Hackers find new way to hack Discord admins via bookmarks and empty their crypto wallets
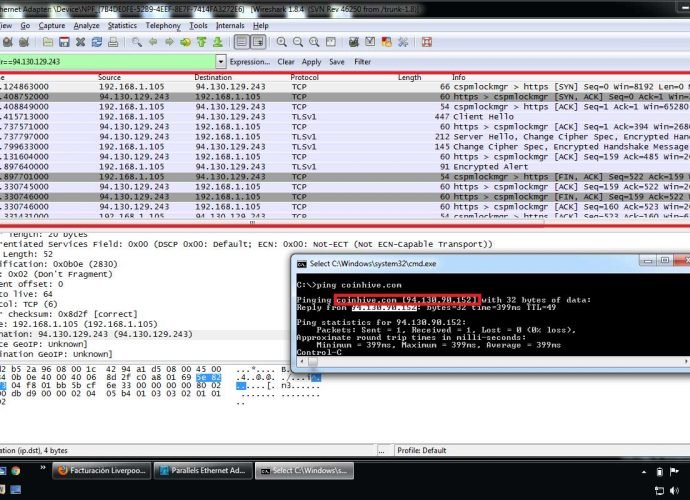
This past month, a number of Discord groups that were centered on cryptocurrencies were compromised after the administrators of such communities were duped into executing malicious Javascript code that wasRead More →