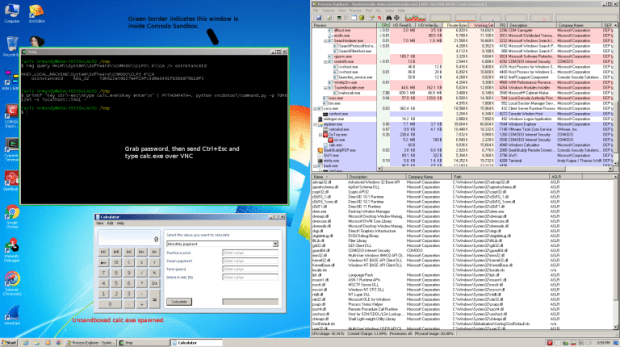
New Industry Timelines (30,60,90 Days) Released for Vulnerability Disclosure for Critical, High and Medium Severity Flaws
To encourage manufacturers to provide better security upgrades, the Zero Day Initiative (ZDI), a vulnerability reseller, has shortened its disclosure deadlines for incomplete fixes. Security company Trend Micro’s ZDI isRead More →