Who is behind the hacking of the national elections in Ecuador?
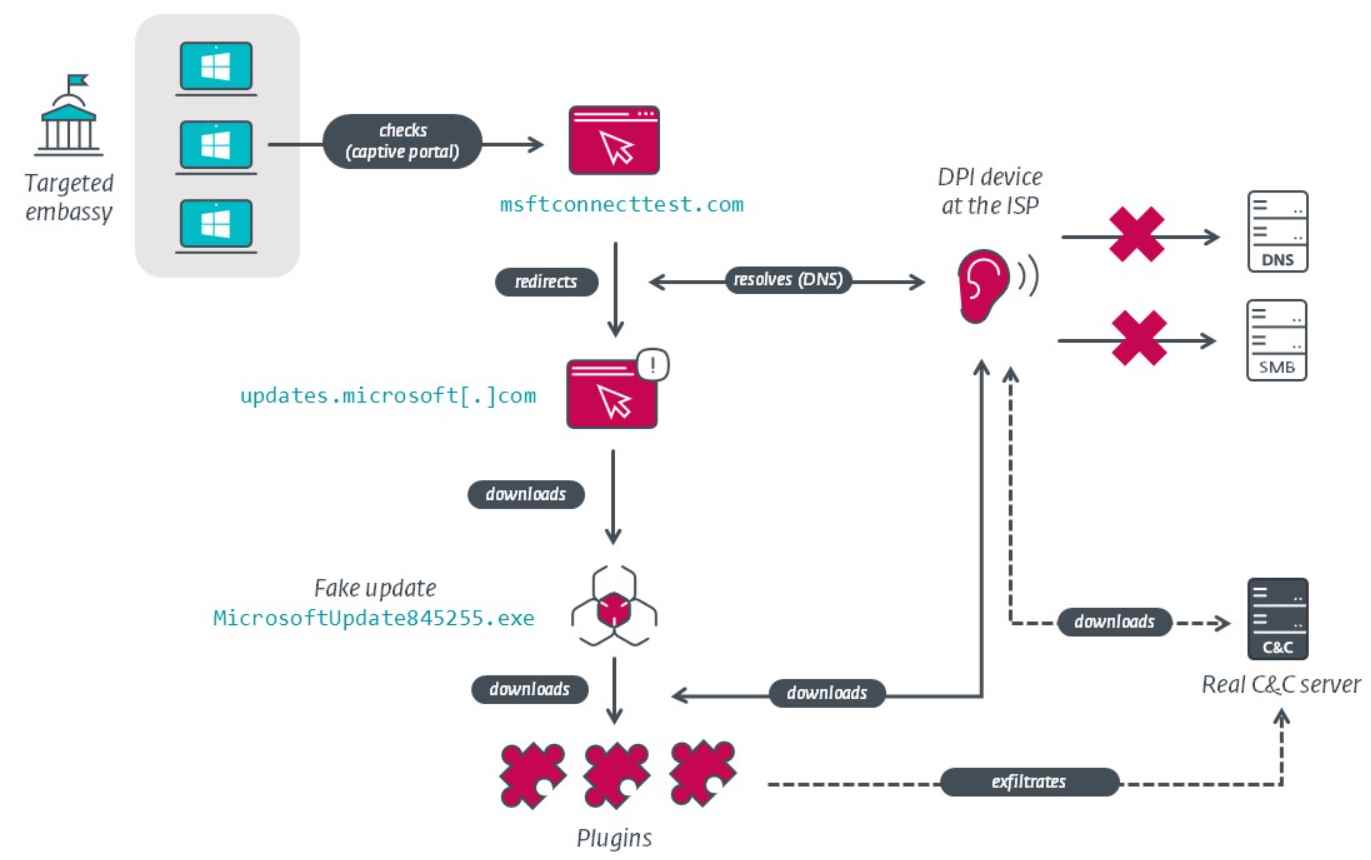
The Ecuadorian national election, which took place on Sunday, was hampered by problems with internet voting for residents residing outside of the country. The Ecuadorian electoral office blamed these problemsRead More →