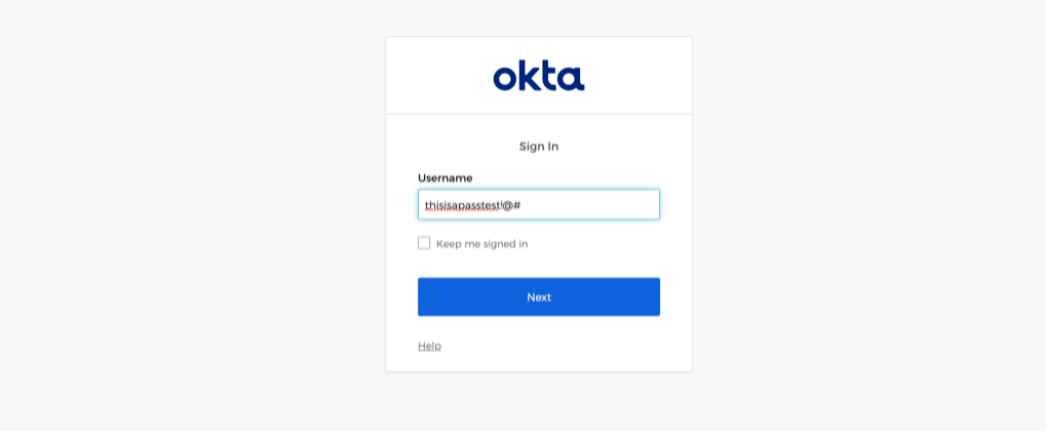
Famous 3 Hacking and Fake News Generation Tools Used by the Russian Military
Large-scale preparations by Russian military and intelligence services to use their cyberwar capabilities in misinformation campaigns, hacking operations, critical infrastructure disruption, and Internet control have been revealed by the disclosureRead More →