Fan of Splunk SIEM? You should be worried as it can now be exploited to leak your company data
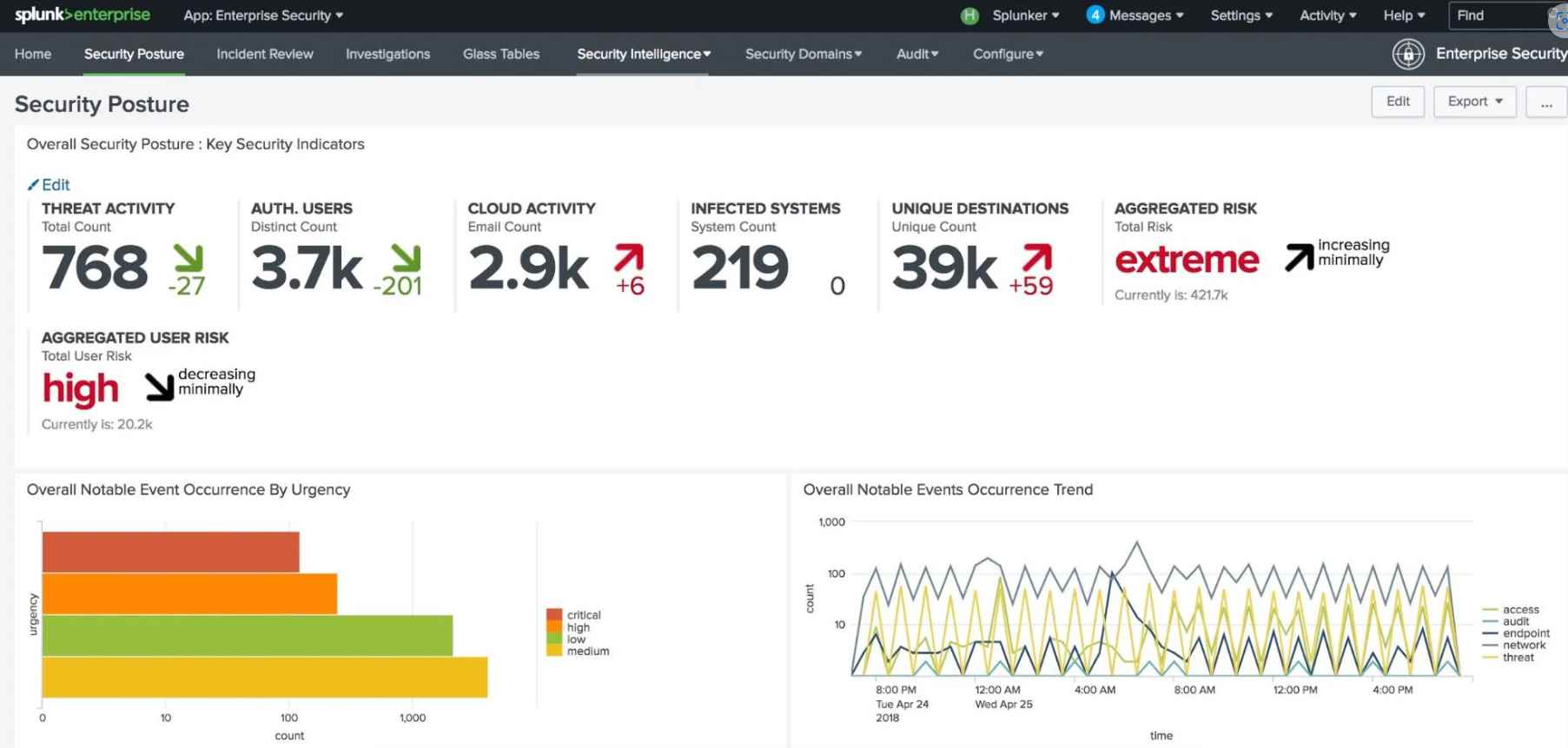
Splunk is one of the Security Incident and Event Management (SIEM) tools that is used the most all over the globe. Splunk has the capability to gather logs of allRead More →