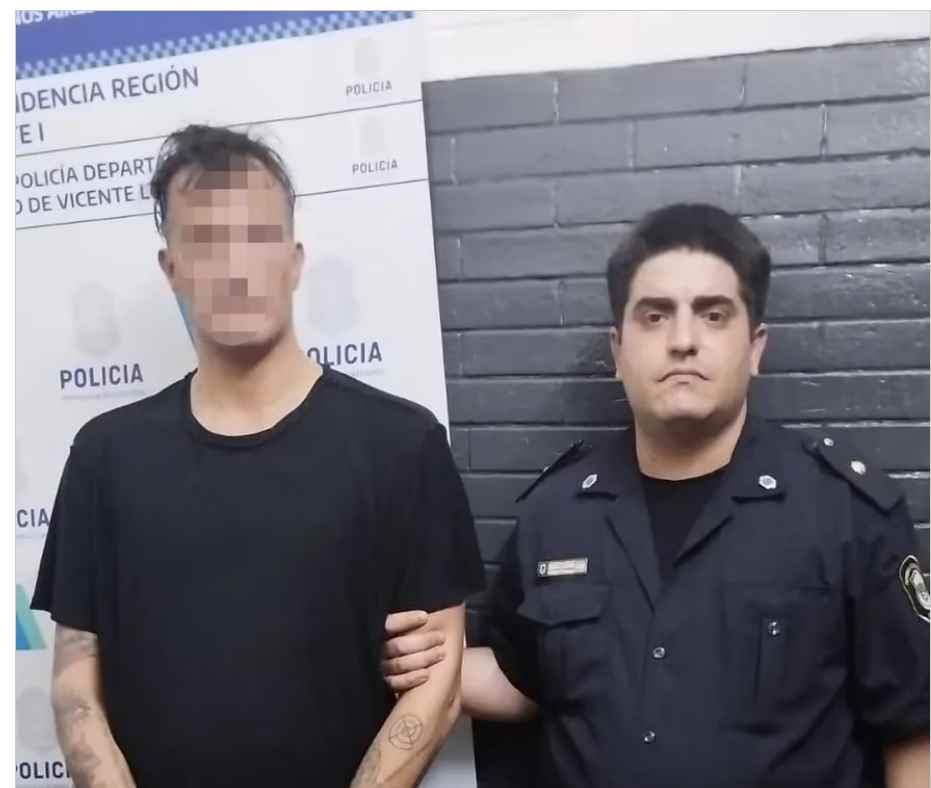
How the famous Argentinean Scammer ” El Hacker or C14″ was tracked and arrested by Police
He resided at Saint Thomas Country Club. He then moved to El Rebenque, a gated enclave near Canning, where he paid $2,000 a month. He drove an Audi and MiniRead More →