The developers of Apache Storm, an open-source real time data analysis platform, announced the correction of two vulnerabilities whose exploitation would allow remote code execution (RCE) attacks to be deployed. The flaws were reported by experts at GitHub Security Labs.
The first of the two flaws lies in one of the functions of Nimbus, the main component of Storm. The getTopologyHistory function takes a username argument and concatenates it into a shell command without sanitizing it; threat actors could take advantage of this argument to send commands from the operating system to the Apache server.
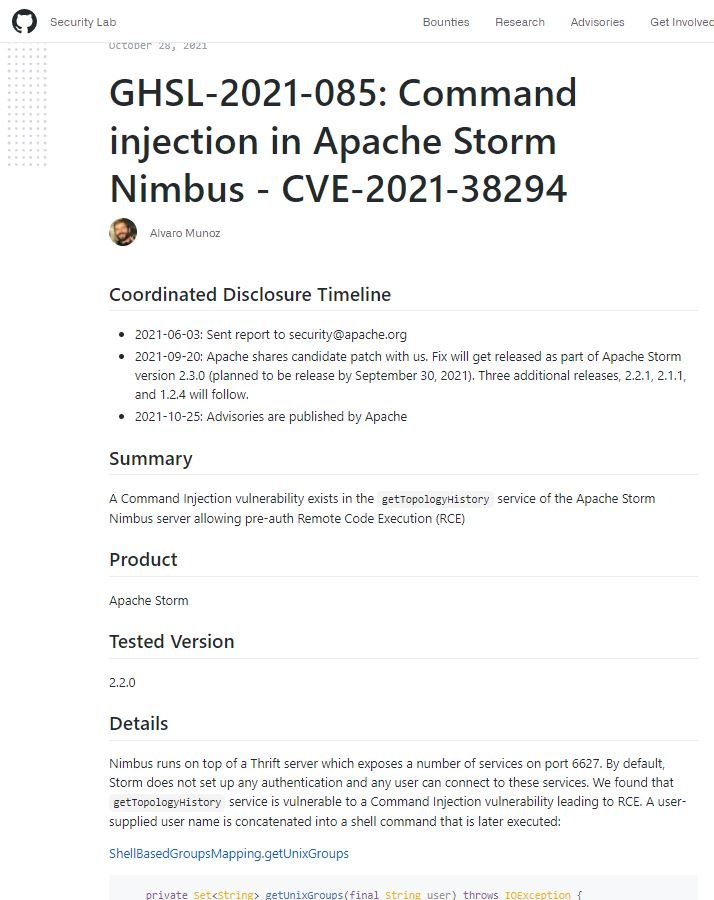
When called directly through the Nimbus Thrift port, the feature does not require any special privileges from users, leading to a pre-authentication RCE scenario. A proof of concept (PoC) to exploit the bug is also available.
The second flaw lies in the Storm monitoring service, running on top of a Netty server. The researchers discovered that the incoming server pipeline (the different controllers that process incoming network packets) uses an object analyzer vulnerable to an insecure deserialization scenario, which could be exploited by threat actors to send a malicious object to be executed on the server.
In this regard, the member of the Apache Storm Project Management Committee Derek Dagit mentioned that failures can be exploited to compromise Storm installations with predetermined configurations, so it is essential to update as soon as possible. On the code injection failure, Dagit mentions that the key taker is to treat any code that invokes an interpreter with scrutiny.
This group of flaws can also be taken as a reminder that authentication should be applied as early as possible in the data processing chain to reduce the chances that unauthenticated users could trigger potential vulnerabilities in the code.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
