The Linux kernel has a framework known as netfilter that enables a variety of networking-related actions to be performed in the form of individualized handlers. This may be accomplished by filtering incoming network packets. The functionality required for directing packets through a network and preventing packets from reaching sensitive locations within a network is provided by Netfilter, which provides a variety of functions and operations for packet filtering, network address translation, and port translation among other things. Netfilter offers these features.
The vulnerability in the Netfilter subsystem has been referred to as a stack-based buffer overflow by its developers. An authorized attacker might exploit this issue to get elevated privileges as root if the attacker executed a program that had been carefully written for the purpose. All versions of Linux from 5.5 up to 6.2-rc3 are susceptible to the vulnerability.
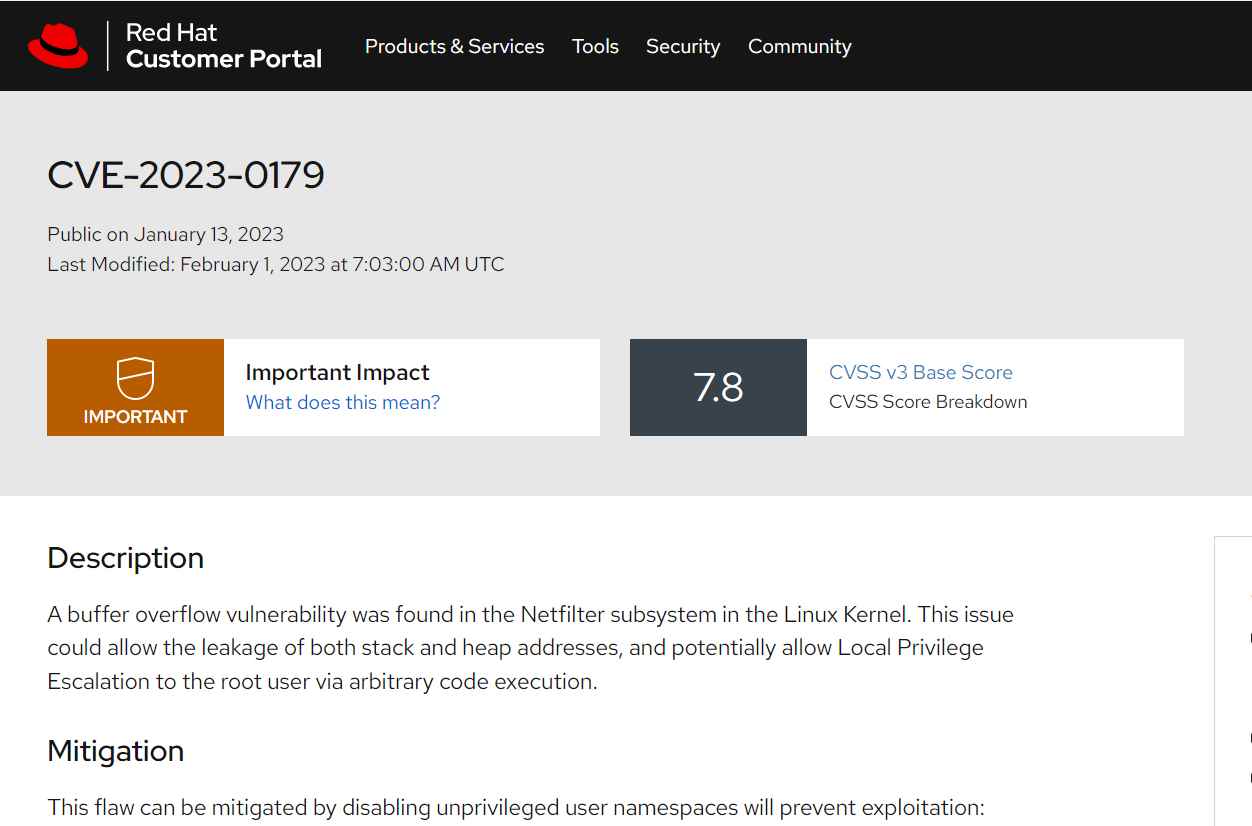
The exploitation might result in the disclosure of both stack and heap addresses, as well as the possible elevation of a user’s local privileges to those of the root user via the execution of arbitrary code.
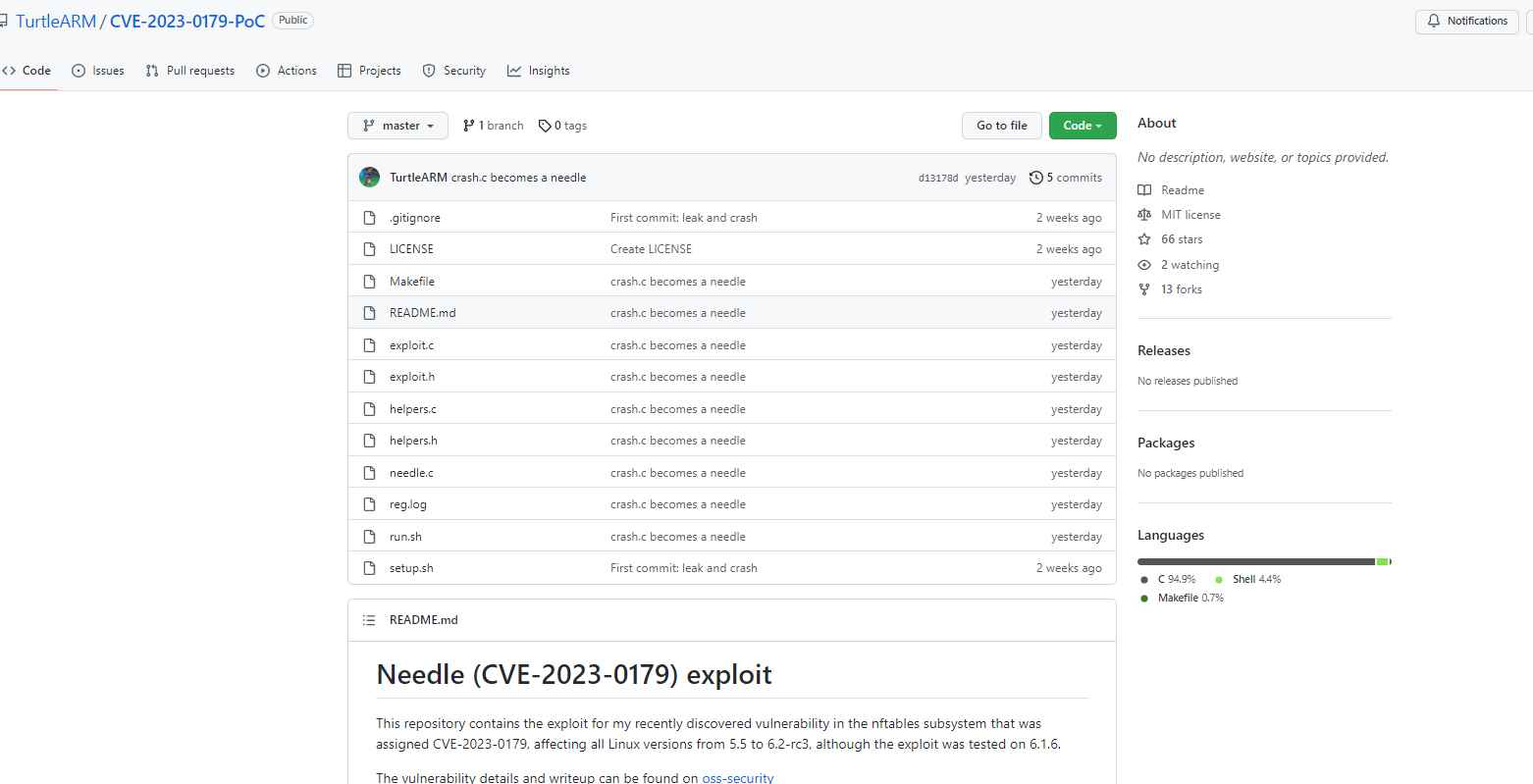
When the exploit is run, it will log in as a user with no special permissions and use the rule add payload function to add a nft payload expression. This expression, when evaluated, will cause the stack buffer to overflow, which in turn will cause the registers to be overwritten.
The proof-of-concept attack for CVE-2023-0179 has been successfully tested against the unpatched version of the Linux kernel (6.1.6). The vulnerability results in the creation of a new user account with the username needle and the UID 0.
It is strongly suggested that users immediately upgrade their Linux servers and implement the fixes for distributions as soon as is humanly practicable. It is also advised that they only let trustworthy people access local systems and that they constantly check the systems that have been compromised.
If you are unable to apply a fix for this flaw, you may avoid exploitation by turning off namespaces for users without privileges.
sysctl -w kernel.unprivileged userns clone = 0 is the command you need to enter.
Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.
