falling for such malicious campaigns; the Lookout report includes a list of all the fraudulent apps identified so far.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
