The prestigious Italian fashion house Ermenegildo Zegna has confirmed that it was the victim of a ransomware attack that severely affected its operations and could be fixed without paying a single dollar to hackers.
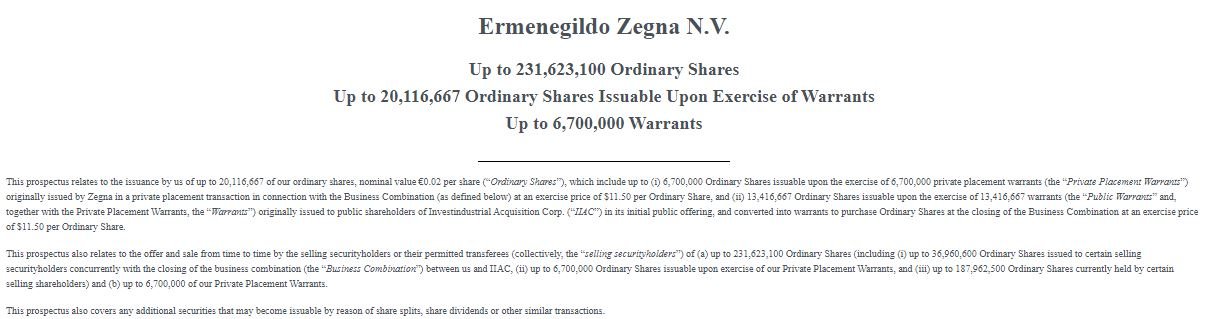
The incident occurred in August 2021, although at the time the company only mentioned one security incident without providing further details. It wasn’t until this week that, filing a U.S. Securities and Exchange Commission (SEC) Form 424B3, Ermenegildo Zegna described the incident as a ransomware attack that affected most of his systems, prompting the leaking of some internal documents.
This was already a known fact, since the RansomExx ransomware group claimed responsibility for the attack just days after the incident, publishing on hacking forums data obtained from the company’s systems. In its report, the company assures that at no time was it shown any intention to cooperate with the attackers: “We refused to participate in discussions related to the payment of the ransom, so the responsible parties published certain accounting materials extracted from our systems.” Zegna ensures that the information exposed does not pose a risk to its customers, employees and operations.
After the attack, Zegna began restoring its IT systems from backups, trying to rescue multiple servers, third-party cloud providers, and all sorts of software implementations without negotiating with hackers. In addition, the company ensures that periodic security assessments were implemented, which has significantly decreased its exposure to the most common cyberattack variants.
Thousands of companies have chosen to pay hackers after a ransomware attack in order to get back up and running as quickly as possible. Law enforcement agencies and security firms around the world recommend against doing so, as this only contributes to funding other attacks and there is no guarantee that hackers will keep their end of the bargain.
Faced with this, hacking groups began to use the tactic of double extortion, which consists of extracting information before encrypting the affected systems, threatening victims with leaking this data in hacking forums in case they refuse to pay the ransom.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.
He is a cyber security and malware researcher. He studied Computer Science and started working as a cyber security analyst in 2006. He is actively working as an cyber security investigator. He also worked for different security companies. His everyday job includes researching about new cyber security incidents. Also he has deep level of knowledge in enterprise security implementation.
