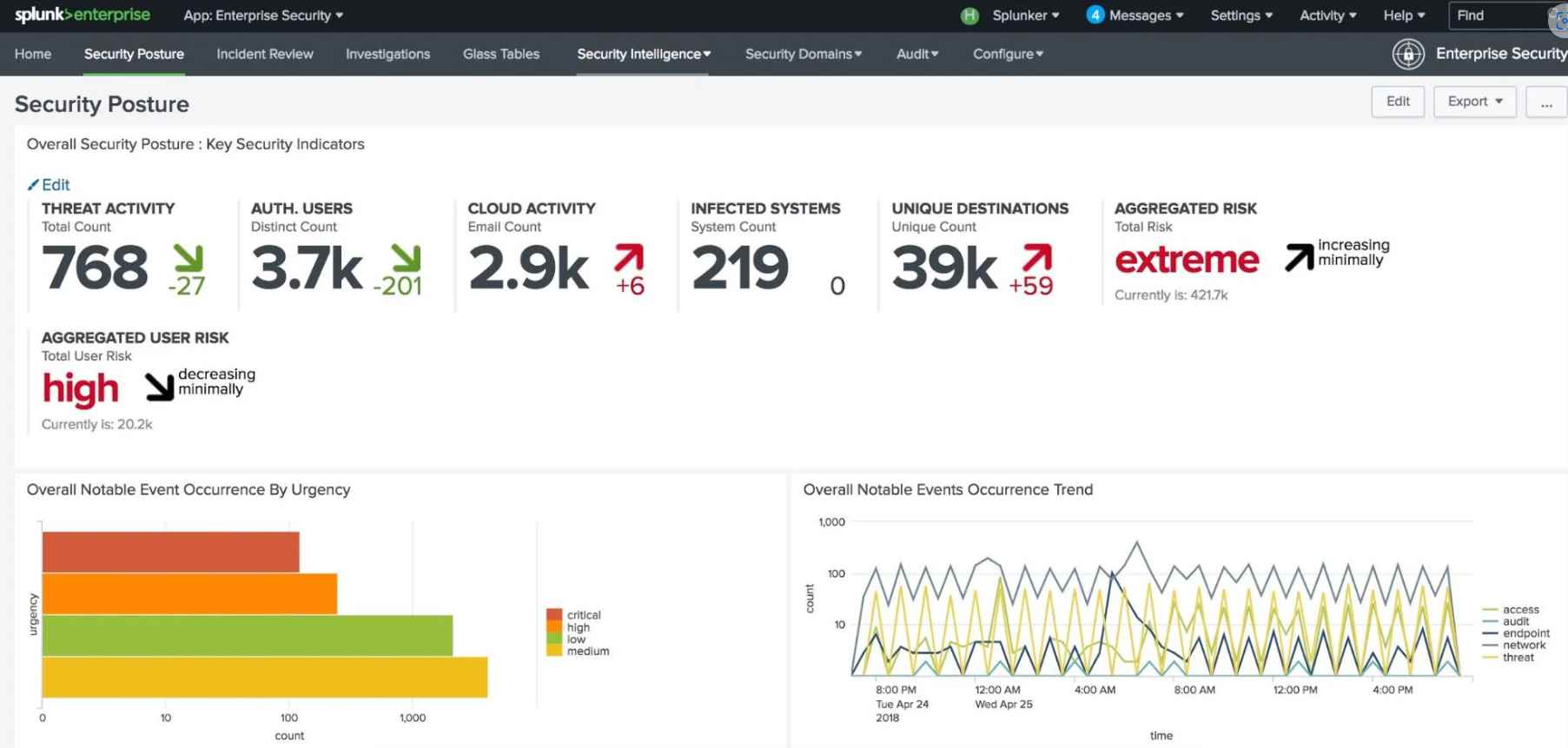
This new DDoS attack prevention technique has a 99% accuracy rate
In comparison to the approaches that are now used, the detection capabilities of a typical internet attack have been much improved thanks to the work done by scientists.Keeping a closeRead More →