Mobile hacking is advancing by great strides, and it’s getting easier and easier to find a tool powerful enough to extract information from a compromised device. This time, the experts of the cyber security course of the International Institute of Cyber Security (IICS) will show you how HaxRat works, a hacking tool for mobile devices available to almost any user.
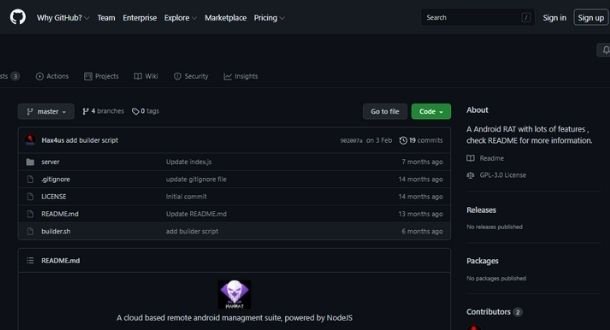
HaxRat is a cloud-based android remote control script developed with Node.js with which it is possible to block calls on the target device, in addition to activating the microphone, intercepting notifications and spying on files in the device’s memory.
As usual, we remind you that this article was prepared for informational purposes only, so IICS is not responsible for the misuse that a person may give to the information contained herein.
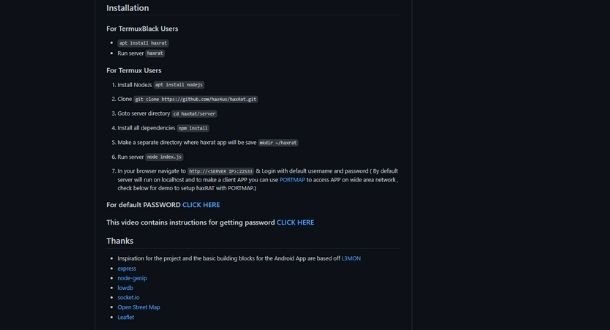
Installation
To start using HaxRat, enter the following commands to the Kali Linux terminal:
$ apt install nodejs git
$ git clone https://github.com/hax4us/haxRat.git
$ cd haxRat/server
$ npm install
$ mkdir ~/haxrat
Using the tool
Next, the experts of the cybersecurity course recommend entering the following commands:
$ node index.js
In response we will get all the information from the compromised system. Remember to use HaxRat only in controlled environments and with the authorization of the target user.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.