The U.S. Cybersecurity and Infrastructure Security Agency (CISA) issued a security alert regarding a set of vulnerabilities that would allow malicious hackers to take control of Illumia genetic analysis devices. According to the report, the flaws reside in Illumia Local Run Manager, used in sequencing instruments for clinical diagnosis.
The Agency mentions that flaws can be exploited to execute arbitrary code, manage to traverse directories, upload arbitrary files, connect without authentication and perform Man-in-The-Middle (MiTM) attacks, among other hacking variants.
There are three most severe failures discovered, receiving a score of 10/10 according to the Common Vulnerability Scoring System (CVSS). Tracked as CVE-202215-17, CVE-2022-1518, and CVE-2022-1519, the flaws would allow for remote code execution (RCE) attacks, data upload from outside the directory structure, and arbitrary file upload.
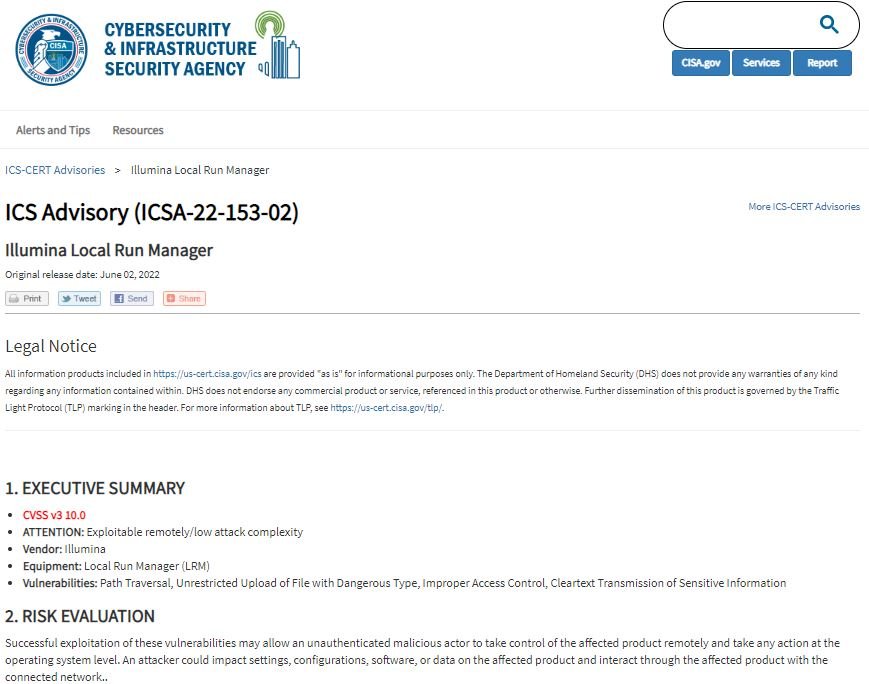
A fourth bug was tracked as CVE-2022-1521 and received a CVSS score of 9.1/10. Apparently, this flaw exists because, by default, LRM does not present authentication or authorization, which can allow an attacker to inject, intercept, or manipulate sensitive data.
Finally, CVE-2022-1524 received a score of 7.4/10 and exists due to the absence of encryption in TLS in LRM v2.4 and earlier, allowing threat actors to deploy MiTM attacks and intercept sensitive data.
Illumia products identified as vulnerable to these attacks include the NextSeg 550Dx and MiSeg Dx in vitro diagnostic systems, and research instruments the NextSeq 500, NextSeq 550, MiSeq Instrument, iSeq 100 and MiniSeq Instrument.
The company acknowledged the errors upon receiving the report and announced the release of security patches, which should have already been issued. In early May, the company notified its customers in the healthcare industry about the risks of remote code execution, recommending taking some additional security measures.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, and information technologies.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
