Sophos security teams announced the fix of a critical vulnerability in authentication software running on Universal Threat Manager (UTM) devices. The vulnerability was described as a SQL injection bug in the Mail Manager component, which would allow threat actors to execute malicious code on affected devices.
UTM appliances bundle a variety of security features into a single computer, operating as network firewall, intrusion prevention, gateway antivirus, web proxy technology, and other security features. These devices are popular because of their ease of management, albeit with the disadvantage of creating an attractive entry point for hackers.
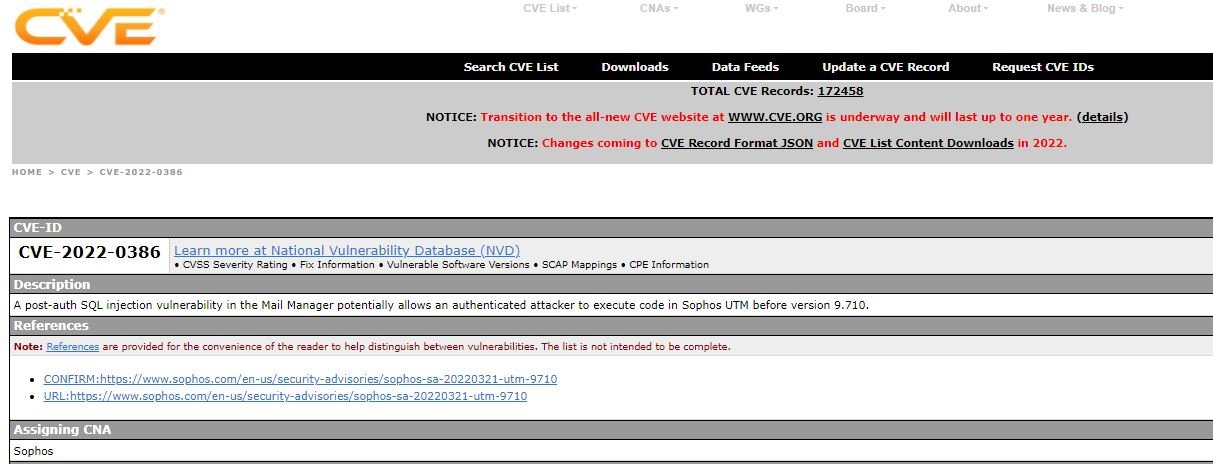
Tracked as CVE-2022-0386, the flaw was identified by Sophos during an internal testing period and should be addressed by updating UTM devices to version 9.710, released a few weeks ago. In its most recent update, Sophos recommended its users update as soon as possible to mitigate the risk of exploitation.
This update also addresses a bug by removing an outdated SSL VPN client, in addition to fixing a minor security vulnerability tracked as CVE-2022-0652 and that could result in writing password hashes to system log files.
Although they cannot be exploited directly, these password hashes were left in places where they could potentially be collected by a malicious actor and employed in brute-force attacks. So far, no exploitation attempts have been reported derived from these vulnerabilities.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
