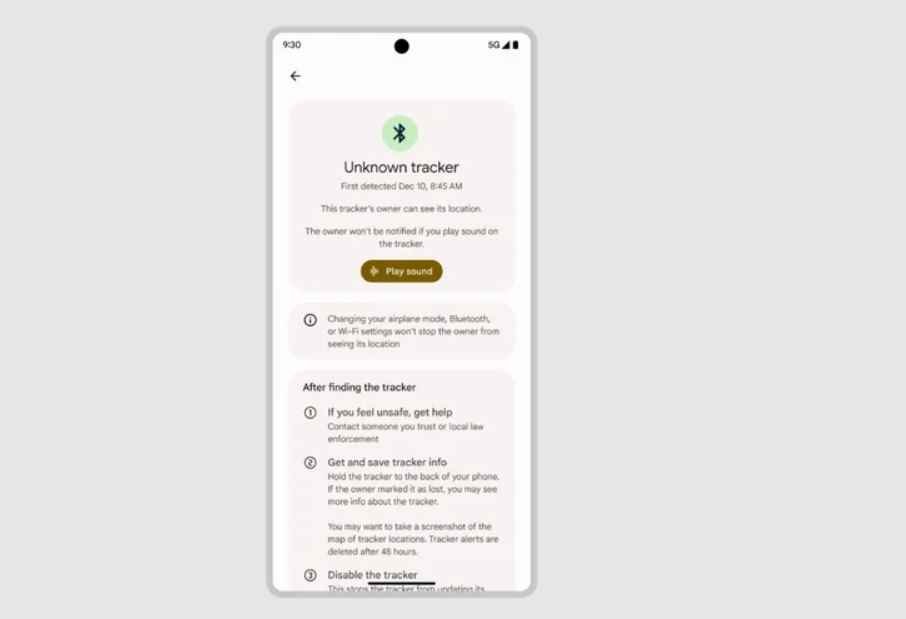
Android users can now detect Bluetooth trackers, such as AirTag, without the need for an app
In the month of May, both Google and Apple made the announcement that they were going to work together to stop intrusive monitoring using AirTags and other devices of aRead More →